So from my gathering of information it is possible but very unlikely to bruteforce the encryption of the 3ds? So my question is would you just bruteforce a 3ds rom? or am i mistaken and its impossible?
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Bruteforcing would take a VERY long time.
It might comes out with even more security and then it would still be bogus.
It might comes out with even more security and then it would still be bogus.
Your best bet is to use a supercomputer for bruteforcing it.
A normal beast PC couldn't bruteforce the 3DS security in 24 hours.
Otherwise people would've already done that back in Feb. when the 3DS came out.
A normal beast PC couldn't bruteforce the 3DS security in 24 hours.
Otherwise people would've already done that back in Feb. when the 3DS came out.
Theoretically, it's possible. Practically, it's not. This is because, IIRC, the 3DS uses secure RSA for encrypting (4096-bit IIRC). The number of possible keys is astronomical and will take "far longer than the age of the universe to complete". That's what I've heard, at least...
EDIT: Someone had made a good post about why it isn't possible to brute force 3DS keys... if I only can find it...
EDIT: Someone had made a good post about why it isn't possible to brute force 3DS keys... if I only can find it...
Impractical to do, unless you have access to CERN's supercomputer array.
Otherwise, it may take longer than the age of the universe to do on conventional computers.
There is another way to obtain the keys, and it's with Ramhax of some kind, and a lot of luck.
Otherwise, it may take longer than the age of the universe to do on conventional computers.
There is another way to obtain the keys, and it's with Ramhax of some kind, and a lot of luck.
Our best bet is a hardware hack.
Just look at the 360.
First the DVD drive got hacked which lead to a Hypervisor escalation resulting in the King Kong exploit.
Then came the Timing Attack wich relied upon booting the base kernel via some glitching and patching it to Dash 4548.
Then came the jTAG hack wich relied upon a old CB and was usable up to dash 7371.
Then came the RGH wich also relies upon a certain CB to glitch the hashing and load a hacked 4548 kernel.
As for softmods on the 360?
There is NONE
And there won't be one very likely.
Just look at the 360.
First the DVD drive got hacked which lead to a Hypervisor escalation resulting in the King Kong exploit.
Then came the Timing Attack wich relied upon booting the base kernel via some glitching and patching it to Dash 4548.
Then came the jTAG hack wich relied upon a old CB and was usable up to dash 7371.
Then came the RGH wich also relies upon a certain CB to glitch the hashing and load a hacked 4548 kernel.
As for softmods on the 360?
There is NONE
And there won't be one very likely.
I asked a question like this once and I was told it would take up to 50 years even with alot of people or somthing crazy like that....
I asked a question like this once and I was told it would take up to 50 years even with alot of people or somthing crazy like that....
It would take 50 years if all the computers in the world, and all that are to be, focused it's tasks on bruteforcing this key. Every last one.
Otherwise, it would take longer than the age of the Universe.
I asked a question like this once and I was told it would take up to 50 years even with alot of people or somthing crazy like that....
It would take 50 years if all the computers in the world, and all that are to be, focused it's tasks on bruteforcing this key. Every last one.
Otherwise, it would take longer than the age of the Universe.
if theres only one encryption level.....
just to put this into perspective, people proposed doing this on the xbox1 to get the private signing key, and it still hasn't yielded a key almost a decade later. (and that was a less complicated key).
in short, have fun!
in short, have fun!
Bruteforcing would take a VERY long time.
It might comes out with even more security and then it would still be bogus.
*could take a VERY long time.
There is also a possibility it would be the first key generated. Such is the nature of a randomly generated number. It could be randomly generated again instantly or it could take hundreds of years.
- Joined
- Apr 29, 2009
- Messages
- 511
- Trophies
- 1
- Age
- 31
- Website
- ridersrealm.b1.jcink.com
- XP
- 1,835
- Country

Great! Let's call Daru to hack into that stuff.Impractical to do, unless you have access to CERN's supercomputer array.
Although we might also need to use the Time Machine too...
If we have a time machine, why not just go forward a few years to when hacks exist?Great! Let's call Daru to hack into that stuff.Impractical to do, unless you have access to CERN's supercomputer array.
Although we might also need to use the Time Machine too...
Here's my copy-paste about the DSi, when people were asking about it.
For the 3DS, just assume it's even harder.
I present to you: "DSi Encryption Put In Perspective", also known as "I Love Crushing People's Dreams".
The DSi uses 128-bit encryption (IIRC).
How do you break it? You find the correct encryption key.
How many encryption keys are there? 2 (binary, a bit) to the 128th power (number of bits), divided by 8 (8 bits in a byte).
That's so many that the calculator that comes with windows (at least XP) can't even display the number without reverting to scientific notation.
128-bits is...
340,282,366,920,938,463,463,374,607,431,768,211,456 possible values in binary.
However, Since there's 8 bits in a byte, you divide 128 by 8 and get 16. That's 16 bytes, 16 characters.
That's 18,446,744,073,709,552,000 possible values, ranging from 0x0000000000000000 to 0xFFFFFFFFFFFFFFFF. Eighteen quintillion possible keys.
The actual number is a bit less less since a key will be a certain number of digits and be designed to not have repeating segments, but this puts it in perspective.
Let's say that you have a computer program which can try 50,000 unique keys a second.
That's 3,000,000 keys a minute.
180,000,000 keys in an hour.
4,320,000,000 keys a day.
1,576,800,000,000 keys in one year.
It would take 11,698,848 years to try all the keys at that speed.
So wait, how do they break other systems? If you can get a direct copy of the encrypted data and compare it to a copy of the unencrypted data (as well as view the data as it's transmitted around the DSi's internals), that goes a long way towards figuring out the key without having to try all possible combinations. You'll be able to find the key without all the guessing! The problem is you'd need to take a DSi apart and fuck with it's insides while it's on to try to get a copy of the data while it's unencrypted (since the DSi will unencrypt what it needs on the fly in order to use it), and usually when you're done with that the DSi's pretty broken and in no shape to game, or even to be experimented on a second time...
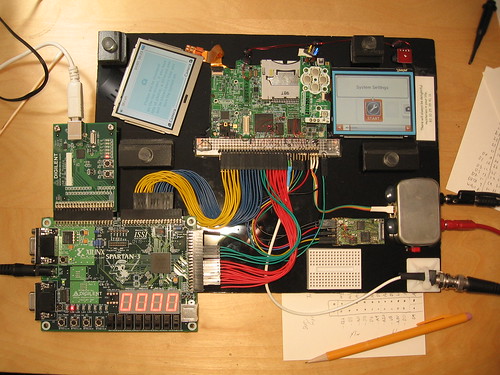
http://www.flickr.com/photos/micahdowty/sets/72157621023570420/
This process can be hampered by the internal design of the system, so you may need to take apart many systems before you even figure out how to read some of the data, let alone get a full copy of it, and last I checked DSi's don't cost $5...
For the 3DS, just assume it's even harder.
Well,
You're assuming that the very last key tried is the proper one. If you're going in a random order (you know, instead of starting at like 00000000000001, with more zeroes before it), I'm sure somebody would find it before then.
The problem is co-ordinating it. I remember there used to be a program that was trying to decrypt the DSi common key, and it would check into a central server that had a list of what's been tried already... I used to run that thing, too, but it sort-of vanished... I had actually heard that some elitist hackers DID find the key already and just didn't tell anybody, so the rest of the world was just wasting CPU power on nothing. I'm sure somebody, somewhere, has figured it out - that's the problem with hackers, they don't want to come forward for fear of being sued, so they just do it for fun and never tell anybody.
Which is why we need this to be a group effort
But yeah. Brute-forcing should totally be possible, it was being done for the DSi too... we just need to make sure this time everybody can view the results, etc. I'm not saying it's very practical, and I'm sure a different exploit will be found before anybody finds it via brute-force, but it would certainly be better than sitting around doing nothing while waiting for some elitist hackers to be nice enough to share their findings with us. No, I'm not going to coordinate this, do not ask me.
You're assuming that the very last key tried is the proper one. If you're going in a random order (you know, instead of starting at like 00000000000001, with more zeroes before it), I'm sure somebody would find it before then.
The problem is co-ordinating it. I remember there used to be a program that was trying to decrypt the DSi common key, and it would check into a central server that had a list of what's been tried already... I used to run that thing, too, but it sort-of vanished... I had actually heard that some elitist hackers DID find the key already and just didn't tell anybody, so the rest of the world was just wasting CPU power on nothing. I'm sure somebody, somewhere, has figured it out - that's the problem with hackers, they don't want to come forward for fear of being sued, so they just do it for fun and never tell anybody.
Which is why we need this to be a group effort
But yeah. Brute-forcing should totally be possible, it was being done for the DSi too... we just need to make sure this time everybody can view the results, etc. I'm not saying it's very practical, and I'm sure a different exploit will be found before anybody finds it via brute-force, but it would certainly be better than sitting around doing nothing while waiting for some elitist hackers to be nice enough to share their findings with us. No, I'm not going to coordinate this, do not ask me.
>Assuming there will be hacks in a few yearsIf we have a time machine, why not just go forward a few years to when hacks exist?Great! Let's call Daru to hack into that stuff.Impractical to do, unless you have access to CERN's supercomputer array.
Although we might also need to use the Time Machine too...
>Assuming there will be hacks in a few yearsIf we have a time machine, why not just go forward a few years to when hacks exist?Great! Let's call Daru to hack into that stuff.Impractical to do, unless you have access to CERN's supercomputer array.
Although we might also need to use the Time Machine too...
Similar threads
- Replies
- 0
- Views
- 235
- Replies
- 2
- Views
- 2K
- Replies
- 2
- Views
- 1K
- Replies
- 0
- Views
- 576
Site & Scene News
New Hot Discussed
-
-
25K views
Wii U and 3DS online services shutting down today, but Pretendo is here to save the day
Today, April 8th, 2024, at 4PM PT, marks the day in which Nintendo permanently ends support for both the 3DS and the Wii U online services, which include co-op play...by ShadowOne333 179 -
21K views
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other... -
18K views
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we... -
17K views
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 96 -
15K views
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems... -
13K views
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 113 -
12K views
A prototype of the original "The Legend of Zelda" for NES has been found and preserved
Another video game prototype has been found and preserved, and this time, it's none other than the game that spawned an entire franchise beloved by many, the very...by ShadowOne333 31 -
10K views
Anbernic reveals specs details of pocket-sized RG28XX retro handheld
Anbernic is back with yet another retro handheld device. The upcoming RG28XX is another console sporting the quad-core H700 chip of the company's recent RG35XX 2024... -
10K views
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another... -
10K views
Nintendo "Indie World" stream announced for April 17th, 2024
Nintendo has recently announced through their social media accounts that a new Indie World stream will be airing tomorrow, scheduled for April 17th, 2024 at 7 a.m. PT...by ShadowOne333 53
-
-
-
179 replies
Wii U and 3DS online services shutting down today, but Pretendo is here to save the day
Today, April 8th, 2024, at 4PM PT, marks the day in which Nintendo permanently ends support for both the 3DS and the Wii U online services, which include co-op play...by ShadowOne333 -
113 replies
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 -
97 replies
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we...by Scarlet -
96 replies
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 -
80 replies
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other...by Chary -
78 replies
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems...by Chary -
67 replies
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal...by relauby -
55 replies
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another...by Chary -
53 replies
Nintendo "Indie World" stream announced for April 17th, 2024
Nintendo has recently announced through their social media accounts that a new Indie World stream will be airing tomorrow, scheduled for April 17th, 2024 at 7 a.m. PT...by ShadowOne333 -
52 replies
The FCC has voted to restore net neutrality, reversing ruling from 2017
In 2017, the United States Federal Communications Commission (FCC) repealed net neutrality. At the time, it was a major controversy between internet service providers...by Chary
-
Popular threads in this forum
General chit-chat
-
-
 @
Psionic Roshambo:
I like that games can be fixed after the fact, hate that it's being abused via beta tests... And DLC... I was a 7800 owner back in the day and loved Impossible Mission, turns out I couldn't beat it because it was actually impossible lol
@
Psionic Roshambo:
I like that games can be fixed after the fact, hate that it's being abused via beta tests... And DLC... I was a 7800 owner back in the day and loved Impossible Mission, turns out I couldn't beat it because it was actually impossible lol -
 @
Psionic Roshambo:
I never knew about it at the time but a fixed version was available but you had to mail in your broken copy lol
@
Psionic Roshambo:
I never knew about it at the time but a fixed version was available but you had to mail in your broken copy lol -
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
 @
Psionic Roshambo:
https://youtu.be/Gy3BOmvLf2w?list=OLAK5uy_k27izUIERfT-RIE1qN1CHIOIkW4h5A9BY Play this song if Hippies are bothering you! lol
@
Psionic Roshambo:
https://youtu.be/Gy3BOmvLf2w?list=OLAK5uy_k27izUIERfT-RIE1qN1CHIOIkW4h5A9BY Play this song if Hippies are bothering you! lol -
-
-
-
-




