I did NOT create the exploits/homebrew described in this post; please thank MarioNumber1, Hykem, and the other contributors. If you find any mistakes, please let me know.
This post contains info about the wii u webkit/kernel exploits and how to run/compile them. For more practical guides, check out Summersett's guides.
WiiU homebrew situation
Updated on June 19th 2016
Wii U security has been compromised and homebrew exists. Homebrew development is still in earlier stage, so there aren't a lot of apps yet.
A homebrew launcher has been released by Dimok.
The homebrew launcher is not permanently installed to your system, you need to run it again every time you shutdown your console. Once launched, you can always return to the homebrew launcher by launching the MiiMaker application.
WiiU exploits
Before the homebrew launcher release, the developers had to merge and encapsulate their homebrew binary inside different exploitable binaries.
This is not needed anymore as the homebrew launcher is granting access to user and kernel space to most commonly used WiiU version.
For historical reasons, and to be able to compile old homebrew, this section is kept on this guide:
Preliminary steps
Before launching homebrew, be sure to prevent the console from updating to newer firmware version.
1) Block the Nintendo Update Server (NUS). There are different methods you can use:
Compiling homebrew
Windows/Linux/MacOS
1: install prerequisites
2: Create or clone a project
Note: Old homebrew required that the project was created as a sub-folder of your libwiiu path. If you are creating a new project or cloning a recent homebrew, you can place its folder anywhere on your computer.
3: Build your homebrew.
Old homebrew might require you to merge the compiled homebrew binary inside an exploit binary. To do this, you need to use Libwiiu package and the provided Python script.
Since the release of the Homebrew Launcher, you don't need to merge your homebrew inside one of the existing exploit's binary anymore!
The homebrew launcher is already patching both the user and kernel space and grant these access to all launched homebrew.
If you develop a homebrew, you only need to compile it to an executable format (.elf) and launch if from the homebrew launcher, like you used to do on the Wii.
If you really need to inject your homebrew into an exploitable binary (for example to bypass the homebrew launcher completely, or if you are compiling the homebrew launcher itself), look into this spoiler:
Launching homebrew
there are two different methods to launch homebrew : homebrew launcher, or the old "individual homebrew injected into an exploit".
Most homebrew has been updated to use the homebrew launcher method, but this section will detail both method for historical reason.
1) The homebrew launcher method :
If your homebrew is an executable (.elf) then you only need to copy the homebrew to your SD card and launch it with the homebrew launcher.
- copy the homebrew in sd:/wiiu/apps/<name of your homebrew>/<filename>.elf
- optionally, copy the homebrew's meta.xml and icon.png in the same folder.
- install the homebrew launcher from the web browser, and select your homebrew to launch.
2) the old method, individual homebrew merged with an exploit.
Existing homebrew
You can find a list of released homebrew on our wiki.
http://wiki.gbatemp.net/wiki/List_of_WiiU_homebrew
F.A.Q.
This post contains info about the wii u webkit/kernel exploits and how to run/compile them. For more practical guides, check out Summersett's guides.
WiiU homebrew situation
Updated on June 19th 2016
Wii U security has been compromised and homebrew exists. Homebrew development is still in earlier stage, so there aren't a lot of apps yet.
A homebrew launcher has been released by Dimok.
The homebrew launcher is not permanently installed to your system, you need to run it again every time you shutdown your console. Once launched, you can always return to the homebrew launcher by launching the MiiMaker application.
WiiU exploits
Before the homebrew launcher release, the developers had to merge and encapsulate their homebrew binary inside different exploitable binaries.
This is not needed anymore as the homebrew launcher is granting access to user and kernel space to most commonly used WiiU version.
For historical reasons, and to be able to compile old homebrew, this section is kept on this guide:
Types of exploits (sorted by amount of access granted)
Exploit status on firmware versions
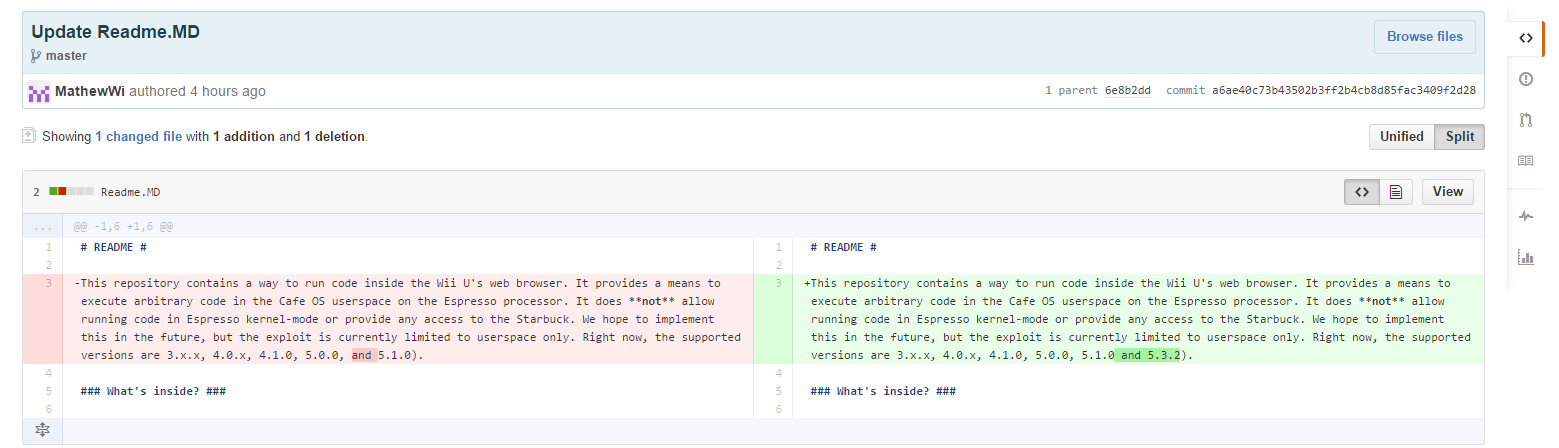
2.0.0 - 5.1.0: Userspace exploit (Webkit), kernel exploit (OSDriver, somewhat unreliable), ioctlvhax
5.2.0-5.3.1: Same exploits possible but still undevelopped
5.3.2-5.4.0: Userspace exploit (MP4), kernel exploit (OSDriver, somewhat unreliable), private IOSU exploits
5.5.x: Userspace exploit (MP4), kernel exploit (reliable), private IOSU exploits (Might be broken)
TL;DR
Versions that can be used for fun hacks right now: 5.3.2, 5.4.0, 5.5.0, 5.5.1
Versions that are still secure: /
("Fun hacks" are TCPGecko, Cafiine, Dumpiine, ___iine, etc. Things that require both a userspace and a kernel exploit.)
Hopefully that helps some of you understand where we're at right now. I'll be around here to answer questions now and then.
Here is a maintained list of possible exploits based on WiiU version: http://rhcafe.us.to/
- A Userspace exploit breaks the security of the specific app it's running in. This exploit has to respect the permissions of app its running in, so it's limited (e.g. the internet browser can't access SD-cards or random RAM-memory, so neither can the exploit). It allows for basic homebrew games, but is mainly import for further exploitation. The userspace exploits are referred to interchangeably as "userspace," "userland" and "WebKit/MP4" exploits.
- The Kernel exploit or Cafe OS exploit, is a exploit that breaks out of the userland. This allows for bigger/advanced programs.
- The IOSU exploit breaks the final barrier (a special security chip, the IOSU). The Wii U is entirely in your hands now. A IOSU exploit typically needs the first two to build further upon, Hykem's is an exception to this as it only needs the former.
Exploit status on firmware versions
2.0.0 - 5.1.0: Userspace exploit (Webkit), kernel exploit (OSDriver, somewhat unreliable), ioctlvhax
5.2.0-5.3.1: Same exploits possible but still undevelopped
5.3.2-5.4.0: Userspace exploit (MP4), kernel exploit (OSDriver, somewhat unreliable), private IOSU exploits
5.5.x: Userspace exploit (MP4), kernel exploit (reliable), private IOSU exploits (Might be broken)
TL;DR
Versions that can be used for fun hacks right now: 5.3.2, 5.4.0, 5.5.0, 5.5.1
Versions that are still secure: /
("Fun hacks" are TCPGecko, Cafiine, Dumpiine, ___iine, etc. Things that require both a userspace and a kernel exploit.)
Hopefully that helps some of you understand where we're at right now. I'll be around here to answer questions now and then.
Here is a maintained list of possible exploits based on WiiU version: http://rhcafe.us.to/
Preliminary steps
Before launching homebrew, be sure to prevent the console from updating to newer firmware version.
1) Block the Nintendo Update Server (NUS). There are different methods you can use:
- Block URL manually from your router
nus.c.shop.nintendowifi.net
nus.cdn.c.shop.nintendowifi.net
nus.cdn.shop.wii.com
nus.cdn.wup.shop.nintendo.net
nus.wup.shop.nintendo.net
c.shop.nintendowifi.net
cbvc.cdn.nintendo.net
cbvc.nintendo.net - Block URLs using OpenDNS (NOT RECOMMENDED - UNEFFECTIVE)
- Block URLs using a proxy (You need your computer powered)
- Block URLs using TubeHax DNS (Recommended). Set DNS manually to 107.211.140.065
Compiling homebrew
Windows/Linux/MacOS
1: install prerequisites
- Install Devkitpro with libogc, devkitPPC and devkitARM.
You will have to get additional libraries used by a lot of homebrew (the portlibs) from here : https://github.com/dimok789/homebrew_launcher/releases/tag/v1.0
Download both the "libogc" and "portlibs" packages and extract them to your devkitpro folder, replacing any existing files.
Optional, some homebrew (mainly old ones) might need this : - Python 2.x
- libwiiu sources from https://github.com/wiiudev/libwiiu, Extract to a folder.
2: Create or clone a project
Note: Old homebrew required that the project was created as a sub-folder of your libwiiu path. If you are creating a new project or cloning a recent homebrew, you can place its folder anywhere on your computer.
- Clone a project or create your new homebrew project into the libwiiu folder
3: Build your homebrew.
- Browse to the makefile location in a command line window and type "make".
Old homebrew might require you to merge the compiled homebrew binary inside an exploit binary. To do this, you need to use Libwiiu package and the provided Python script.
Since the release of the Homebrew Launcher, you don't need to merge your homebrew inside one of the existing exploit's binary anymore!
The homebrew launcher is already patching both the user and kernel space and grant these access to all launched homebrew.
If you develop a homebrew, you only need to compile it to an executable format (.elf) and launch if from the homebrew launcher, like you used to do on the Wii.
If you really need to inject your homebrew into an exploitable binary (for example to bypass the homebrew launcher completely, or if you are compiling the homebrew launcher itself), look into this spoiler:
This section is outdated, but kept for historical reason.
A more detailed (outdated, pre-homebrew launcher) video from BullyWiiPlaza:
Webkit exploit
The webkit exploit uses a vulnerability in the opensource Wii U-webkit.
To inject your homebrew into a browser exploit format, you need to generate a html file using libwiiu and python. Then launch it by loading the generated webpage hosted on a webserver.
To generate the html with your homebrew, open a command line in libwiiu folder and run build.py with the path to the homebrew.
Example to inject helloworld homebrew into html format:
LibStagefright exploit
The stagefright exploit uses a vulnerability in the media player using the mp4 format.
You can go here for the exploit. (more detailed instructions coming)
OSDriver kernel exploit
The kernel exploit is usually integrated into a user space exploit and run automatically after succesfully getting user space access.
To generate the kernel exploit to use with the webkit exploit, you need to compile the kernel example with libwiiu and python.
To generate the kernel exploit to use with the stagefright exploit, you need ... ?
To run homebrew requiring the kernel access, first run the kernel exploit which usually exits to home menu after succesful patching.
Then run your homebrew using one of the compatible user space exploit method (browser, stagefright, etc.).
IOS EXPLOIT
Unreleased
The webkit exploit uses a vulnerability in the opensource Wii U-webkit.
To inject your homebrew into a browser exploit format, you need to generate a html file using libwiiu and python. Then launch it by loading the generated webpage hosted on a webserver.
To generate the html with your homebrew, open a command line in libwiiu folder and run build.py with the path to the homebrew.
Example to inject helloworld homebrew into html format:
Code:
python build.py examples/helloworldLibStagefright exploit
The stagefright exploit uses a vulnerability in the media player using the mp4 format.
You can go here for the exploit. (more detailed instructions coming)
OSDriver kernel exploit
The kernel exploit is usually integrated into a user space exploit and run automatically after succesfully getting user space access.
To generate the kernel exploit to use with the webkit exploit, you need to compile the kernel example with libwiiu and python.
To generate the kernel exploit to use with the stagefright exploit, you need ... ?
To run homebrew requiring the kernel access, first run the kernel exploit which usually exits to home menu after succesful patching.
Then run your homebrew using one of the compatible user space exploit method (browser, stagefright, etc.).
IOS EXPLOIT
Unreleased
A more detailed (outdated, pre-homebrew launcher) video from BullyWiiPlaza:
Launching homebrew
there are two different methods to launch homebrew : homebrew launcher, or the old "individual homebrew injected into an exploit".
Most homebrew has been updated to use the homebrew launcher method, but this section will detail both method for historical reason.
1) The homebrew launcher method :
If your homebrew is an executable (.elf) then you only need to copy the homebrew to your SD card and launch it with the homebrew launcher.
- copy the homebrew in sd:/wiiu/apps/<name of your homebrew>/<filename>.elf
- optionally, copy the homebrew's meta.xml and icon.png in the same folder.
- install the homebrew launcher from the web browser, and select your homebrew to launch.
2) the old method, individual homebrew merged with an exploit.
All homebrew launched using this method need to be executed from the webkit browser and thus need to be hosted on a webserver.
It can be online webserver or locally hosted webpages.
A few online sites to use existing homebrew:
If you want to locally host some homebrew, you have to host it on your PC (the compiled html is by default in the www folder). You can do this anyway you want, but here are some examples:
It can be online webserver or locally hosted webpages.
A few online sites to use existing homebrew:
Code:
http://www.wiiubru.com
http://wiiulib.arndroid.nl
http://wj44.bplaced.comIf you want to locally host some homebrew, you have to host it on your PC (the compiled html is by default in the www folder). You can do this anyway you want, but here are some examples:
- With Python you can use the following commands to create a really simple python server:
Then point your WiiU Browser to http://yourinternalip:2343/Code:cd path/to/homebrew/ python -mSimpleHTTPServer 2343
- On windows, you can install wamp, xampp, or even easyphp.
- Or you can use a private Online webserver.
- A Video from BullyWiiPlaza on how to host on windows:
Existing homebrew
You can find a list of released homebrew on our wiki.
http://wiki.gbatemp.net/wiki/List_of_WiiU_homebrew
F.A.Q.
- Is my warranty void if I use this?
As the exploit doesn't permanently change anything, your warranty is completely fine.
- When will we get IOSU acces?
soon™, hykem/plutoo is working on it, stop complaining to them please
- Is there a firmware spoofer?
Yes
- Should I update?
NO. If you don't have to update, don't.
Last edited by Cyan,
, Reason: little typo