You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
- Thread starter SimonMKWii
- Start date
- Views 128,463
- Replies 329
- Likes 29
yesIs the fact that my sd is not exFAT (i dont remember what it is) the reason to why rawnand gets dumped in parts?
...
For reasons like this one, TX is working on an all-in-one
you'll still need this if you plan on downloading games from nintendo's cdn in the near future 0.o
- Joined
- Jul 15, 2014
- Messages
- 651
- Trophies
- 0
- Location
- Toronto, Ontario
- Website
- www.youtube.com
- XP
- 960
- Country

There is a lot of steps involved in this portion of everything to get the main app/downloader up and running.
It's at least a 20 step process.
Must be some way this can be streamlined or made into and app or executable on a pc.
It's hard to explain but I'm sure you get what direction I am going in. There must be a way to cut this 20 step process down to a 5 step process.
Every step has a chance for mistake and I'm sure one mistake along the process and you will fail.
Just an idea but should be considered.
Once we have the nand backup for example copy it to the computer and run a program that does most of the steps in one.
It's so difficult to do I'm having trouble following this tutorial the way it is described.
It's at least a 20 step process.
Must be some way this can be streamlined or made into and app or executable on a pc.
It's hard to explain but I'm sure you get what direction I am going in. There must be a way to cut this 20 step process down to a 5 step process.
Every step has a chance for mistake and I'm sure one mistake along the process and you will fail.
Just an idea but should be considered.
Once we have the nand backup for example copy it to the computer and run a program that does most of the steps in one.
you'll still need this if you plan on downloading games from nintendo's cdn in the near future 0.o
It's so difficult to do I'm having trouble following this tutorial the way it is described.
since the whole process is aids to figure out without any prior experience, I'll provide steps:
step 1: Download TegraRcmSmash https://gbatemp.net/threads/tegrarcmsmash-a-fusee-launcher-for-windows.502334/
step 2: Get payload https://gbatemp.net/threads/rcm-payload-hekate-mod-raw-full-nand-backup.502604/
step 3: Put an empty microSD card on exFAT with at least 32GB of space into your switch
step 4: Plug the switch into your comp, get into RCM
step 5: Boot hekate 1.3 and select rawNAND backup (something like that) and wait for it.
step 6: Get next payload (biskey) https://switchtools.sshnuke.net
step 7: Open the folder with TegraRcmSmash and place biskeydump.bin next to it
step 8: While in the TegraRcmSmash folder, Shift + Right Click in an empty space and press "Open command window here"
step 9: Plug the switch into your comp, get into RCM (microsd card not required)
step 10: Back where you opened the command window, type TegraRcmSmash.exe -w out/biskeydump.bin BOOT:0x0
step 11: biskeydump will now show your keys on the console AND on your computer in the command window
step 12: Open hacdiskmount https://switchtools.sshnuke.net
step 13: file > open > rawnand.bin (extracted from your switch)
step 14: select PRODINFO
step 15: put the keys in that it asks you for from the command window earlier.
step 16: You now have PRODINFO
step 17: download op's CertNXtractionPack
step 18: open up the pack and edit 00_generate_ssl_kek.py
step 19: insert the keys within the quotations
step 20: replace "ssl_aes_key_x" with "key_x_gak", and replace "ssl_rsa_key_y" with "rpk_key_y"
step 21: save it and drag your PRODINFO onto the 03_save_pft.bat
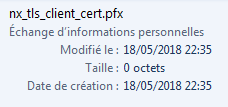
step 22: your cert is in the "Out" folder. gratz
I should add it in a new thread. So avoid that the last messages like this are not read and keep asking how to do it.How to obtain PRODINFO.bin file please ?
Ok thanks !I should add it in a new thread. So avoid that the last messages like this are not read and keep asking how to do it.
In step 20 you say to replace the "ssl_aes_key_x" with "key_x_gak", and replace "ssl_rsa_key_y" with "rpk_key_y". The output from the BIS payload gives me these keys. Which ones go where in the certnxtractionpack?since the whole process is aids to figure out without any prior experience, I'll provide steps:
step 1: Download TegraRcmSmash https://gbatemp.net/threads/tegrarcmsmash-a-fusee-launcher-for-windows.502334/
step 2: Get payload https://gbatemp.net/threads/rcm-payload-hekate-mod-raw-full-nand-backup.502604/
step 3: Put an empty microSD card on exFAT with at least 32GB of space into your switch
step 4: Plug the switch into your comp, get into RCM
step 5: Boot hekate 1.3 and select rawNAND backup (something like that) and wait for it.
step 6: Get next payload (biskey) https://switchtools.sshnuke.net
step 7: Open the folder with TegraRcmSmash and place biskeydump.bin next to it
step 8: While in the TegraRcmSmash folder, Shift + Right Click in an empty space and press "Open command window here"
step 9: Plug the switch into your comp, get into RCM (microsd card not required)
step 10: Back where you opened the command window, type TegraRcmSmash.exe -w out/biskeydump.bin BOOT:0x0
step 11: biskeydump will now show your keys on the console AND on your computer in the command window
step 12: Open hacdiskmount https://switchtools.sshnuke.net
step 13: file > open > rawnand.bin (extracted from your switch)
step 14: select PRODINFO
step 15: put the keys in that it asks you for from the command window earlier.
step 16: You now have PRODINFO
step 17: download op's CertNXtractionPack
step 18: open up the pack and edit 00_generate_ssl_kek.py
step 19: insert the keys within the quotations
step 20: replace "ssl_aes_key_x" with "key_x_gak", and replace "ssl_rsa_key_y" with "rpk_key_y"
step 21: save it and drag your PRODINFO onto the 03_save_pft.bat
step 22: your cert is in the "Out" folder. gratz
HWI: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
SBK: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
TSEC KEY: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
DEVICE KEY: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 0 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 0 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 1 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 1 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 2 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 2 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 3 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 3 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
In step 20 you say to replace the "ssl_aes_key_x" with "key_x_gak", and replace "ssl_rsa_key_y" with "rpk_key_y". The output from the BIS payload gives me these keys. Which ones go where ni the certnxtractionpack?
HWI: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
SBK: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
TSEC KEY: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
DEVICE KEY: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 0 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 0 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 1 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 1 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 2 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 2 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 3 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 3 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 0 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 0 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
So just to be clear, are you telling me to replece the words "ssl_aes_key_x" with "key_x_gak"? Or are you just saying put those keys in inside the parenthesis? Also what about the rsa_private_kek_generation_source and master_key? Do I need to change those lines or insert something?BIS KEY 0 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 0 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
Last question for more clarity. When I insert my BIS KEY 0 (crypt) and BIS KEY (tweak) keys do I leave the single apostrophe or just delete everything between ( and ) and replace with key?
No, no, no!!!BIS KEY 0 (crypt): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
BIS KEY 0 (tweak): xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
That's completely incorrect.
Assuming you're on 5.0.2, find "F5D06292E093C651E67AA7C1A93B3880.nca" then decrypt and extract it in hactool.
Open the main file in a hex editor, then search for the hint bytes I gave in the script. Both are 16-bytes (32 characters) long.
I'm on 4.1No, no, no!!!
That's completely incorrect.
Assuming you're on 5.0.2, find "F5D06292E093C651E67AA7C1A93B3880.nca" then decrypt and extract it in hactool.
Open the main file in a hex editor, then search for the hint bytes I gave in the script. Both are 16-bytes (32 characters) long.
--------------------- MERGED ---------------------------
How do I find that .nca file on 4.1? I followed the 20 steps by @aslk and I don't have that fileNo, no, no!!!
That's completely incorrect.
Assuming you're on 5.0.2, find "F5D06292E093C651E67AA7C1A93B3880.nca" then decrypt and extract it in hactool.
Open the main file in a hex editor, then search for the hint bytes I gave in the script. Both are 16-bytes (32 characters) long.
No, no, no!!!
That's completely incorrect.
Assuming you're on 5.0.2, find "F5D06292E093C651E67AA7C1A93B3880.nca" then decrypt and extract it in hactool.
Open the main file in a hex editor, then search for the hint bytes I gave in the script. Both are 16-bytes (32 characters) long.
o shit, so I did it wrong? rip
If you're on 4.1.0, find "1FD444259440E23722CC0E0D0D8D0F0B.nca" in the system partition, and extract the exefs in hactool.I'm on 4.1
--------------------- MERGED ---------------------------
How do I find that .nca file on 4.1? I followed the 20 steps by @aslk and I don't have that file
Then, put the main file in a hex editor, and search for the leading bytes.
Not sure how to find that .nca in the system partition. Do I use hacdiskmount to extract system first to a bin file and then hactool to find that .nca file? I'm not sure how to use hactoolIf you're on 4.1.0, find "1FD444259440E23722CC0E0D0D8D0F0B.nca" in the system partition, and extract the exefs in hactool.
Then, put the main file in a hex editor, and search for the leading bytes.
It's a bit annoying to keep messaging back and forth, do you have a Discord account?Not sure how to find that .nca in the system partition. Do I use hacdiskmount to extract system first to a bin file and then hactool to find that .nca file? I'm not sure how to use hactool
If so, hop onto my Switch Hacking / general gaming server! Anyone is welcome.
We'll help you out, (unless you ask how to get free games.)
Invite link: https://discord.gg/K5nyTyj
Similar threads
-
- Article
- Replies
- 287
- Views
- 150K
- Replies
- 553
- Views
- 270K
- Replies
- 147
- Views
- 54K
Site & Scene News
New Hot Discussed
-
-
25K views
Wii U and 3DS online services shutting down today, but Pretendo is here to save the day
Today, April 8th, 2024, at 4PM PT, marks the day in which Nintendo permanently ends support for both the 3DS and the Wii U online services, which include co-op play...by ShadowOne333 179 -
21K views
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other... -
18K views
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we... -
17K views
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 96 -
15K views
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems... -
13K views
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 113 -
12K views
A prototype of the original "The Legend of Zelda" for NES has been found and preserved
Another video game prototype has been found and preserved, and this time, it's none other than the game that spawned an entire franchise beloved by many, the very...by ShadowOne333 31 -
10K views
Anbernic reveals specs details of pocket-sized RG28XX retro handheld
Anbernic is back with yet another retro handheld device. The upcoming RG28XX is another console sporting the quad-core H700 chip of the company's recent RG35XX 2024... -
10K views
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another... -
10K views
Nintendo "Indie World" stream announced for April 17th, 2024
Nintendo has recently announced through their social media accounts that a new Indie World stream will be airing tomorrow, scheduled for April 17th, 2024 at 7 a.m. PT...by ShadowOne333 53
-
-
-
179 replies
Wii U and 3DS online services shutting down today, but Pretendo is here to save the day
Today, April 8th, 2024, at 4PM PT, marks the day in which Nintendo permanently ends support for both the 3DS and the Wii U online services, which include co-op play...by ShadowOne333 -
113 replies
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 -
97 replies
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we...by Scarlet -
96 replies
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 -
80 replies
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other...by Chary -
78 replies
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems...by Chary -
67 replies
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal...by relauby -
55 replies
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another...by Chary -
53 replies
Nintendo "Indie World" stream announced for April 17th, 2024
Nintendo has recently announced through their social media accounts that a new Indie World stream will be airing tomorrow, scheduled for April 17th, 2024 at 7 a.m. PT...by ShadowOne333 -
52 replies
The FCC has voted to restore net neutrality, reversing ruling from 2017
In 2017, the United States Federal Communications Commission (FCC) repealed net neutrality. At the time, it was a major controversy between internet service providers...by Chary
-
Popular threads in this forum
General chit-chat
-
-
-
 @
Psionic Roshambo:
I like that games can be fixed after the fact, hate that it's being abused via beta tests... And DLC... I was a 7800 owner back in the day and loved Impossible Mission, turns out I couldn't beat it because it was actually impossible lol
@
Psionic Roshambo:
I like that games can be fixed after the fact, hate that it's being abused via beta tests... And DLC... I was a 7800 owner back in the day and loved Impossible Mission, turns out I couldn't beat it because it was actually impossible lol -
 @
Psionic Roshambo:
I never knew about it at the time but a fixed version was available but you had to mail in your broken copy lol
@
Psionic Roshambo:
I never knew about it at the time but a fixed version was available but you had to mail in your broken copy lol -
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
 @
Psionic Roshambo:
https://youtu.be/Gy3BOmvLf2w?list=OLAK5uy_k27izUIERfT-RIE1qN1CHIOIkW4h5A9BY Play this song if Hippies are bothering you! lol
@
Psionic Roshambo:
https://youtu.be/Gy3BOmvLf2w?list=OLAK5uy_k27izUIERfT-RIE1qN1CHIOIkW4h5A9BY Play this song if Hippies are bothering you! lol -
-
-
-