The trouble with the seeddb updater from the list I posted aboveWhich entry?
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
- Joined
- May 9, 2014
- Messages
- 2,493
- Reaction score
- 1,524
- Trophies
- 0
- Location
- Hervey Bay, Queensland
- XP
- 1,827
- Country

Hmm I'm not following. lol BUT it is 6 am and I'm tired...so yeah. :/The trouble with the seeddb updater from the list I posted above.
9.30pm ( ͡° ͜ʖ ͡°)Hmm I'm not following. lol BUT it is 6 am and I'm tired...so yeah. :/
Good night xD
Alright, I promised a proof-of-concept for my new project, GodMode9, and here it is.
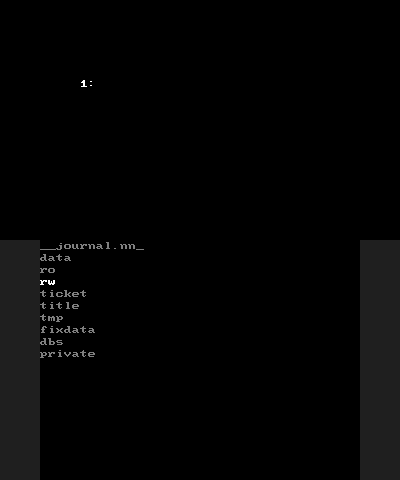
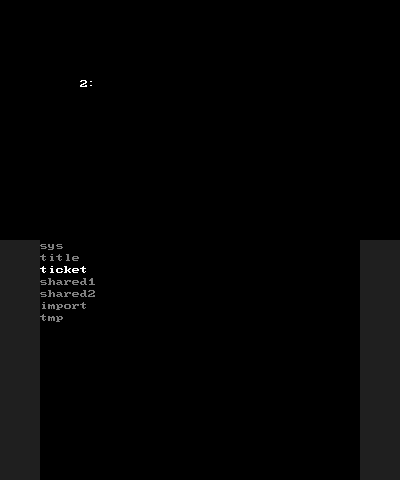
It is still pretty ugly and doesn't do anything useful by itself right now. What it does right now is let you browse (that means only display filenames right now!) the files and folders on your SD card, on your SysNAND CTRNAND/TWLN/TWLP and on your EmuNAND0 CTRNAND/TWLN/TWLP.
When finished this won't be near as refined as CTRXplorer (if you haven't yet, check it out!) is, the two reasons being, that (1) ARM9 doesn't give me the same graphical possibilities and, and (2) a small bug on ARM9 can have dire consequences, especially for those without a NANDmod. So, I will keep it simple.
This is what this will be able to do later:
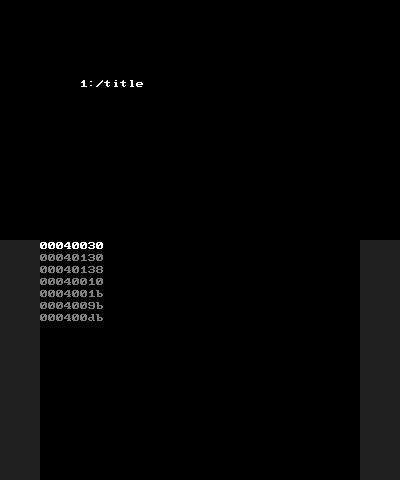
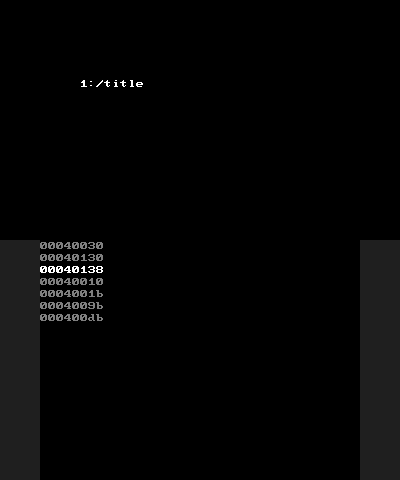
As many of you will be too lazy to try it themselves, here are some screenshots (button is [X], by the way):
Oh, and if you want to try it, no worries. All the NAND writing stuff is stubbed, nothing bad will happen.
It is still pretty ugly and doesn't do anything useful by itself right now. What it does right now is let you browse (that means only display filenames right now!) the files and folders on your SD card, on your SysNAND CTRNAND/TWLN/TWLP and on your EmuNAND0 CTRNAND/TWLN/TWLP.
When finished this won't be near as refined as CTRXplorer (if you haven't yet, check it out!) is, the two reasons being, that (1) ARM9 doesn't give me the same graphical possibilities and, and (2) a small bug on ARM9 can have dire consequences, especially for those without a NANDmod. So, I will keep it simple.
This is what this will be able to do later:
- Copy files between SDcard and all NAND partitions (there will be extra safety for writing to NAND)
- Possibly moving/deleting files, but still up for discussion.
- Creating folders (not looking forward to implementing the name input method :/)
- Possibly supporting multi EmuNAND (not simple to do, FATFS only supports 10 partitions mounted max)
As many of you will be too lazy to try it themselves, here are some screenshots (button is [X], by the way):
Oh, and if you want to try it, no worries. All the NAND writing stuff is stubbed, nothing bad will happen.
Hello, is the emuNAND injection without risk if I want to insert a 2days younger same emuNAND backup to replace the actual one? I received the update nag and browser block yesterday. And what will I lose? todays gamesaves will be replaced with their state two days ago?
Saves are prolly on SD, so I'd say anything installed will be on SD but not considered installed by system and settings changes will be undone.Hello, is the emuNAND injection without risk if I want to insert a 2days younger same emuNAND backup to replace the actual one? I received the update nag and browser block yesterday. And what will I lose? todays gamesaves will be replaced with their state two days ago?
Worst case, make a backup before you restore and observe.
Guys, I hope you can help me with this:
I installed A9LH and now I want to install TWLFirm on both emunand and sysNand. The problem is with sysnand, because when I load decrypt9WIP with A9LH directly, I get an error when I try to extract h&s from sysnand. I also tried to launch AuReinand in sysnand mode by pressing R, it launched fine, launched homebrew menu using ninjhax but when I try to launch decrypt9 or any other app, it just returns me to the homebrew menu again, I don't know why this happens.
I installed A9LH and now I want to install TWLFirm on both emunand and sysNand. The problem is with sysnand, because when I load decrypt9WIP with A9LH directly, I get an error when I try to extract h&s from sysnand. I also tried to launch AuReinand in sysnand mode by pressing R, it launched fine, launched homebrew menu using ninjhax but when I try to launch decrypt9 or any other app, it just returns me to the homebrew menu again, I don't know why this happens.
I installed A9LH so I just make AuReinand boot directly into sysNAND by default and then I hold L to enter my 9.2 emuNAND and use Decrypt9 just fine.Guys, I hope you can help me with this:
I installed A9LH and now I want to install TWLFirm on both emunand and sysNand. The problem is with sysnand, because when I load decrypt9WIP with A9LH directly, I get an error when I try to extract h&s from sysnand. I also tried to launch AuReinand in sysnand mode by pressing R, it launched fine, launched homebrew menu using ninjhax but when I try to launch decrypt9 or any other app, it just returns me to the homebrew menu again, I don't know why this happens.
Guys, I hope you can help me with this:
I installed A9LH and now I want to install TWLFirm on both emunand and sysNand. The problem is with sysnand, because when I load decrypt9WIP with A9LH directly, I get an error when I try to extract h&s from sysnand. I also tried to launch AuReinand in sysnand mode by pressing R, it launched fine, launched homebrew menu using ninjhax but when I try to launch decrypt9 or any other app, it just returns me to the homebrew menu again, I don't know why this happens.
I installed A9LH so I just make AuReinand boot directly into sysNAND by default and then I hold L to enter my 9.2 emuNAND and use Decrypt9 just fine.
This happens because some stuff required for decryption is not (yet?) accessible via A9LH. The solution given by piratesepiroth will work, though.
@d0k3 , can you add a way for us to input data (title id, common key index and encrypted title key) directly into Decrypt9 and have the decrypted titlekey outputted to the screen?
It's kinda annoying always having to make that "enctitlekeys.bin" when we want titlekys for stuff that 's not installed.
It's kinda annoying always having to make that "enctitlekeys.bin" when we want titlekys for stuff that 's not installed.
This happens because some stuff required for decryption is not (yet?)
Just curious, do you know any of the devs working on making this happen? I would like to follow their postings and work, if available.
No one (to my knowledge) is working on that at the moment.Just curious, do you know any of the devs working on making this happen? I would like to follow their postings and work, if available.
Oops forgot to say I also tried launching synand pressing L but didn't launch, but it was because I forgot to put firmware90.bin in rei/ and it launched fine, but this is really weird, I can launch any app except Decrypt9 and Emunand9, because they return me to the homebrew menu. I tried updating the homebrew launcher and it didn't work. Then I renamed Decrypt9.3dsx to boot.3dsx so it launches inmediatly, but it just gets in a loop where the red screen flashes but it doesn't boot.
Edit: Ok, this is evein weirder. Now it worked out of nowhere.
Edit: Ok, this is evein weirder. Now it worked out of nowhere.
Last edited by darklinkpower,
I think it would be better to have a small command line utility to generate the enctitlekeys.bin from human readable data (textfile for example). You won't get a virtual keyboard on ARM9, and implementing a different input method would be a pain in the ass too@d0k3 , can you add a way for us to input data (title id, common key index and encrypted title key) directly into Decrypt9 and have the decrypted titlekey outputted to the screen?
It's kinda annoying always having to make that "enctitlekeys.bin" when we want titlekys for stuff that 's not installed.
Even if it had a simple password screen style, where we select the letters one by one, like in old games, would already be enough.I think it would be better to have a small command line utility to generate the enctitlekeys.bin from human readable data (textfile for example). You won't get a virtual keyboard on ARM9, and implementing a different input method would be a pain in the ass too.
Even if we had to just select the positions with left and right and change the digits with up and down it would already be cool, heheh
Last edited by piratesephiroth,
Asking this... what would be the source of your input data (title id, common key index and encrypted title key)? Any manual input method with these long numbers would be tedious and very error prone, leading to more frustration than good I think.Even if it had a simple password screen style, where we select the letters one by one, like in old games, would already be enough.
Even if we had to just select the positions with left and right and change the digits with up and down it would already be cool, heheh
We can get that info from a legitimate ticket, or even from a CIA made from NUS content with make_cdn_cia (Decrypt9 couldn't handle these last time I tried, by the way).Asking this... what would be the source of your input data (title id, common key index and encrypted title key)? Any manual input method with these long numbers would be tedious and very error prone, leading to more frustration than good I think.
I know the title key is kinda long but as long as you add spaces between its bytes it wouldn't be too much trouble.
Last edited by piratesephiroth,
For legitimate tickets, there is already the print_ticket_keys.py script (included in Decrypt9). For CIAs, I guess make_cdn_cia doesn't lend itself to automation (ie, build a enctitlekeys.bin), but putting something together for the PC commandline is not too difficult. I agree that for single keys, putting it in directly might be a tad faster then moving around files.We can get that info from a legitimate ticket, or even from a CIA made from NUS content with make_cdn_cia (Decrypt9 couldn't handle these last time I tried, by the way).
I know the title key is kinda long but as long as you add spaces between its bytes it wouldn't be too much trouble.
As for CIAs from NUS, made by make_cdn_cia... I'd need an example, and you should better doublecheck it. I recently checked the FW 1.0.0 (US) package (created from a valid NAND backup). Seven files could not be decrypted, but doublechecking these with NUS content it turned out the non-decryptable CIAs had broken contents (100% sure, cause matching hashes and differing files). Maybe @MassExplosion213 knows more?
Knows more about what? I don't pop in too often any more.For legitimate tickets, there is already the print_ticket_keys.py script (included in Decrypt9). For CIAs, I guess make_cdn_cia doesn't lend itself to automation (ie, build a enctitlekeys.bin), but putting something together for the PC commandline is not too difficult. I agree that for single keys, putting it in directly might be a tad faster then moving around files.
As for CIAs from NUS, made by make_cdn_cia... I'd need an example, and you should better doublecheck it. I recently checked the FW 1.0.0 (US) package (created from a valid NAND backup). Seven files could not be decrypted, but doublechecking these with NUS content it turned out the non-decryptable CIAs had broken contents (100% sure, cause matching hashes and differing files). Maybe @MassExplosion213 knows more?
Similar threads
- Replies
- 0
- Views
- 214
- Replies
- 1
- Views
- 2K
- Replies
- 0
- Views
- 345
- Replies
- 4
- Views
- 852
Site & Scene News
New Hot Discussed
-
-
25K views
Twilight Princess PC port "Dusk" gets its first release
It wasn't too long ago we saw our first glimpse of Courage Reborn, another Twilight Princess PC port in the works based on last year's decompilation efforts. With... -
15K views
Pokemon Platinum PC port gets a surprise release
Seemingly out of nowhere a PC port for Pokemon Platinum has surfaced online, bundled alongside the source code for those interested in building and developing it for... -
13K views
Nintendo announces price increases across the board, set to come into effect from September in western regions
After much speculation, Nintendo has finally followed their competitors in announcing price increases for their hardware. You can find a breakdown of what's changing... -
10K views
Steam Deck gets a major price bump, more than 40% increase for US buyers
With very little in the way of announcement, Valve has today increased the price of the Steam Deck but some fairly considerable margins. Both of the available models... -
9K views
Nintendo president Shuntaro Furukawa explains Switch 2 price increases in recent Financial Results Briefing
As a part of their Financial Results Briefing for the previous year, Nintendo president Shuntaro Furukawa took to the floor to answer key questions around the Switch... -
9K views
Sony announces PlayStation Plus price increase for new customers starting May 20
Earlier this year, Sony announced major price increases for the PS5, PS5 Pro, and PlayStation Portal. Now the company is raising prices again, this time for... -
7K views
Forza Horizon 6 leaks online after Steam preload data was uploaded without encryption
We are once again here to tell you about a game leaking before its release, but for once, it's not one published by Nintendo. The game files for Microsoft's upcoming... -
7K views
Pokémon Crystal gets a PC port titled "suiCune" based on C/C++ language
Continuing with the great news of Pokémon Platinum getting a native unofficial PC port just a few days ago, today, yet another classic title from the franchise has... -
6K views
Paper Mario PC recompilation "ReCut" gets its first pre-release build
The latest in a growing number of native PC ports, Paper Mario ReCut got its first pre-release build earlier this week. Based on the N64 recompilation toolchain, the... -
4K views
Low-level 3DS emulator 3Beans released alongside setup tutorial video
When you talk about 3DS emulation, most people would jump to Citra. As the defacto choice since its first release it's seen tremendous success, and even after its...
-
-
-
169 replies
Steam Deck gets a major price bump, more than 40% increase for US buyers
With very little in the way of announcement, Valve has today increased the price of the Steam Deck but some fairly considerable margins. Both of the available models... -
163 replies
Twilight Princess PC port "Dusk" gets its first release
It wasn't too long ago we saw our first glimpse of Courage Reborn, another Twilight Princess PC port in the works based on last year's decompilation efforts. With... -
144 replies
Nintendo announces price increases across the board, set to come into effect from September in western regions
After much speculation, Nintendo has finally followed their competitors in announcing price increases for their hardware. You can find a breakdown of what's changing... -
102 replies
Pokemon Platinum PC port gets a surprise release
Seemingly out of nowhere a PC port for Pokemon Platinum has surfaced online, bundled alongside the source code for those interested in building and developing it for... -
92 replies
Sony announces PlayStation Plus price increase for new customers starting May 20
Earlier this year, Sony announced major price increases for the PS5, PS5 Pro, and PlayStation Portal. Now the company is raising prices again, this time for... -
83 replies
Nintendo president Shuntaro Furukawa explains Switch 2 price increases in recent Financial Results Briefing
As a part of their Financial Results Briefing for the previous year, Nintendo president Shuntaro Furukawa took to the floor to answer key questions around the Switch... -
73 replies
Paper Mario PC recompilation "ReCut" gets its first pre-release build
The latest in a growing number of native PC ports, Paper Mario ReCut got its first pre-release build earlier this week. Based on the N64 recompilation toolchain, the... -
71 replies
PlayStation State of Play June 2, 2026 broadcast - new God of War announced
A whole hour of PlayStation content is on the way, thanks to the latest State of Play showcase. Headlining the stream will be Marvel's Wolverine, alongside a... -
63 replies
Call of Duty: Modern Warfare 4 to launch on Nintendo Switch 2 in October
For the first time in 13 years, the Call of Duty series will again return to Nintendo's consoles. Set to launch on the 23rd of October, the latest release, Modern... -
54 replies
Nintendo shows off mouse controls for the upcoming Star Fox remake
With the latest entry to the Star Fox series being announced earlier this month, Nintendo have today shown off one of the features new to the game in the mouse...
-











