WOW, what a big picture, you could have put that in spoilers like i did above, this is much better for the eyes...and makes reading the thread much better.But my XenoX is little incomplete cuz
I can't download these file and DLC

You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Oh rly sorry i am newbie using forum, sorry :LWOW, what a big picture, you could have put that in spoilers like i did above, this is much better for the eyes...and makes reading the thread much better.
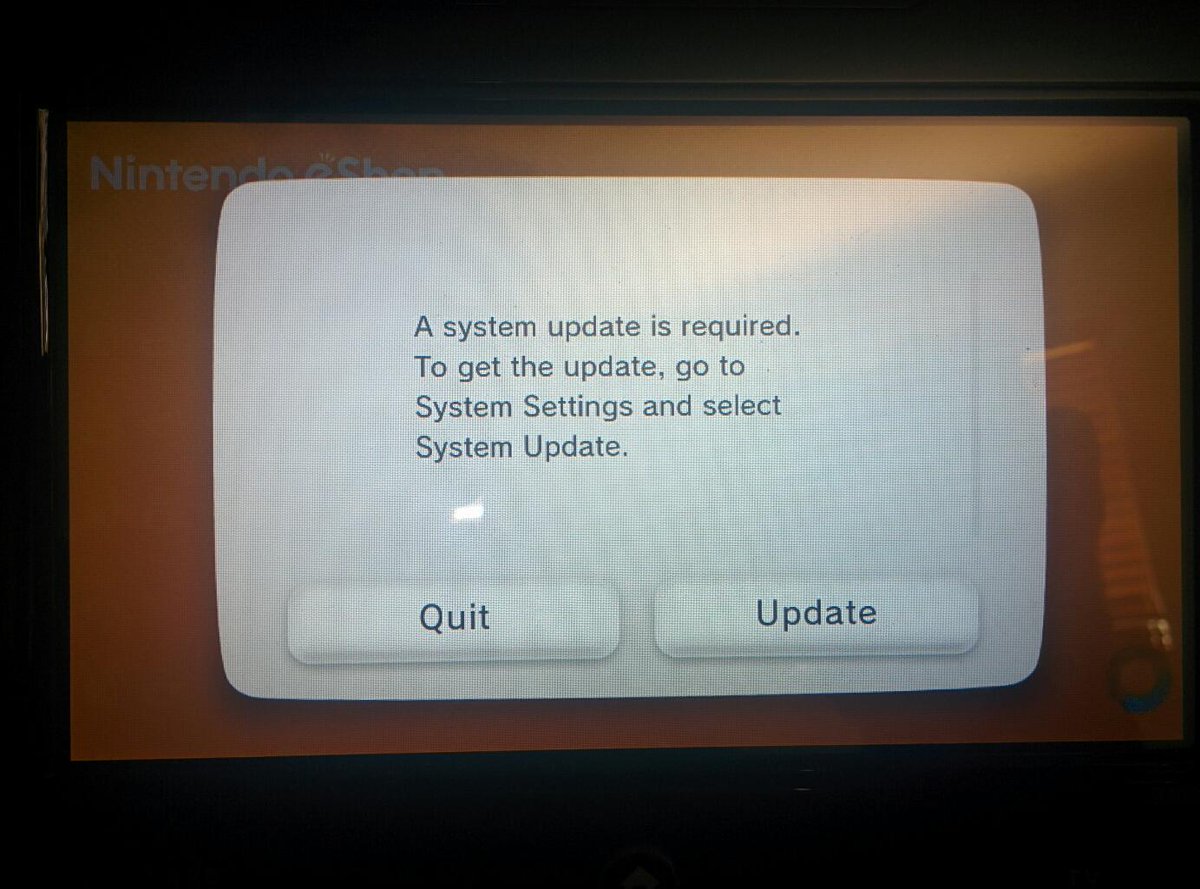
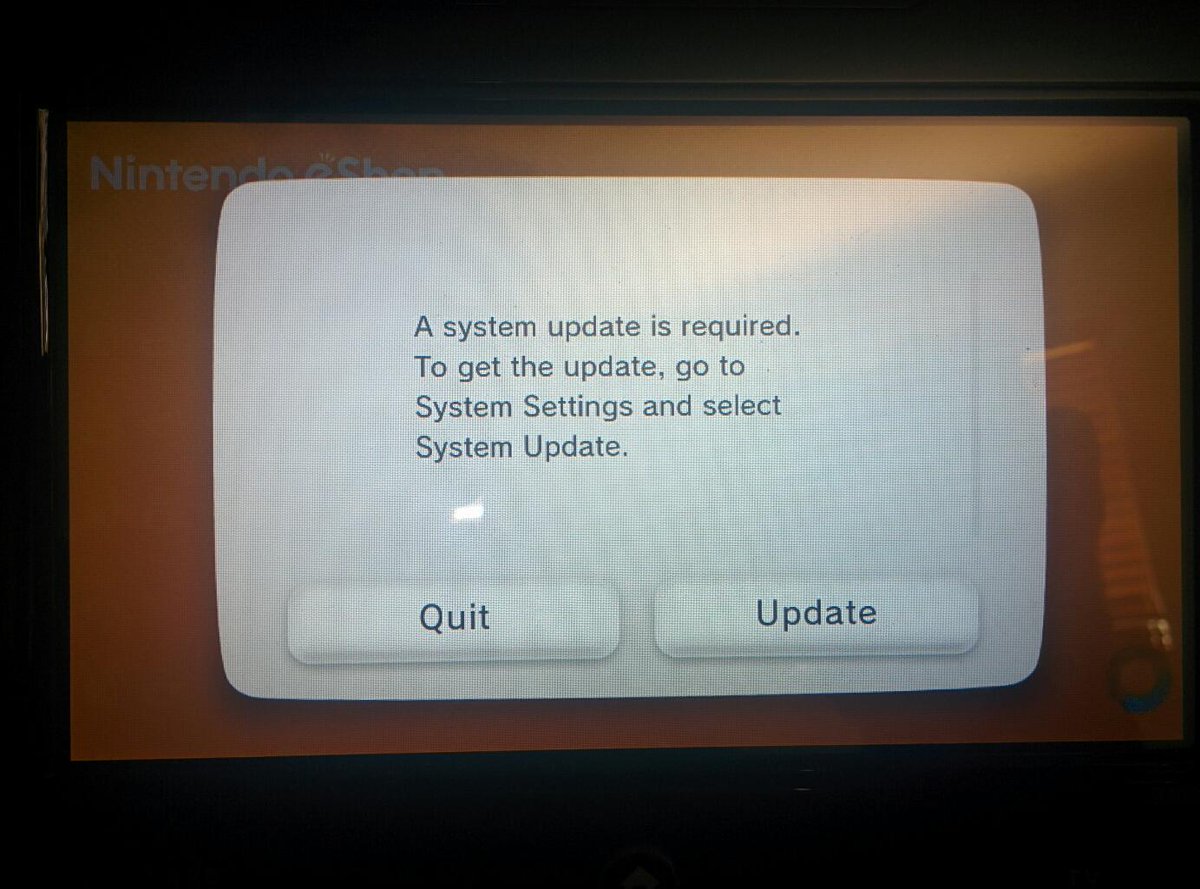
Problem being, I couldn't even setup a Nintendo Network Id yet on my 2nd Wii U since it also requires you to update first
Wow, really? Nintendo is the most anti-consumerist company (besides Apple) that I've seen.
YesWow, really? Nintendo is the most anti-consumerist company (besides Apple) that I've seen.
And in Mario Kart 8 I can't view my character stamps without a Nintendo Network Id but it displays the amount of stamps I have. Just great
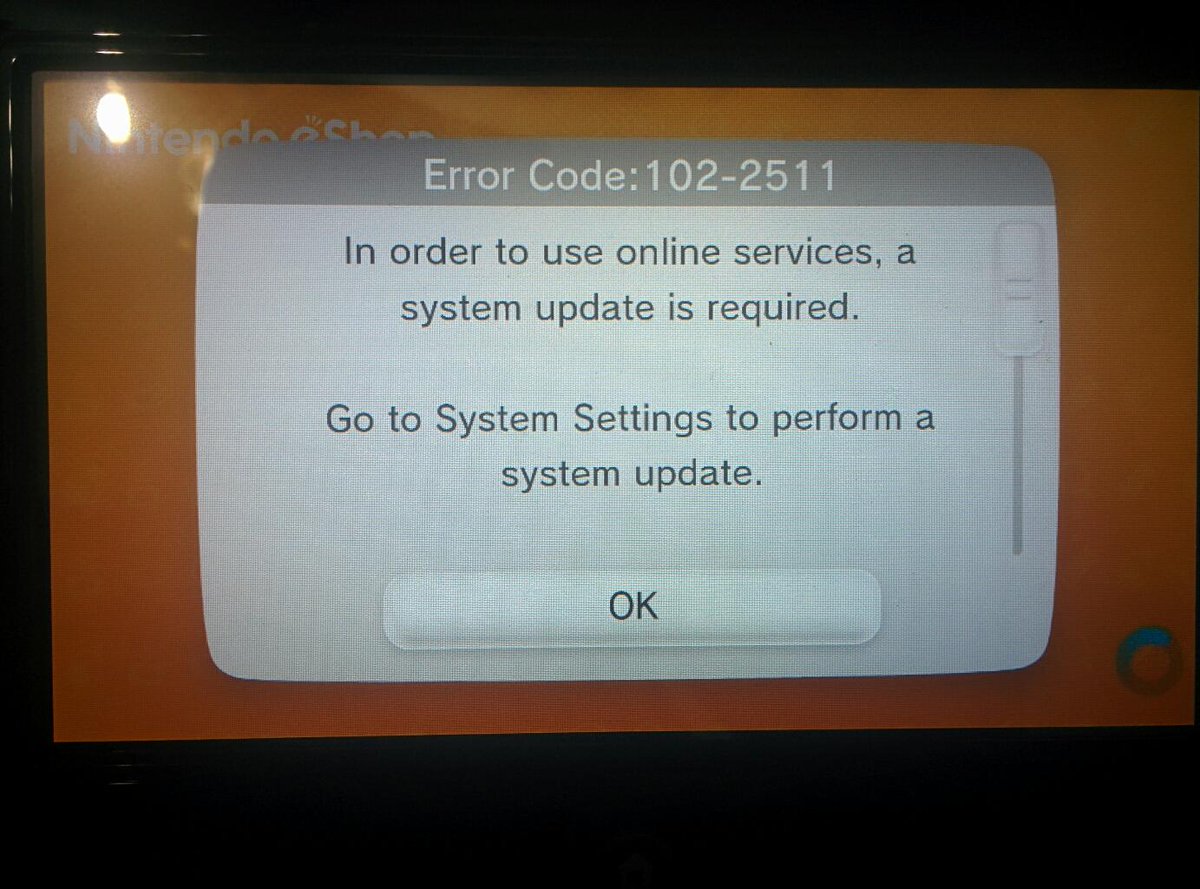
Making more progress on eShop update bypasses. 105-4260 was the old error, which just said the network was "busy" (aka nn::nim::NeedsNetworkUpdate returned 1). This is what happens when you remove the call from the app .text. I'm willing to bet this is a return from NNID sign in, so maybe patching NIM directly will yield results.
I already got to that point few days ago just using tcp gecko, but I could not still get to enter the eshop so I lost interest; my advice is to try messing around with the debug feture of tcp gecko, with which you can pause threads. There are some threads dedicated to update checking and maybe with a good timing you can go inside eshop (and maybe also online games). The only downside is that pausing the wrong thread or at a wrong time it will crash your console, so testing this is really a pain.
True, I paused a random thread for fun and it already crashed so that's pretty retarded.The only downside is that pausing the wrong thread or at a wrong time it will crash your console, so testing this is really a pain.
Still not respondingYou have to use the unmodified codehandler:
Nevermind, it just finished. It just takes a long time
Last edited by BullyWiiPlaza,
cafiine works on 5.5.0, tcp is not so lucky
If I can't do it in code my plan is to take a look at the SSL content by using cafiine or similar (maybe alter the .text to read from SD?) to change the pem to allow me to MITM the SSL on the Wii U while in eShop. I've done it on 3DS so I see no reason for it to fail there, especially with it as modular as it is (3DS needed a reassembled module and modified rodata). It could be a check somewhere which consequently fails it. Or, there's a check somewhere for the error, so even if the actual call returns 0 it'll also check for an existing error. How were you altering the NIM module?I already got to that point few days ago just using tcp gecko, but I could not still get to enter the eshop so I lost interest; my advice is to try messing around with the debug feture of tcp gecko, with which you can pause threads. There are some threads dedicated to update checking and maybe with a good timing you can go inside eshop (and maybe also online games). The only downside is that pausing the wrong thread or at a wrong time it will crash your console, so testing this is really a pain.
the devs said several imes SD acess will be very hard if possible with kernel tough.If I can't do it in code my plan is to take a look at the SSL content by using cafiine or similar (maybe alter the .text to read from SD?) to change the pem to allow me to MITM the SSL on the Wii U while in eShop. I've done it on 3DS so I see no reason for it to fail there, especially with it as modular as it is (3DS needed a reassembled module and modified rodata). It could be a check somewhere which consequently fails it. Or, there's a check somewhere for the error, so even if the actual call returns 0 it'll also check for an existing error. How were you altering the NIM module?
Not quite, Matt and NWPlayer got it workingcafiine works on 5.5.0, tcp is not so lucky
- Joined
- Mar 13, 2015
- Messages
- 1,060
- Trophies
- 0
- Age
- 29
- Location
- Austria
- Website
- epiclper.com
- XP
- 1,151
- Country

Man this thread was active for the past few weeks I was gone 
Uhm... Anyone willing to, in a nutshell, wrap things up here? Did anything "special" or "awesome" happen for 5.3.2 the last... let's say 3 weeks?

Uhm... Anyone willing to, in a nutshell, wrap things up here? Did anything "special" or "awesome" happen for 5.3.2 the last... let's say 3 weeks?
@EpicLPer You also missed a lot of drama 
Man this thread was active for the past few weeks I was gone
Uhm... Anyone willing to, in a nutshell, wrap things up here? Did anything "special" or "awesome" happen for 5.3.2 the last... let's say 3 weeks?
Webkitexploit= userspace access
Pong= first homebrew
Kernel exploit=kernel access
Caffeine = Game files replacement like the old Riivolution
Tcp Gecko = Ram edit and cheats
Ability to dump game files
Online cheating and drama+
People complaining and drama++
Rom injection with Caffeine for VC games
NSMBU level editor
Hardware nand dump and restore
Music replacement for SSB4 and Mario Kart8
People working on IOSU exploit, firmware spoofing, backup loading and more stuff
EDIT: I forgot to mention DRAMA
Once the IOSU exploit is finished, file replacement will be permanent since it will allow for SD/USB file replacements (maybe...)File replacement is permanent using Cafiine?
So I readjusted my patches so that it wouldn't get a chance to throw any errors, now it's not throwing an actual error but the update nags persist.
- Joined
- Jan 7, 2014
- Messages
- 14,600
- Trophies
- 4
- Location
- Another World
- Website
- www.gbatemp.net
- XP
- 25,218
- Country

A step closerSo I readjusted my patches so that it wouldn't get a chance to throw any errors, now it's not throwing an actual error but the update nags persist.
So I readjusted my patches so that it wouldn't get a chance to throw any errors, now it's not throwing an actual error but the update nags persist.
Check which threads are running during the startup of eshop with tcpgecko and see if you find one related to update check
ALRIGHT, got kernel exploit on 3.1.0 working, turns out the memory mapping is quite different, for you guys it physically started at 0x31000000 which maps to 0, for me it starts at 0x30000000 which maps to 0x10000000, my 0 is actually located at 0x4C000000 so where you guys write to 0xA0000000 I need to write to 0xBC000000 now, but hey all that aside its working pretty good, coreinit can be written over quite easly now as I just tried out by patching MCP_GetSystemVersion:


- Joined
- Jan 7, 2014
- Messages
- 14,600
- Trophies
- 4
- Location
- Another World
- Website
- www.gbatemp.net
- XP
- 25,218
- Country

Is it a real firmware spoof, or is it a simple string edit?ALRIGHT, got kernel exploit on 3.1.0 working, turns out the memory mapping is quite different, for you guys it physically started at 0x31000000 which maps to 0, for me it starts at 0x30000000 which maps to 0x10000000, my 0 is actually located at 0x4C000000 so where you guys write to 0xA0000000 I need to write to 0xBC000000 now, but hey all that aside its working pretty good, coreinit can be written over quite easly now as I just tried out by patching MCP_GetSystemVersion:

(please, a real spoof!)
Similar threads
- Replies
- 0
- Views
- 2K
- Replies
- 45
- Views
- 31K
- Replies
- 2
- Views
- 2K
- Replies
- 5
- Views
- 1K
Site & Scene News
New Hot Discussed
-
-
30K views
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other... -
25K views
New static recompiler tool N64Recomp aims to seamlessly modernize N64 games
As each year passes, retro games become harder and harder to play, as the physical media begins to fall apart and becomes more difficult and expensive to obtain. The... -
24K views
Nintendo officially confirms Switch successor console, announces Nintendo Direct for next month
While rumors had been floating about rampantly as to the future plans of Nintendo, the President of the company, Shuntaro Furukawa, made a brief statement confirming... -
22K views
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems... -
21K views
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 129 -
18K views
Name the Switch successor: what should Nintendo call its new console?
Nintendo has officially announced that a successor to the beloved Switch console is on the horizon. As we eagerly anticipate what innovations this new device will... -
16K views
A prototype of the original "The Legend of Zelda" for NES has been found and preserved
Another video game prototype has been found and preserved, and this time, it's none other than the game that spawned an entire franchise beloved by many, the very...by ShadowOne333 32 -
15K views
Anbernic reveals specs details of pocket-sized RG28XX retro handheld
Anbernic is back with yet another retro handheld device. The upcoming RG28XX is another console sporting the quad-core H700 chip of the company's recent RG35XX 2024... -
13K views
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal... -
12K views
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another...
-
-
-
280 replies
Name the Switch successor: what should Nintendo call its new console?
Nintendo has officially announced that a successor to the beloved Switch console is on the horizon. As we eagerly anticipate what innovations this new device will...by Costello -
232 replies
Nintendo officially confirms Switch successor console, announces Nintendo Direct for next month
While rumors had been floating about rampantly as to the future plans of Nintendo, the President of the company, Shuntaro Furukawa, made a brief statement confirming...by Chary -
129 replies
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 -
127 replies
New static recompiler tool N64Recomp aims to seamlessly modernize N64 games
As each year passes, retro games become harder and harder to play, as the physical media begins to fall apart and becomes more difficult and expensive to obtain. The...by Chary -
88 replies
Ubisoft reveals 'Assassin's Creed Shadows' which is set to launch later this year
Ubisoft has today officially revealed the next installment in the Assassin's Creed franchise: Assassin's Creed Shadows. This entry is set in late Sengoku-era Japan...by Prans -
82 replies
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other...by Chary -
80 replies
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems...by Chary -
78 replies
"Nintendo World Championships: NES Edition", a new NES Remix-like game, launching July 18th
After rumour got out about an upcoming NES Edition release for the famed Nintendo World Championships, Nintendo has officially unveiled the new game, titled "Nintendo...by ShadowOne333 -
71 replies
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal...by relauby -
65 replies
Microsoft is closing down several gaming studios, including Tango Gameworks and Arkane Austin
The number of layoffs and cuts in the videogame industry sadly continue to grow, with the latest huge layoffs coming from Microsoft, due to what MIcrosoft calls a...by ShadowOne333
-
Popular threads in this forum
General chit-chat
-
 AncientBoi
Loading…
AncientBoi
Loading… -
 BakerMan
Loading…I rather enjoy a life of taking it easy. I haven't reached that life yet though.
BakerMan
Loading…I rather enjoy a life of taking it easy. I haven't reached that life yet though.
-
-
-
-
-
-
-
-
-
-
-
-
-
 @
Jayro:
Eventhough the New 3DS XL is more powerful, I still feel like the DS Lite was a more polished system. It's a real shame that it never got an XL variant keeping the GBA slot. You'd have to go on AliExpress and buy an ML shell to give a DS phat the unofficial "DS Lite" treatment, and that's the best we'll ever get I'm afraid.+1
@
Jayro:
Eventhough the New 3DS XL is more powerful, I still feel like the DS Lite was a more polished system. It's a real shame that it never got an XL variant keeping the GBA slot. You'd have to go on AliExpress and buy an ML shell to give a DS phat the unofficial "DS Lite" treatment, and that's the best we'll ever get I'm afraid.+1 -
-
 @
SylverReZ:
@Jayro, I don't see whats so special about the DS ML, its just a DS lite in a phat shell. At least the phat model had louder speakers, whereas the lite has a much better screen.+1
@
SylverReZ:
@Jayro, I don't see whats so special about the DS ML, its just a DS lite in a phat shell. At least the phat model had louder speakers, whereas the lite has a much better screen.+1 -
 @
SylverReZ:
They probably said "Hey, why not we combine the two together and make a 'new' DS to sell".
@
SylverReZ:
They probably said "Hey, why not we combine the two together and make a 'new' DS to sell". -
-
-
 @
Veho:
Nothing special about it other than it's more comfortable than the Lite+1
@
Veho:
Nothing special about it other than it's more comfortable than the Lite+1
for people with beefy hands. -
-
-
-
-
-







 Or others
Or others