How did you get it working dude? was you getting similar issues to me by any chance? I keep getting result code: c8a0802b. also do you just put 2 data base files and name them import.db and title.db is that correct?
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Hello,I can get the romfs.bin,exheader.bin,exefs.bin by decrypting the 3ds rom,but where's the code.bin,icon.bin and banner.bin come from?Step1: decrypt the .3ds rom.
I will not explain it in this tutorial, as it is explained a couple of times around the forum. (http://gbatemp.net/threads/release-3ds_ctr_decryptor-void.370684/)
If you end up with a decrypted romfs.bin, exheader.bin, code.bin (decompressed), icon.bin and banner.bin you did everything correct.
Hello,I can get the romfs.bin,exheader.bin,exefs.bin by decrypting the 3ds rom,but where's the code.bin,icon.bin and banner.bin come from?
Code:
ctrtool -t exefs --exefsdir=exefs exefs.bin --decompresscodeIt was built with SDK 5.x, so probably!
I tried again with -desc app:3 -target t and it worked.
Thanks a lot, it's worked for with with MK7
Tip : If you want to add the game manual (if the game have one) you can extract it with rom_tool -x then add -content XXX-X-XXXX_1_MANUAL.cfa:1:1 to the makerom command
Thank you ,thank you very muchCode:ctrtool -t exefs --exefsdir=exefs exefs.bin --decompresscode
Thanks a lot, it's worked for with with MK7
Tip : If you want to add the game manual (if the game have one) you can extract it with rom_tool -x then add -content XXX-X-XXXX_1_MANUAL.cfa:1:1 to the makerom command
would this mean that we can add other documents such as game guides if they were in the same format as the game manuals?.......................sudeki300
well if you can create a manual i dont see why not.....idk what format the manual is in thoughwould this mean that we can add other documents such as game guides if they were in the same format as the game manuals?.......................sudeki300
You'll have to create the dbs folder.
Thank you.
Does anyone know if Donkey Kong Country Returns work?
but... it didn't workCode:ctrtool -t exefs --exefsdir=exefs exefs.bin --decompresscode
I get stuck in the end, first i do sdmc:/Nintendo 3DS/<id0>/<id1>/dbs/, create de two files, go to management data, your data is not working i press "delete", now you can download for eshop.
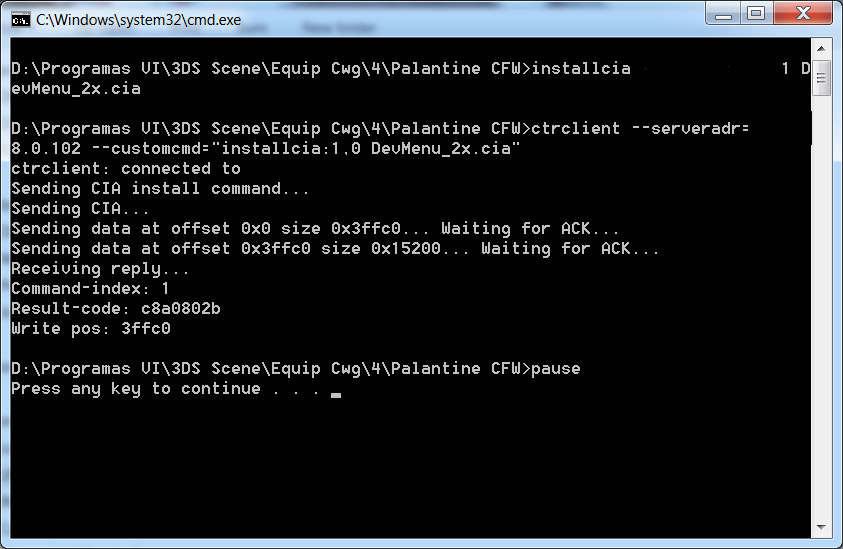
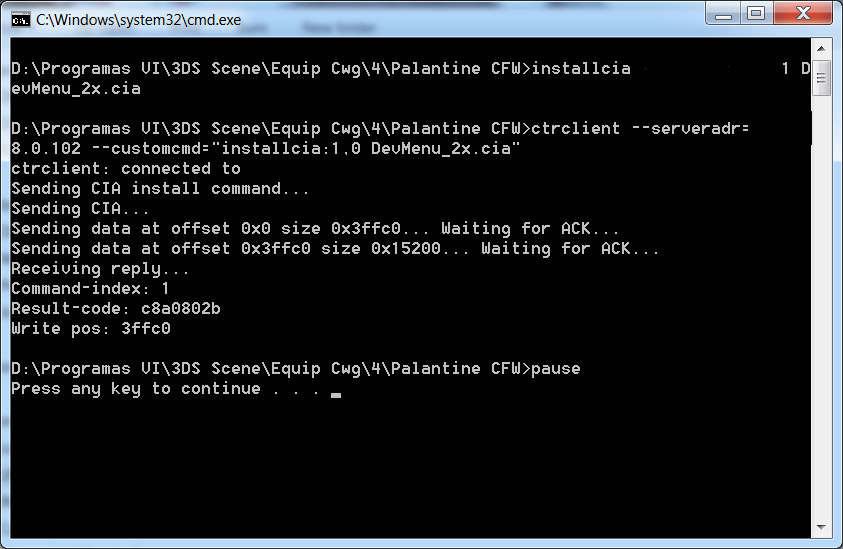
Then trying to install dev_menu (cia), this happends
Thats means that is need to install something from the eshop. The first time appears "uptade 3ds" i choose cancel, the next time only the image above apear.
When i go to the management data, apears a dev_menu slot that ocuppy 4 slots, but when restart the console is not more there.
Some user try to give me a shinny passageway, how to install eshop with other form or something i miss.
Process: Microsd Hombrew 4>Profile SD (Palantine CFW)>Cpu run.bat (image above).
Then trying to install dev_menu (cia), this happends
Thats means that is need to install something from the eshop. The first time appears "uptade 3ds" i choose cancel, the next time only the image above apear.
When i go to the management data, apears a dev_menu slot that ocuppy 4 slots, but when restart the console is not more there.
Some user try to give me a shinny passageway, how to install eshop with other form or something i miss.
Process: Microsd Hombrew 4>Profile SD (Palantine CFW)>Cpu run.bat (image above).
Hi there guays!
First of all thank you so much to all sceners and users that works for the comunity.
Here is the question:
-I want to convert .3ds to .cia,I drop the .3ds file in ctrkeygen.py and a 1kb ncchinfo.bin was generated.I paste this into root of sd card,and when I launch the exploit,I recived this:
''Nothing to do:-1''
Where is the fail?
Thank you so much guys
First of all thank you so much to all sceners and users that works for the comunity.
Here is the question:
-I want to convert .3ds to .cia,I drop the .3ds file in ctrkeygen.py and a 1kb ncchinfo.bin was generated.I paste this into root of sd card,and when I launch the exploit,I recived this:
''Nothing to do:-1''
Where is the fail?
Thank you so much guys
maybe someone has said this already, but, from what i understand, the dev menu is installed to an emunand... right?
has anyone tried flashing that emunand to their nand, to make it an easier process, so you don't need to load up the emunand each time you want to install something?
has anyone tried flashing that emunand to their nand, to make it an easier process, so you don't need to load up the emunand each time you want to install something?
well it is installed to your sd card. and actually someone tried flashing their emunand to realnand. it boots but the devmenu wont work. this is logical as it the exploit is needed to bypass some checksmaybe someone has said this already, but, from what i understand, the dev menu is installed to an emunand... right?
has anyone tried flashing that emunand to their nand, to make it an easier process, so you don't need to load up the emunand each time you want to install something?
well it is installed to your sd card. and actually someone tried flashing their emunand to realnand. it boots but the devmenu wont work. this is logical as it the exploit is needed to bypass some checks
ok so it doesn't work since checks have to be bypassed, that makes sense i guess, thanks
seems like a faulty ncchinfo.bin, maybe to remake it will help. (or if jsut the index number is wrong, open it with a hex editor and change te first byte from 00 to ?, where ? is the amount of xorpads you want to generate)Hi there guays!
First of all thank you so much to all sceners and users that works for the comunity.
Here is the question:
-I want to convert .3ds to .cia,I drop the .3ds file in ctrkeygen.py and a 1kb ncchinfo.bin was generated.I paste this into root of sd card,and when I launch the exploit,I recived this:
''Nothing to do:-1''
Where is the fail?
Thank you so much guys
You can have a try,but I think it wouldn't workmaybe someone has said this already, but, from what i understand, the dev menu is installed to an emunand... right?
has anyone tried flashing that emunand to their nand, to make it an easier process, so you don't need to load up the emunand each time you want to install something?
does this cfw stuff modify the actual 3ds at all or only the emunand?
if it does modify the actual 3ds, has anyone that can restore their nand tried to update after installing the mod? does the update still work like normal or does it brick/fail to install kind of like a bad wii u mod?
if it does modify the actual 3ds, has anyone that can restore their nand tried to update after installing the mod? does the update still work like normal or does it brick/fail to install kind of like a bad wii u mod?
yeah, someone already tried and it didn't work. I guess the system processes are patched in RAM instead of the actual files.maybe someone has said this already, but, from what i understand, the dev menu is installed to an emunand... right?
has anyone tried flashing that emunand to their nand, to make it an easier process, so you don't need to load up the emunand each time you want to install something?
Similar threads
- Replies
- 123
- Views
- 26K
- Replies
- 29
- Views
- 3K
- Replies
- 45
- Views
- 13K
- Replies
- 0
- Views
- 1K
Site & Scene News
New Hot Discussed
-
-
26K views
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other... -
20K views
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we... -
19K views
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems... -
19K views
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 96 -
17K views
Nintendo officially confirms Switch successor console, announces Nintendo Direct for next month
While rumors had been floating about rampantly as to the future plans of Nintendo, the President of the company, Shuntaro Furukawa, made a brief statement confirming... -
17K views
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 123 -
14K views
A prototype of the original "The Legend of Zelda" for NES has been found and preserved
Another video game prototype has been found and preserved, and this time, it's none other than the game that spawned an entire franchise beloved by many, the very...by ShadowOne333 31 -
13K views
Anbernic reveals specs details of pocket-sized RG28XX retro handheld
Anbernic is back with yet another retro handheld device. The upcoming RG28XX is another console sporting the quad-core H700 chip of the company's recent RG35XX 2024... -
12K views
New static recompiler tool N64Recomp aims to seamlessly modernize N64 games
As each year passes, retro games become harder and harder to play, as the physical media begins to fall apart and becomes more difficult and expensive to obtain. The... -
12K views
Name the Switch successor: what should Nintendo call its new console?
Nintendo has officially announced that a successor to the beloved Switch console is on the horizon. As we eagerly anticipate what innovations this new device will...
-
-
-
245 replies
Name the Switch successor: what should Nintendo call its new console?
Nintendo has officially announced that a successor to the beloved Switch console is on the horizon. As we eagerly anticipate what innovations this new device will...by Costello -
212 replies
Nintendo officially confirms Switch successor console, announces Nintendo Direct for next month
While rumors had been floating about rampantly as to the future plans of Nintendo, the President of the company, Shuntaro Furukawa, made a brief statement confirming...by Chary -
123 replies
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 -
97 replies
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we...by Scarlet -
96 replies
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 -
84 replies
New static recompiler tool N64Recomp aims to seamlessly modernize N64 games
As each year passes, retro games become harder and harder to play, as the physical media begins to fall apart and becomes more difficult and expensive to obtain. The...by Chary -
82 replies
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other...by Chary -
80 replies
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems...by Chary -
74 replies
"Nintendo World Championships: NES Edition", a new NES Remix-like game, launching July 18th
After rumour got out about an upcoming NES Edition release for the famed Nintendo World Championships, Nintendo has officially unveiled the new game, titled "Nintendo...by ShadowOne333 -
71 replies
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal...by relauby
-
Popular threads in this forum
General chit-chat
- No one is chatting at the moment.
-
 @
K3Nv2:
https://gbatemp.net/threads/ps5-m2sdd-quit-working-in-ps5.622567/page-2 guess I'm not the only one with issues
@
K3Nv2:
https://gbatemp.net/threads/ps5-m2sdd-quit-working-in-ps5.622567/page-2 guess I'm not the only one with issues -
-
-
-
-
-
 @
Psionic Roshambo:
BakerMan I always wanted a Hell Raiser PikeMon spoof with the box instead of poke balls and cenobites instead of pokemon lol
@
Psionic Roshambo:
BakerMan I always wanted a Hell Raiser PikeMon spoof with the box instead of poke balls and cenobites instead of pokemon lol -
-
-
-
-
-
-
-
-
 @
BigOnYa:
Oh, that's why that transformer statue sold at auction for 1.2 million. It would literally shit bricks.+1
@
BigOnYa:
Oh, that's why that transformer statue sold at auction for 1.2 million. It would literally shit bricks.+1 -
 @
Psionic Roshambo:
I always wondered how the autobots could afford to do the stuff they did on the show.... now I know lol+1
@
Psionic Roshambo:
I always wondered how the autobots could afford to do the stuff they did on the show.... now I know lol+1 -
-
 @
Psionic Roshambo:
Megatron "Prime why throw away your life!" Prime "How do I think I got these gold rims!!!"
@
Psionic Roshambo:
Megatron "Prime why throw away your life!" Prime "How do I think I got these gold rims!!!" -
-
 @
Psionic Roshambo:
Channel 69 news "Last night someone stole several cars and a semi truck loaded with drugs from the police impound lot!"
@
Psionic Roshambo:
Channel 69 news "Last night someone stole several cars and a semi truck loaded with drugs from the police impound lot!" -
 @
BakerMan:
i'mma @ juan in the joke thread and say "hey juan i call your mom dwayne the way she rock my johnson"
@
BakerMan:
i'mma @ juan in the joke thread and say "hey juan i call your mom dwayne the way she rock my johnson" -
-
-










