So in that case, it's not a bootrom exploit itself. Good god.THAT RSA CODE IS IN THE PROTECTED BOOTROM
Good. God.
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Homebrew SigHax Updates and Discussion Thread
- Thread starter adrifcastr
- Start date
- Views 469,590
- Replies 3,813
- Likes 43
cmon I´m feeling like the water type z-move was used on meSo in that case, it's not a bootrom exploit itself. Good god.
I can't believe I'm reading thisSo in that case, it's not a bootrom exploit itself. Good god.
I just posted that and you said I was rude.updated the op and thanks
Just ignore the people who don't realise exploiting a bug in the bootrom is a bootrom exploitcmon I´m feeling like the water type z-move was used on me
Last edited by KevinX8,
lmao I'm done.
The sigpatch doesn't exploit the bootrom itself, the actual bootrom exploit exploits it, lmao.
All the sigpatch does is use the exploited bootrom to it's advantage, to enable FW signing.
Have a nice day!
The sigpatch doesn't exploit the bootrom itself, the actual bootrom exploit exploits it, lmao.
All the sigpatch does is use the exploited bootrom to it's advantage, to enable FW signing.
Have a nice day!
totally confused with everything now, half the users here say my op is correct he other ones say I completely messed it upI just posted that and you said I was rude.
--------------------- MERGED ---------------------------
k thanksJust ignore the people who don't release exploiting a bug in the bootrom is a bootrom exploit
We aren't touching the bootrom, it's readonly anway, all we are doing is exploiting the fact it only requires half assed signatures to load the firmware which can be brute forced since its only a couple bytes that are requiredlmao I'm done.
The sigpatch doesn't exploit the bootrom itself, the actual bootrom exploit exploits it, lmao.
All the sigpatch does is use the exploited bootrom to it's advantage, to enable FW signing.
Have a nice day!
I think the misunderstanding here is the fact that an exploit, in your definition, can only mean taking over control of the code. That is not the case, defeating the bootrom's ability to verify firmware code as correctly signed is definitely exploiting a flaw in the bootrom itself.lmao I'm done.
The sigpatch doesn't exploit the bootrom itself, the actual bootrom exploit exploits it, lmao.
All the sigpatch does is use the exploited bootrom to it's advantage, to enable FW signing.
Have a nice day!
Last edited by zoogie,
I think the misunderstanding here is the fact that an exploit, in your definition, can only mean taking over control of the code. That is not the case, defeating the bootrom's ability to verify firmware code as correctly signed is definitely exploit a flaw in the bootrom itself.
We aren't touching the bootrom, it's readonly anway, all we are doing is exploiting the fact it only requires half assed signatures to load the firmware which can be brute forced since its only a couple bytes that are required
Fine btw @KevinX8 added your post to my signature actually that was really funny
XD You might wanna edit it thought lol it should be "realise" not "release" oops lolFine btw @KevinX8 added your post to my signature actually that was really funny
I'm suddenly and inexplicably reminded of grade school. Wonder why...
Anyway, I agree with @Crystal the Glaceon, the more options the community has, the better. Especially in light of Ninty's sudden enhanced interest in crushing fan games and homebrew.
Anyway, I agree with @Crystal the Glaceon, the more options the community has, the better. Especially in light of Ninty's sudden enhanced interest in crushing fan games and homebrew.
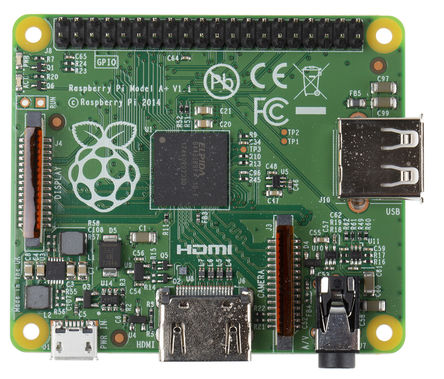
pretty muchit basically turns this

into this
gonna do xDXD You might wanna edit it thought lol it should be "realise" not "release" oops lol
" relealise" Achievment unlocked! Invented a new word when fixing an errorgonna do xD

damn" relealise" Achievment unlocked! Invented a new word when fixing an error

 that literally killed me, I´m dumb
that literally killed me, I´m dumbWhat's up with the scene lately? Everyone has become such naysayers. Like this is cool stuff! Another means of booting into CFW? And even faster than A9LH! That's cool as hell!
I don't remember this much pissing and moaning when A9LH was revealed.
I don't remember this much pissing and moaning when A9LH was revealed.
What's up with the scene lately? Everyone has become such naysayers. Like this is cool stuff! Another means of booting into CFW? And even faster than A9LH! That's cool as hell!
I don't remember this much pissing and moaning when A9LH was revealed.
Some have been spoilt for choice with CFW and means of putting it on their 3DS'.
They'd no doubt be a little more humble if things like this were held back until it's needed instead of just throwing it into the basket of current CFW installation methods etc.
Or we could just be happy that we are getting somewhere. This is actually big stuff! We will have even more control over the system than ever before!Some have been spoilt for choice with CFW and means of putting it on their 3DS'.
They'd no doubt be a little more humble if things like this were held back until it's needed instead of just throwing it into the basket of current CFW installation methods etc.
People are acting like this is some small project they could have done in a few hours, instead of the major achievement that took years to accomplish.
Last edited by The Catboy,
This is quite possibly the dumbest thing I've read all day.lmao I'm done.
The sigpatch doesn't exploit the bootrom itself, the actual bootrom exploit exploits it, lmao.
All the sigpatch does is use the exploited bootrom to it's advantage, to enable FW signing.
Have a nice day!
The boot ROM has a vulnerability in its RSA signature verification; therefore, something that takes advantage of it is a boot ROM exploit. What else would it be, an Internet Explorer exploit?
...unless you're trying to say that the only possible "boot ROM exploit" is a way to dump the boot ROM.
EDIT: Oh, so you're trying to be pedantic by claiming the signature patch itself isn't an "exploit", but the program used to generate the patch is. Or something like that; I don't speak fluent noob.
Last edited by GerbilSoft,
Similar threads
Site & Scene News
New Hot Discussed
-
-
29K views
Atmosphere CFW for Switch updated to pre-release version 1.7.0, adds support for firmware 18.0.0
After a couple days of Nintendo releasing their 18.0.0 firmware update, @SciresM releases a brand new update to his Atmosphere NX custom firmware for the Nintendo...by ShadowOne333 110 -
22K views
Wii U and 3DS online services shutting down today, but Pretendo is here to save the day
Today, April 8th, 2024, at 4PM PT, marks the day in which Nintendo permanently ends support for both the 3DS and the Wii U online services, which include co-op play...by ShadowOne333 179 -
18K views
GBAtemp Exclusive Introducing tempBOT AI - your new virtual GBAtemp companion and aide (April Fools)
Hello, GBAtemp members! After a prolonged absence, I am delighted to announce my return and upgraded form to you today... Introducing tempBOT AI 🤖 As the embodiment... -
15K views
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we... -
15K views
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other... -
14K views
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 96 -
14K views
MisterFPGA has been updated to include an official release for its Nintendo 64 core
The highly popular and accurate FPGA hardware, MisterFGPA, has received today a brand new update with a long-awaited feature, or rather, a new core for hardcore...by ShadowOne333 54 -
11K views
"TMNT: The Hyperstone Heist" for the SEGA Genesis / Mega Drive gets a brand new DX romhack with new features
The romhacking community is always a source for new ways to play retro games, from completely new levels or stages, characters, quality of life improvements, to flat...by ShadowOne333 36 -
10K views
"Sonic 3" movie has wrapped production & Knuckles series gets its official poster
Quite a bit of news have unfolded in the past couple of days in regards to the Sonic franchise, for both its small and big screens outings. To start off, the...by ShadowOne333 27 -
10K views
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 113
-
-
-
179 replies
Wii U and 3DS online services shutting down today, but Pretendo is here to save the day
Today, April 8th, 2024, at 4PM PT, marks the day in which Nintendo permanently ends support for both the 3DS and the Wii U online services, which include co-op play...by ShadowOne333 -
169 replies
GBAtemp Exclusive Introducing tempBOT AI - your new virtual GBAtemp companion and aide (April Fools)
Hello, GBAtemp members! After a prolonged absence, I am delighted to announce my return and upgraded form to you today... Introducing tempBOT AI 🤖 As the embodiment...by tempBOT -
113 replies
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 -
110 replies
Atmosphere CFW for Switch updated to pre-release version 1.7.0, adds support for firmware 18.0.0
After a couple days of Nintendo releasing their 18.0.0 firmware update, @SciresM releases a brand new update to his Atmosphere NX custom firmware for the Nintendo...by ShadowOne333 -
97 replies
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we...by Scarlet -
96 replies
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 -
77 replies
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other...by Chary -
55 replies
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another...by Chary -
54 replies
MisterFPGA has been updated to include an official release for its Nintendo 64 core
The highly popular and accurate FPGA hardware, MisterFGPA, has received today a brand new update with a long-awaited feature, or rather, a new core for hardcore...by ShadowOne333 -
53 replies
Nintendo "Indie World" stream announced for April 17th, 2024
Nintendo has recently announced through their social media accounts that a new Indie World stream will be airing tomorrow, scheduled for April 17th, 2024 at 7 a.m. PT...by ShadowOne333
-
Popular threads in this forum
General chit-chat
- No one is chatting at the moment.
-
-
-
-
 @
Psionic Roshambo:
Well it helps when you get every Eidos game ever made for like 40 bucks on a 90% off Steam sale lol
@
Psionic Roshambo:
Well it helps when you get every Eidos game ever made for like 40 bucks on a 90% off Steam sale lol -
-
 @
Psionic Roshambo:
Spent like 200 bucks one year doing that they had all kinds of collections on sale
@
Psionic Roshambo:
Spent like 200 bucks one year doing that they had all kinds of collections on sale -
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-





