You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Its definitely not an FPGA, it would be a lot more expensive if it had one.
Agreed, also the pin count would be probabily larger.
I've looked up the R4ds company's website,
http://www.gelinelec.com/Product.asp?BigCl...e%20Accessories
they seem to produce a lot of CD/DVD rom replacement parts so maybe its a simple DSP that they use on their CD/DVD peripherals!!!
I spent a humongous 2 day googling session and came up with zilch, trawled thru a lot of chipmakers datasheets
R....
Where didyou get that information?
Mega google session, I think I typed in "R4DS China" and sorta found it.
R..
All I got from searching is that it's: "a controller chip."
Every other website is in Russian.
Yeah, I got that "a controller chip" then followed the links and got nowhere, "no datasheet" sorta responces
I think the ATMEL site might be a good place to scour, their chips begin with AT!!
http://www.atmel.com
look for something with 48pins and runs with maybe a 40mhz or multiples freq
R...
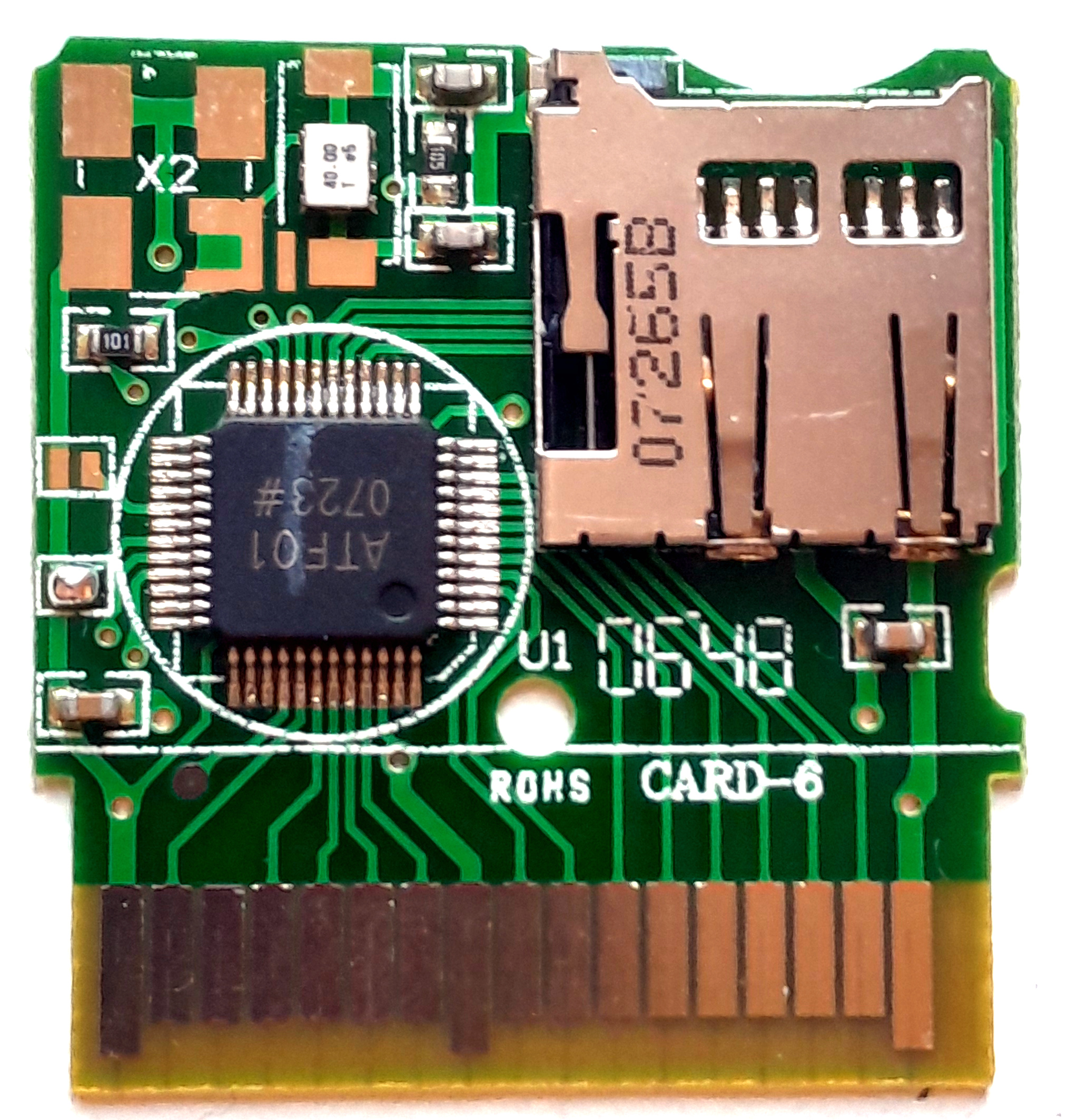
It's a custom asic, meaning they likely made the die themselves or contracted a manufacturer to make it specific for their purpose (hence both epoxied bump and chip packages, and definitely no public datasheets or actel overheads like cost.)
It's a custom asic, meaning they likely made the die themselves or contracted a manufacturer to make it specific for their purpose (hence both epoxied bump and chip packages, and definitely no public datasheets or actel overheads like cost.)
I agree its probibaly a custom chip, but even if it is, Datasheet information can still be attained for the components used within the chip. I.E microcontroller core, memory controller, dsp... as these are usually off the shelf components.
For example:
Atmel customer specific ICs
So a lot of information could be gleemed...
Its not for anything serious I'm just curious about the hardware and its functionality.
R....
If anyone knows what language the R4DS Firmware is in, 8051, Arm, Pics, Zilog ...?
That would tell us what core to look for on the Silicon.
Also could run in thru a disassembler and see if we could figure what other bits might be on the Silicon with the Core.
R....
That would tell us what core to look for on the Silicon.
Also could run in thru a disassembler and see if we could figure what other bits might be on the Silicon with the Core.
R....
You would need to get a dump of the firmware (provided it is not hard wired to work a specific way wrather than being a processor with firmware/data areas) before you could say. It's unlikely that such data is even dumpable without significant work (aka: microprobes, xray, die dissection, timing attacks etc.) It might be interesting to see what the leads that aren't attached to anything are actually doing, you'd never know unless you check (and have the tools available to check with) - could even be some form of jtag/boundary scan or similar interface.
Not going to say it isn't an atmel, but ATF could be anything - even just a acronym for an internal name printed on just to keep their lines sorted and give visual queues for inspectors... for example - "asic trans flash V01 August 12" could easily explain the silkscreen.
http://en.wikipedia.org/wiki/Application-s...egrated_circuit
Do realize that a custom ASIC is not the same thing as a FPGA, mainly for the fact that an FPGA is re-programmable. There is no need to run any specific known core as they are generally set up to "emulate" after a fashion complex circuitry (though they can emulate cores, like ARM implemented on an actel). In the R4's case, they are implementing two serial interfaces to an SD interface and a fairly significant (when talking about asics at any rate) chunk of embedded data memory which apparently is not updateable - and even possibly some form of crypt engine to deal with DS boot up.
Not going to say it isn't an atmel, but ATF could be anything - even just a acronym for an internal name printed on just to keep their lines sorted and give visual queues for inspectors... for example - "asic trans flash V01 August 12" could easily explain the silkscreen.
http://en.wikipedia.org/wiki/Application-s...egrated_circuit
Do realize that a custom ASIC is not the same thing as a FPGA, mainly for the fact that an FPGA is re-programmable. There is no need to run any specific known core as they are generally set up to "emulate" after a fashion complex circuitry (though they can emulate cores, like ARM implemented on an actel). In the R4's case, they are implementing two serial interfaces to an SD interface and a fairly significant (when talking about asics at any rate) chunk of embedded data memory which apparently is not updateable - and even possibly some form of crypt engine to deal with DS boot up.
You would need to get a dump of the firmware (provided it is not hard wired to work a specific way wrather than being a processor with firmware/data areas) before you could say. It's unlikely that such data is even dumpable without significant work (aka: microprobes, xray, die dissection, timing attacks etc.) It might be interesting to see what the leads that aren't attached to anything are actually doing, you'd never know unless you check (and have the tools available to check with) - could even be some form of jtag/boundary scan or similar interface.
Not going to say it isn't an atmel, but ATF could be anything - even just a acronym for an internal name printed on just to keep their lines sorted and give visual queues for inspectors... for example - "asic trans flash V01 August 12" could easily explain the silkscreen.
http://en.wikipedia.org/wiki/Application-s...egrated_circuit
Do realize that a custom ASIC is not the same thing as a FPGA, mainly for the fact that an FPGA is re-programmable. There is no need to run any specific known core as they are generally set up to "emulate" after a fashion complex circuitry (though they can emulate cores, like ARM implemented on an actel). In the R4's case, they are implementing two serial interfaces to an SD interface and a fairly significant (when talking about asics at any rate) chunk of embedded data memory which apparently is not updateable - and even possibly some form of crypt engine to deal with DS boot up.
Hi Cory,
Thanks for the responce, yes I am aware the differences in FPGA's over ASICs, with FPGA more like designing/programming your own silicon over the ASIC's off the shelf solutions (very simplistic analogy).
I only made the slight assertion that the chip could be a ASIC it may be something entirely different. The parts count on the R4 board is so small, it screams of a high level of intergration and of course makes it really diffictult to investigate whats under the hood.
Holes see in all these devices to be investigated are.
1) Firmware or OS updates (although this just seems to be the NDS boot loader)
2) Price (cheap somestime means low off the shelf tech).
3) The signal busses. (device to flash, device to NDS) cant see that giving much away.
4) Find a really early version of the R4 cart in the hope that the circuitry was unrefined.
Unfortunately I havent got the tools to polish away micons to expose the layers, actually or the patience,
Ohhh wouldnt a JTAG interface be nice
I cant see why all the secrecy surrounds what is exactly in these "flash Card" devices. If you look at the last 24c3 conference you will be overwhelmed by the amount of information "Hackers/Homebrewers" put out. I suppose its all about money and competition at the end of the day, which is a shame as knowledge is power... Afterall these devices are based on the ground work of others that freely put the information out there, Dark Fader, Natrium ect....
Innovation comes from experimentation, secrecy stifles innovation.
Early mods like the Xbox/Xodus stuff gave out much more information.
Shame TeamXodus didnt stick to that mindset on the DS Xtreme
Still my lust for wanting to know whats under the hood remains...
R....
P.S the 24c3 hacking the xbox360 is a good youtube watch, a simple 16bit compare instruction flaw, how we laughed.
Yeah, I know Microsoft have patched it, but the reverse engineering journey was a joy to watch. Maybe I'll go to the conference next year, looks more fun the E3, GDC, AGC....
Disclaimer:
I'm not at all interested at all in the "backup" functionality of these cards, just their potential for development and a desire for knowledge...
What does that mean? And speak English please I have no idea what you and cory are talking aboutR....
R....
What does that mean? And speak English please I have no idea what you and cory are talking about
It's obviously him signing his alias on every post:
R = reveng.
And, if you don't understand what they're posting then don't post. Their posts are clearly in legible English.
reveng: I might have a spare R4DS laying around. I'll try to find it, it was my old spring version of the R4DS if that matters to you.
I didn't mean it in a nasty way. It's just that I don't understand what "microprobes, xray, die dissection, timing attacks etc." are. I don't speak geek, so whatever.R....
What does that mean? And speak English please I have no idea what you and cory are talking about
It's obviously him signing his alias on ever post:
R = reveng.
And, if you don't understand what they're posting then don't post. Their posts are clearly in legible English.
reveng: I might have a spare R4DS laying around. I'll try to find it, it was my old spring version of the R4DS if that matters to you.
And what's the point in signing it 'R....' it's not like we can't read his name above his avatar.
I didn't mean it in a nasty way. It's just that I don't understand what "microprobes, xray, die dissection, timing attacks etc." are. I don't speak geek, so whatever.
And what's the point in signing it 'R....' it's not like we can't read his name above his avatar.
Eh, I see... Although, most of this information can be found via google.
Also, I agree. The R... is getting annoying to look at.
What does that mean? And speak English please I have no idea what you and cory are talking about
Sorry you could not understand Ackers, let me try and explain some stuff.
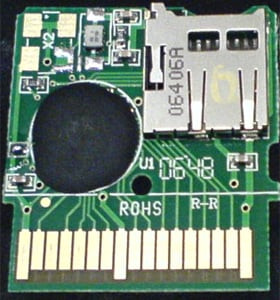
There are two versions of the R4DS circuitboard one with a ceramic chip and the other with the chip just glued on the cicuit board with a blob of Epoxy resin see above.
Myself and Cory where just engaged in a debate over what the ATF01 chip is on the circuit board and the techniques you could employ to find out. "microprobes, xray, die dissection, timing attacks etc." are those techniques...
Unfortunately humans being humans we use a lot of abbreviations, "how many of your friends do you address with their full names?". Software Engineering has so many abbreviations "acronyms" it makes things difficult to follow, even for an engineer
Here's some of the Acronyms, just click on the links.
CPU's
FPGA's
ASIC's
JTAG
DarkFader
Natrium
24C3
E3
GDC
AGC
The rest I will leave up to you and your web browser to seek out all that is unknown
If you find out anything about the ATF01 in your research be sure to post it here.
reveng: I might have a spare R4DS laying around. I'll try to find it, it was my old spring version of the R4DS if that matters to you.
Hi Grimalkin,
If its the circuit board with the chip glued thats the one im interested in.
Hopefully I might be able to dissolve the epoxy with the chip in situ.
That would then give us the info on what connections are going to the Die.
If the springs broken the cart still usually works, mines been broken from almost day one...
thanks again for the offer, much appreciated, but dont send it if its still fuctional keep it as a backup.
reveng: I might have a spare R4DS laying around. I'll try to find it, it was my old spring version of the R4DS if that matters to you.
Hi Grimalkin,
If its the circuit board with the chip glued thats the one im interested in.
Hopefully I might be able to dissolve the epoxy with the chip in situ.
That would then give us the info on what connections are going to the Die.
If the springs broken the cart still usually works, mines been broken from almost day one...
thanks again for the offer, much appreciated, but dont send it if its still fuctional keep it as a backup.
Seeing as I have like.. 5 flash carts. Functional or not, it doesn't matter to me. (And yes, it still works. Including the spring)
I'm still looking for it, but I had to go to work. So I'll reply later on tonight.
EDIT Off-Topic: Woo, 800 posts.
Similar threads
- Replies
- 10
- Views
- 2K
- Replies
- 4
- Views
- 469
- Replies
- 0
- Views
- 428
Site & Scene News
New Hot Discussed
-
-
24K views
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other... -
19K views
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we... -
18K views
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 96 -
18K views
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems... -
16K views
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 120 -
15K views
Nintendo officially confirms Switch successor console, announces Nintendo Direct for next month
While rumors had been floating about rampantly as to the future plans of Nintendo, the President of the company, Shuntaro Furukawa, made a brief statement confirming... -
14K views
A prototype of the original "The Legend of Zelda" for NES has been found and preserved
Another video game prototype has been found and preserved, and this time, it's none other than the game that spawned an entire franchise beloved by many, the very...by ShadowOne333 31 -
12K views
Anbernic reveals specs details of pocket-sized RG28XX retro handheld
Anbernic is back with yet another retro handheld device. The upcoming RG28XX is another console sporting the quad-core H700 chip of the company's recent RG35XX 2024... -
11K views
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another... -
11K views
Name the Switch successor: what should Nintendo call its new console?
Nintendo has officially announced that a successor to the beloved Switch console is on the horizon. As we eagerly anticipate what innovations this new device will...
-
-
-
234 replies
Name the Switch successor: what should Nintendo call its new console?
Nintendo has officially announced that a successor to the beloved Switch console is on the horizon. As we eagerly anticipate what innovations this new device will...by Costello -
205 replies
Nintendo officially confirms Switch successor console, announces Nintendo Direct for next month
While rumors had been floating about rampantly as to the future plans of Nintendo, the President of the company, Shuntaro Furukawa, made a brief statement confirming...by Chary -
120 replies
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 -
97 replies
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we...by Scarlet -
96 replies
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 -
82 replies
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other...by Chary -
80 replies
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems...by Chary -
74 replies
"Nintendo World Championships: NES Edition", a new NES Remix-like game, launching July 18th
After rumour got out about an upcoming NES Edition release for the famed Nintendo World Championships, Nintendo has officially unveiled the new game, titled "Nintendo...by ShadowOne333 -
71 replies
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal...by relauby -
64 replies
Microsoft is closing down several gaming studios, including Tango Gameworks and Arkane Austin
The number of layoffs and cuts in the videogame industry sadly continue to grow, with the latest huge layoffs coming from Microsoft, due to what MIcrosoft calls a...by ShadowOne333
-
Popular threads in this forum
General chit-chat
- No one is chatting at the moment.
-
-
-
 @
BakerMan:
sadly, the clouds are setting in now
@
BakerMan:
sadly, the clouds are setting in now
hey BigOnYa the clouds are coming from the south, maybe check again -
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
 @
K3Nv2:
I really don't want to buy this fap tab https://www.lenovo.com/us/en/p/tabl...enovo-tab-series/tab-p11-pro-gen-2/zab50101us
@
K3Nv2:
I really don't want to buy this fap tab https://www.lenovo.com/us/en/p/tabl...enovo-tab-series/tab-p11-pro-gen-2/zab50101us


