Any software running with the SD+NAND permission enabled can read internal storage (duh) and therefore read your consoleIDReally? How?
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Right. OK. So I'm basically just waiting for ugopwn to be released (like I was anyway). Great!Any software running with the SD+NAND permission enabled can read internal storage (duh) and therefore read your consoleID
The leaked version works just fineRight. OK. So I'm basically just waiting for ugopwn to be released (like I was anyway). Great!
Take a look at my flag, then reread the release post.The leaked version works just fine
Not sure what your flag has to do with anything.Take a look at my flag, then reread the release post.
Urgh. It says in the release post for ugopwn that EUR and JPN aren't supported and will just crash, and the UK was EUR last time I checked.Not sure what your flag has to do with anything.
find, install, and run the operating system dedicated to unlocking Gateway-bricked 3DSes (which is designed to fully load in memory so then you can remove the card it loads from and connect your console instead), it includes a CID viewer
Thank you for clearing that part up, but I'm still at a bit of a loss. I'm entirely new to harmodding and don't even know how to about attaching the NAND pinouts to an insertable SD card. If you could explain that, I'd be all set, really.
Disassemble a microSD adapter in the least destructively possible way, connect 4 wires, preferably doing your best to have them of the same length and reasonably short, to CMD, CLK, DAT0, and GND, connect the other end of the first 3 to your console according to the pictures in the OP, connect GND to any metal shield like slot-1Thank you for clearing that part up, but I'm still at a bit of a loss. I'm entirely new to harmodding and don't even know how to about attaching the NAND pinouts to an insertable SD card. If you could explain that, I'd be all set, really.
Disassemble a microSD adapter in the least destructively possible way, connect 4 wires, preferably doing your best to have them of the same length and reasonably short, to CMD, CLK, DAT0, and GND, connect the other end of the first 3 to your console according to the pictures in the OP, connect GND to any metal shield like slot-1
Ahhhh, Thank you so much. This is gonna be fun~
- Joined
- Jun 27, 2014
- Messages
- 441
- Reaction score
- 192
- Trophies
- 1
- Location
- Santiago, Chile
- XP
- 1,424
- Country

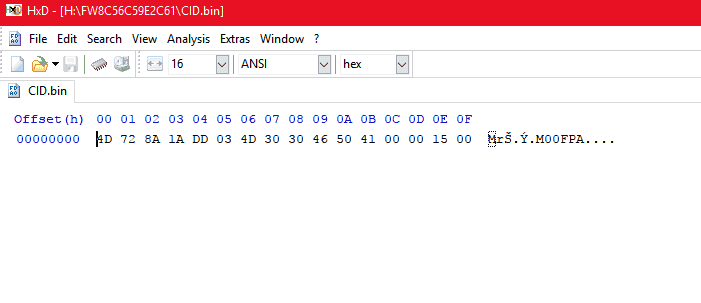
I dumped my CID with FWTOOL and it gave me a CID.bin
but i don't know what i need to put in the command prompt to decrypt the nand... help
but i don't know what i need to put in the command prompt to decrypt the nand... help
Copy the first line to put into command prompt. There's your CID right there.I dumped my CID with FWTOOL and it gave me a CID.bin
but i don't know what i need to put in the command prompt to decrypt the nand... help
View attachment 94916
- Joined
- Jun 27, 2014
- Messages
- 441
- Reaction score
- 192
- Trophies
- 1
- Location
- Santiago, Chile
- XP
- 1,424
- Country

Copy the first line to put into command prompt. There's your CID right there.
what of that is the first line? i'm a bit confused xd
When I decrypted my NAND, I used this command: twltool nandcrypt --cid 7f3c6cc21a3257373136354d00011500 --consoleid 0820537514114111 --in NAND_0.bin --out NAND_DEC.binwhat of that is the first line? i'm a bit confused xd
Last edited by Ghost,
When I decrypted my NAND, I used this command: twltool nandcrypt --cid 7f3c6cc21a3257373136354d00011500 --consoleid 0820537514114111 --in NAND_0.bin --out NAND_DEC.bin
I have your ConsoleID and your CID now I just need your NAND.bin
Good luck using it for a console that I permanently destroyed.I have your ConsoleID and your CID now I just need your NAND.bin
- Joined
- Jun 27, 2014
- Messages
- 441
- Reaction score
- 192
- Trophies
- 1
- Location
- Santiago, Chile
- XP
- 1,424
- Country

When I decrypted my NAND, I used this command: twltool nandcrypt --cid 7f3c6cc21a3257373136354d00011500 --consoleid 0820537514114111 --in NAND_0.bin --out NAND_DEC.bin.
so in that case.. i'll need to use the command (i replaced the consoleid with mine and the cid with what you said, copy the first line)
twltool nandcrypt --cid 4D728A1ADD034D303046504100001500 --consoleid 0820190924109135 --in NAND_0.bin --out NAND_DEC.bin.
Make sure your encrypted NAND file is in the same location with twltool named "NAND_0.bin."so in that case.. i'll need to use the command (i replaced the consoleid with mine and the cid with what you said, copy the first line)
twltool nandcrypt --cid 4D728A1ADD034D303046504100001500 --consoleid 0820190924109135 --in NAND_0.bin --out NAND_DEC.bin.
I have a question. Is there a way to decrypt a NAND using Hardmod without any DSiWare game installed!? Because as I can see to get the ConsoleID we need it...
Similar threads
- Replies
- 3
- Views
- 881
- Replies
- 5
- Views
- 955
-
- Article
- Replies
- 3
- Views
- 1K
-
- Article
- Replies
- 1
- Views
- 1K
Site & Scene News
New Hot Discussed
-
-
25K views
Twilight Princess PC port "Dusk" gets its first release
It wasn't too long ago we saw our first glimpse of Courage Reborn, another Twilight Princess PC port in the works based on last year's decompilation efforts. With... -
14K views
Pokemon Platinum PC port gets a surprise release
Seemingly out of nowhere a PC port for Pokemon Platinum has surfaced online, bundled alongside the source code for those interested in building and developing it for... -
13K views
Nintendo announces price increases across the board, set to come into effect from September in western regions
After much speculation, Nintendo has finally followed their competitors in announcing price increases for their hardware. You can find a breakdown of what's changing... -
11K views
Star Fox 64 remake for the Switch 2 announced in surprise Nintendo Direct
Airing last night with very little in the way of warning, a brand new Nintendo Direct was aired. Running for 15 minutes in total, it took a moment to celebrate the... -
10K views
Steam Deck gets a major price bump, more than 40% increase for US buyers
With very little in the way of announcement, Valve has today increased the price of the Steam Deck but some fairly considerable margins. Both of the available models... -
9K views
Nintendo president Shuntaro Furukawa explains Switch 2 price increases in recent Financial Results Briefing
As a part of their Financial Results Briefing for the previous year, Nintendo president Shuntaro Furukawa took to the floor to answer key questions around the Switch... -
8K views
Sony announces PlayStation Plus price increase for new customers starting May 20
Earlier this year, Sony announced major price increases for the PS5, PS5 Pro, and PlayStation Portal. Now the company is raising prices again, this time for... -
7K views
Forza Horizon 6 leaks online after Steam preload data was uploaded without encryption
We are once again here to tell you about a game leaking before its release, but for once, it's not one published by Nintendo. The game files for Microsoft's upcoming... -
7K views
Pokémon Crystal gets a PC port titled "suiCune" based on C/C++ language
Continuing with the great news of Pokémon Platinum getting a native unofficial PC port just a few days ago, today, yet another classic title from the franchise has... -
6K views
Paper Mario PC recompilation "ReCut" gets its first pre-release build
The latest in a growing number of native PC ports, Paper Mario ReCut got its first pre-release build earlier this week. Based on the N64 recompilation toolchain, the...
-
-
-
166 replies
Steam Deck gets a major price bump, more than 40% increase for US buyers
With very little in the way of announcement, Valve has today increased the price of the Steam Deck but some fairly considerable margins. Both of the available models... -
163 replies
Twilight Princess PC port "Dusk" gets its first release
It wasn't too long ago we saw our first glimpse of Courage Reborn, another Twilight Princess PC port in the works based on last year's decompilation efforts. With... -
144 replies
Nintendo announces price increases across the board, set to come into effect from September in western regions
After much speculation, Nintendo has finally followed their competitors in announcing price increases for their hardware. You can find a breakdown of what's changing... -
134 replies
Star Fox 64 remake for the Switch 2 announced in surprise Nintendo Direct
Airing last night with very little in the way of warning, a brand new Nintendo Direct was aired. Running for 15 minutes in total, it took a moment to celebrate the... -
100 replies
Pokemon Platinum PC port gets a surprise release
Seemingly out of nowhere a PC port for Pokemon Platinum has surfaced online, bundled alongside the source code for those interested in building and developing it for... -
92 replies
Sony announces PlayStation Plus price increase for new customers starting May 20
Earlier this year, Sony announced major price increases for the PS5, PS5 Pro, and PlayStation Portal. Now the company is raising prices again, this time for... -
83 replies
Nintendo president Shuntaro Furukawa explains Switch 2 price increases in recent Financial Results Briefing
As a part of their Financial Results Briefing for the previous year, Nintendo president Shuntaro Furukawa took to the floor to answer key questions around the Switch... -
73 replies
Paper Mario PC recompilation "ReCut" gets its first pre-release build
The latest in a growing number of native PC ports, Paper Mario ReCut got its first pre-release build earlier this week. Based on the N64 recompilation toolchain, the... -
71 replies
PlayStation State of Play June 2, 2026 broadcast - new God of War announced
A whole hour of PlayStation content is on the way, thanks to the latest State of Play showcase. Headlining the stream will be Marvel's Wolverine, alongside a... -
63 replies
Call of Duty: Modern Warfare 4 to launch on Nintendo Switch 2 in October
For the first time in 13 years, the Call of Duty series will again return to Nintendo's consoles. Set to launch on the 23rd of October, the latest release, Modern...
-











