Here's my copy-paste from the DSi stuff.
I present to you: "DSi Encryption Put In Perspective", also known as "I Love Crushing People's Dreams".
The DSi uses 128-bit encryption (IIRC).
How do you break it? You find
the correct encryption key.
How many encryption keys are there? 2 (binary, a bit) to the 128th power (number of bits), divided by 8 (8 bits in a byte).
That's so many that the calculator that comes with windows (at least XP) can't even display the number without reverting to scientific notation.
128-bits is...
340,282,366,920,938,463,463,374,607,431,768,211,456 possible values in binary.
However, Since there's 8 bits in a byte, you divide 128 by 8 and get 16. That's 16 bytes, 16 characters.
That's 18,446,744,073,709,552,000 possible values, ranging from 0x0000000000000000 to 0xFFFFFFFFFFFFFFFF. Eighteen quintillion possible keys.
The actual number is a bit less less since a key will be a certain number of digits and be designed to not have repeating segments, but this puts it in perspective.
Let's say that you have a computer program which can try 50,000
unique keys a second.
That's 3,000,000 keys a minute.
180,000,000 keys in an hour.
4,320,000,000 keys a day.
1,576,800,000,000 keys in one year.
It would take 11,698,848 years to try all the keys at that speed.
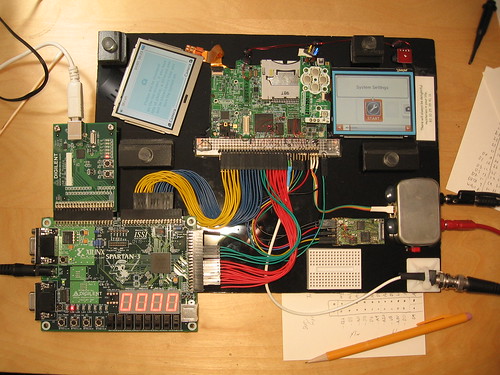
So wait, how do they break other systems? If you can get a direct copy of the encrypted data and compare it to a copy of the unencrypted data (as well as view the data as it's transmitted around the DSi's internals), that goes a long way towards figuring out the key without having to try all possible combinations. You'll be able to find the key without all the guessing! The problem is you'd need to take a DSi apart and fuck with it's insides while it's on to try to get a copy of the data while it's unencrypted (since the DSi will unencrypt what it needs on the fly in order to use it), and usually when you're done with that the DSi's pretty broken and in no shape to game, or even to be experimented on a second time...
http://www.flickr.com/photos/micahdowty/sets/72157621023570420/
This process can be hampered by the internal design of the system, so you may need to take apart many systems before you even figure out how to read some of the data, let alone get a full copy of it, and last I checked DSi's don't cost $5...