Just to make sure on Any other version than 1.4.0 it will brick, but on 1.4.0 Nintendo forgot to re enable the RSA verification of the whitelist so we can flash a crafted one.Except, in the state that the exploit is in, it's hard to setup for a "consumer." It's also partially dangerous since the user has to modify their nand (manually, as the exploit is contained in the whitelist which is copyrighted, or potentially an xdelta patch could be used for distributing patches early on).
And (I'm 90% sure I'm wrong about this) if the whitelist ends up corrupted then the DSi might brick. The devs wouldn't want to release a buggy product without rigorous testing to make sure it works properly (see: OTPless A9LH).
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
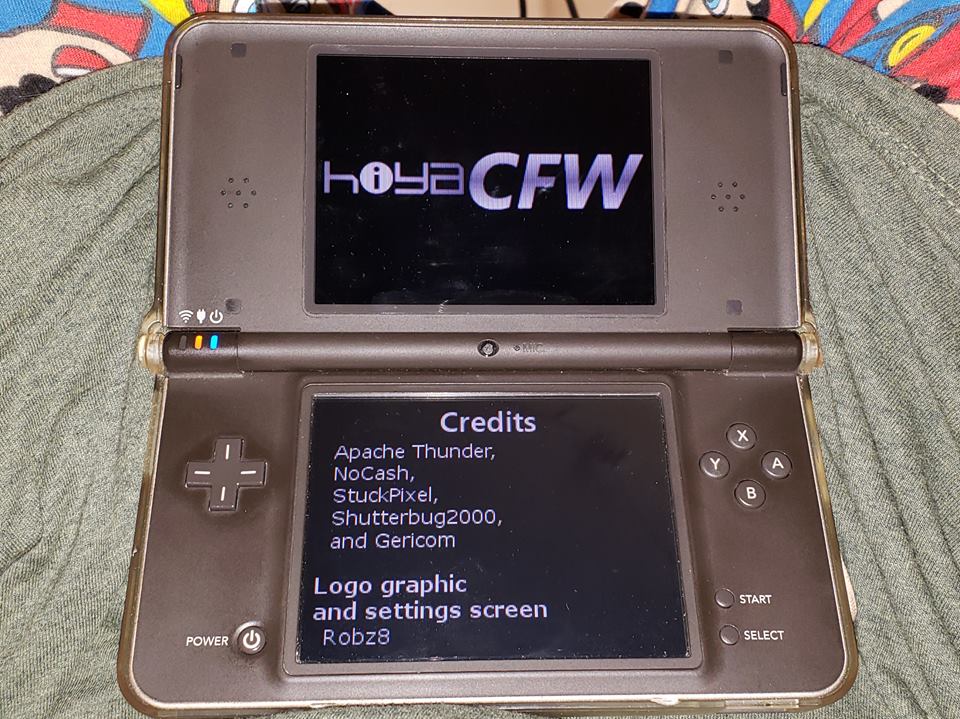
https://github.com/shutterbug2000/hiyaCFW/Where's my HiyaCFW?
It's been here since July. Why don't you go make an exploit so you can play it?
RIP RocketLauncher, you made a nice tease and a nonsence hype train.
Can anyone please lock this until HiyaCFW and/or RocketLauncher eventually come out WHEN they are confirmed to be released?
I've heard you should report the first post and ask for it to be locked.Can anyone please lock this until HiyaCFW and/or RocketLauncher eventually come out WHEN they are confirmed to be released?
Done™.I've heard you should report the first post and ask for it to be locked.
65 pages in already so I would assume close to everything that needs to be said has been said. Until we get more information and/or an actual release, I'll be locking this for the time being.
That was the last thing I was expecting to see from the notification I got!
Wasn't too difficult overall. Having Sudoku already installed with hax made it 10x easier.
- Joined
- Nov 23, 2014
- Messages
- 15,144
- Trophies
- 0
- Location
- Canberra, Australia
- Website
- boot9strap.com
- XP
- 11,119
- Country

You guys can start requesting to be added to the site if you like - I'm trying to rewrite it to have a database and I have to learn a lot of stuff (spring boot, JPA, and mysql). I should get it finished tomorrow. If I didn't have to learn then it probably would have only taken a few hours!
It previously just had an array of everyone's names and was hardcoded to add people to the array when it restarted. So the way I had it before won't work, because it gets restarted like one a day so if I try to add people to the array while the site is running it will just forget them when it restarts itself - and I was hoping to delegate responsibility to someone else to add people so I can't be hard coding it. A database means it won't forget when it is restarted. Hope that made sense.
I installed Hiya before it was officially releasedYou guys can start requesting to be added to the site if you like - I'm trying to rewrite it to have a database and I have to learn a lot of stuff (spring boot, JPA, and mysql). I should get it finished tomorrow. If I didn't have to learn then it probably would have only taken a few hours!
It previously just had an array of everyone's names and was hardcoded to add people to the array when it restarted. So the way I had it before won't work, because it gets restarted like one a day so if I try to add people to the array while the site is running it will just forget them when it restarts itself - and I was hoping to delegate responsibility to someone else to add people so I can't be hard coding it. A database means it won't forget when it is restarted. Hope that made sense.
Similar threads
-
- Article
- Replies
- 3
- Views
- 3K
- Replies
- 29
- Views
- 19K
- Replies
- 3
- Views
- 3K
- Replies
- 112
- Views
- 16K
- Replies
- 92
- Views
- 11K
Site & Scene News
New Hot Discussed
-
-
30K views
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other... -
25K views
New static recompiler tool N64Recomp aims to seamlessly modernize N64 games
As each year passes, retro games become harder and harder to play, as the physical media begins to fall apart and becomes more difficult and expensive to obtain. The... -
24K views
Nintendo officially confirms Switch successor console, announces Nintendo Direct for next month
While rumors had been floating about rampantly as to the future plans of Nintendo, the President of the company, Shuntaro Furukawa, made a brief statement confirming... -
22K views
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems... -
21K views
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 129 -
18K views
Name the Switch successor: what should Nintendo call its new console?
Nintendo has officially announced that a successor to the beloved Switch console is on the horizon. As we eagerly anticipate what innovations this new device will... -
16K views
A prototype of the original "The Legend of Zelda" for NES has been found and preserved
Another video game prototype has been found and preserved, and this time, it's none other than the game that spawned an entire franchise beloved by many, the very...by ShadowOne333 32 -
15K views
Anbernic reveals specs details of pocket-sized RG28XX retro handheld
Anbernic is back with yet another retro handheld device. The upcoming RG28XX is another console sporting the quad-core H700 chip of the company's recent RG35XX 2024... -
13K views
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal... -
12K views
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another...
-
-
-
280 replies
Name the Switch successor: what should Nintendo call its new console?
Nintendo has officially announced that a successor to the beloved Switch console is on the horizon. As we eagerly anticipate what innovations this new device will...by Costello -
232 replies
Nintendo officially confirms Switch successor console, announces Nintendo Direct for next month
While rumors had been floating about rampantly as to the future plans of Nintendo, the President of the company, Shuntaro Furukawa, made a brief statement confirming...by Chary -
129 replies
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 -
127 replies
New static recompiler tool N64Recomp aims to seamlessly modernize N64 games
As each year passes, retro games become harder and harder to play, as the physical media begins to fall apart and becomes more difficult and expensive to obtain. The...by Chary -
88 replies
Ubisoft reveals 'Assassin's Creed Shadows' which is set to launch later this year
Ubisoft has today officially revealed the next installment in the Assassin's Creed franchise: Assassin's Creed Shadows. This entry is set in late Sengoku-era Japan...by Prans -
82 replies
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other...by Chary -
80 replies
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems...by Chary -
78 replies
"Nintendo World Championships: NES Edition", a new NES Remix-like game, launching July 18th
After rumour got out about an upcoming NES Edition release for the famed Nintendo World Championships, Nintendo has officially unveiled the new game, titled "Nintendo...by ShadowOne333 -
71 replies
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal...by relauby -
65 replies
Microsoft is closing down several gaming studios, including Tango Gameworks and Arkane Austin
The number of layoffs and cuts in the videogame industry sadly continue to grow, with the latest huge layoffs coming from Microsoft, due to what MIcrosoft calls a...by ShadowOne333
-
Popular threads in this forum
General chit-chat
-
 AncientBoi
Loading…
AncientBoi
Loading… -
 BigOnYa
Loading…
BigOnYa
Loading…
-
-
-
-
-
-
-
-
 @
Jayro:
Eventhough the New 3DS XL is more powerful, I still feel like the DS Lite was a more polished system. It's a real shame that it never got an XL variant keeping the GBA slot. You'd have to go on AliExpress and buy an ML shell to give a DS phat the unofficial "DS Lite" treatment, and that's the best we'll ever get I'm afraid.+1
@
Jayro:
Eventhough the New 3DS XL is more powerful, I still feel like the DS Lite was a more polished system. It's a real shame that it never got an XL variant keeping the GBA slot. You'd have to go on AliExpress and buy an ML shell to give a DS phat the unofficial "DS Lite" treatment, and that's the best we'll ever get I'm afraid.+1 -
-
 @
SylverReZ:
@Jayro, I don't see whats so special about the DS ML, its just a DS lite in a phat shell. At least the phat model had louder speakers, whereas the lite has a much better screen.+1
@
SylverReZ:
@Jayro, I don't see whats so special about the DS ML, its just a DS lite in a phat shell. At least the phat model had louder speakers, whereas the lite has a much better screen.+1 -
 @
SylverReZ:
They probably said "Hey, why not we combine the two together and make a 'new' DS to sell".
@
SylverReZ:
They probably said "Hey, why not we combine the two together and make a 'new' DS to sell". -
-
-
 @
Veho:
Nothing special about it other than it's more comfortable than the Lite+1
@
Veho:
Nothing special about it other than it's more comfortable than the Lite+1
for people with beefy hands. -
-
-
-
-
-
-
 @
The Real Jdbye:
@SylverReZ if you could find a v5 DS ML you would have the best of both worlds since the v5 units had the same backlight brightness levels as the DS Lite unlockable with flashme
@
The Real Jdbye:
@SylverReZ if you could find a v5 DS ML you would have the best of both worlds since the v5 units had the same backlight brightness levels as the DS Lite unlockable with flashme -
-
-
 @
BigOnYa:
A woman with no arms and no legs was sitting on a beach. A man comes along and the woman says, "I've never been hugged before." So the man feels bad and hugs her. She says "Well i've also never been kissed before." So he gives her a kiss on the cheek. She says "Well I've also never been fucked before." So the man picks her up, and throws her in the ocean and says "Now you're fucked."
@
BigOnYa:
A woman with no arms and no legs was sitting on a beach. A man comes along and the woman says, "I've never been hugged before." So the man feels bad and hugs her. She says "Well i've also never been kissed before." So he gives her a kiss on the cheek. She says "Well I've also never been fucked before." So the man picks her up, and throws her in the ocean and says "Now you're fucked." -






 Or others
Or others