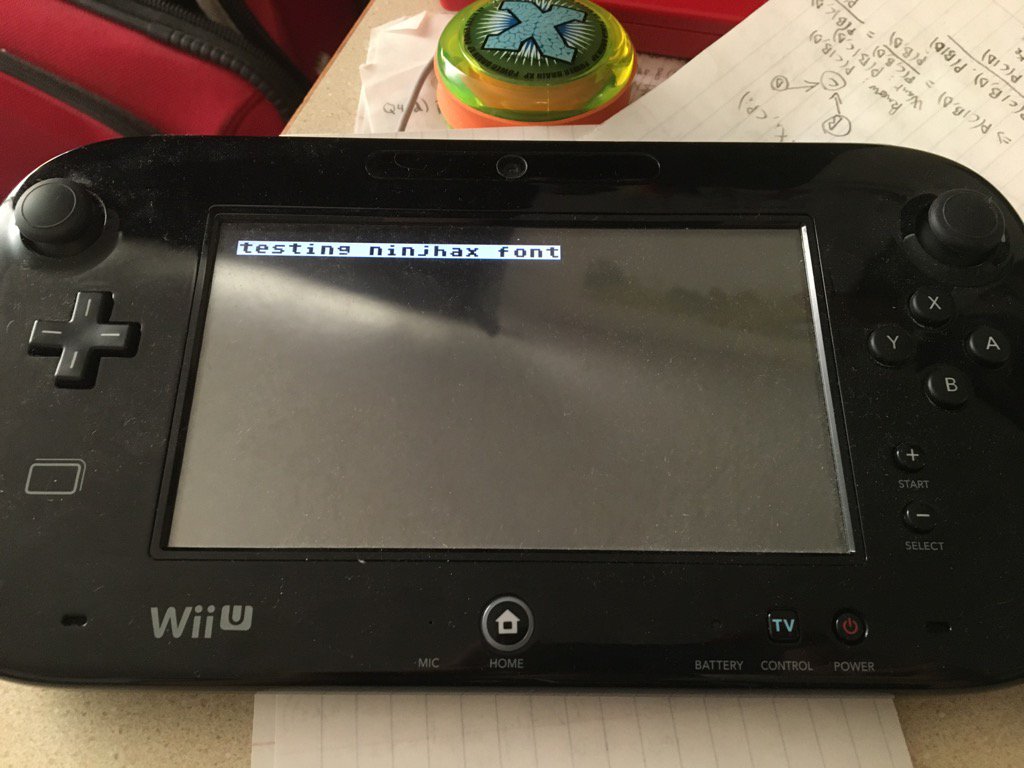
I think hes working on HBL-USo what´s with this screenshot by Smealum?
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
and what does it mean?I think hes working on HBL-U
sorry Im noob
remember Homebrew Launcher for Wii/3DS?and what does it mean?
sorry Im noob
- Joined
- Jan 7, 2014
- Messages
- 14,604
- Trophies
- 4
- Location
- Another World
- Website
- www.gbatemp.net
- XP
- 25,280
- Country

Exploiting that SAVE ability I seedecrypt shit and use it to "time-travel"
Homebrew launcher (hbl).and what does it mean?
sorry Im noob
Isn't it dying*? lolbrain-cells are dieing.
I think its an abbreviation for Homebrew Loader-U.and what does it mean?
sorry Im noob
It probably means homebrew launcher for Wii U like the one for 3DS. You know the launcher app where you runs other homebrew apps from.and what does it mean?
sorry Im noob
See the video to get a better idea what homebrew launcher is
Last edited by tivu100,
What mean iv? Is an abbreviation of something? If I understand, in the boot0 you found the boot1 iv used to descript the first 0x10 bytes of the boot1? I love that shit is very interesting..yep, and the bootrom contains the expresso iv, whilst IOSU contains the starbuck iv (while we are talking about hardcoded crap)
What mean iv? Is an abbreviation of something? If I understand, in the boot0 you found the boot1 iv used to descript the first 0x10 bytes of the boot1? I love that shit is very interesting..
It's the initialization vector, something that's used with the key to perform decryption (in this case, of the first 0x10 bytes). It gives a bit more security, since the key isn't the only thing you need for decryption.
Is there any news on EMUNAND development for Wii U, @Marionumber1 ?
Nothing I've heard from Hykem on it.
you need to elaborate what not working isWhy tubehax 107.211.140.065 dns not working in my wiiu plz help.i connected to the home wifi and putted this ip in dns.plz help
does it still trying to update despite you've set tubehax? or does your internet stop working after setting up tubehax?
and did you set tubehax on the wii u itself or on the router?
you need to elaborate what not working is
does it still trying to update despite you've set tubehax? or does your internet stop working after setting up tubehax?
and did you set tubehax on the wii u itself or on the router?
I'm pretty sure he's a troll
first time seeing that id, so I know nothing whether he's a troll or not 
so you need to resort to other ways to block update
some ISP (mine included) does not allow changing DNSInternet not connecting after setup dns in wiiu
so you need to resort to other ways to block update
Last edited by Garou,
Presumably, it was reverse-engineered out of boot0, which has been possible to dump for almost 2 years.
Well, that was embarassing <_< Of course whatever that decrypts it needs to have the IV, and thus he got it from there. Maybe it was good that I got some sleep after writing it ;_;
None the less, thanks for the response mate!
What mean iv? Is an abbreviation of something? If I understand, in the boot0 you found the boot1 iv used to descript the first 0x10 bytes of the boot1? I love that shit is very interesting..
MN1 already answered you on what an IV is. Anyway, if you find it interesting, you should begin reading up on it - it is indeed very interesting!
Here is a good example for, why you need to utilize your cipher in a way that uses an IV: http://i.stack.imgur.com/bXAUL.png
Electronic Code Book mode (ECB) is one where you just encrypt your plaintext blocks each for themselves, so every white group of pixels becomes the same encrypted something else, etc. As you can see, it is still pretty easy to see the places that was white before, as all identical blocks all have the new same color/look now. Chain Block Cipher mode (and pretty much all other modes) on the other hand also utilises the value of the earlier block in the encryption of the new block, thus two identical blocks will never look the same.
The trick here is that the very first block we encrypt, will have no block before it, which has a value we can use in the encryption of this block. Thus we need an initialisation vector.
Its really fundamental cryptology, and if you like it - read up on it! Modes of operation for ciphers are one of the easiest concepts to grasp as a start, as it involves no math really. (So gogogo
Last edited by oPolo,
vinscool was one of them, so probably off-topic posts.This thread gets even more confusing if mods delete posts without giving a reason.
Maybe because it's forbidden to post the keys ?I was posted the isou key of wiiu 5.5.1...but I don't know why they removed it.and I also don't know what to do with this isou key to hack wiiu
Similar threads
- Replies
- 0
- Views
- 2K
- Replies
- 45
- Views
- 31K
- Replies
- 2
- Views
- 2K
- Replies
- 5
- Views
- 1K
Site & Scene News
New Hot Discussed
-
-
20K views
Majora’s Mask PC port 2Ship2Harkinian gets its first release
After several months of work, the Harbour Masters 64 team have released their first public build of 2Ship2Harkinian, a feature-rich Majora's Mask PC port. This comes... -
19K views
Mario Builder 64 is the N64's answer to Super Mario Maker
With the vast success of Super Mario Maker and its Switch sequel Super Mario Maker 2, Nintendo fans have long been calling for "Maker" titles for other iconic genres... -
19K views
Modders hint at potential kernel exploit hack for Xbox One consoles
It's been a while since Microsoft released the Xbox One, and despite its age, there haven't been any reliable softmod methods to hack the console. Until now. A post... -
17K views
The founder of Oculus is releasing a $199 FPGA Game Boy system
Palmer Luckey is known for his pursuits into the world of virtual reality, having founded Oculus and designed the Rift VR headset. Prior to the $2 billion dollar... -
14K views
Nintendo takes down the Breath of the Wild randomizer mod from Gamebanana
Another day, another Nintendo DMCA takedown against fan-made content. Just a few minutes ago, Nintendo issued a DMCA takedown notice against a widely known and...by ShadowOne333 104 -
14K views
The Kingdom Hearts games are coming to Steam
After a little more than three years of exclusivity with the Epic Games Store, Square Enix has decided to bring their beloved Kingdom Hearts franchise to Steam. The... -
12K views
Select PlayStation 2 games are coming to PlayStation 5
Sony is once more attempting to reintroduce players to their older library of games by re-releasing classic PlayStation 2 titles onto the PlayStation Store. During... -
11K views
Skyward Sword HD randomizer announced with release date and trailer
Skyward Sword is a divisive title in the Zelda series. Hailed with praise at launch with a 93 Metacritic average, the game since received criticism for the... -
10K views
PlayStation State of Play May 2024 showcase - God of War: Ragnarok coming to PC
The latest State of Play is here. This is PlayStation's Summer showcase, providing updates to new updates on upcoming games and brand new reveals. The 35-minute... -
9K views
Nintendo acquires company behind Mortal Kombat 1 and Hogwarts Legacy ports on Switch, "Shiver Entertainment Inc."
Nintendo is having quite the successful console generation with the Nintendo Switch, and with the follow-up to the Switch already on the horizon confirmed by...by ShadowOne333 48
-
-
-
169 replies
The founder of Oculus is releasing a $199 FPGA Game Boy system
Palmer Luckey is known for his pursuits into the world of virtual reality, having founded Oculus and designed the Rift VR headset. Prior to the $2 billion dollar...by Chary -
118 replies
Modders hint at potential kernel exploit hack for Xbox One consoles
It's been a while since Microsoft released the Xbox One, and despite its age, there haven't been any reliable softmod methods to hack the console. Until now. A post...by Chary -
108 replies
Majora’s Mask PC port 2Ship2Harkinian gets its first release
After several months of work, the Harbour Masters 64 team have released their first public build of 2Ship2Harkinian, a feature-rich Majora's Mask PC port. This comes...by Scarlet -
104 replies
Nintendo takes down the Breath of the Wild randomizer mod from Gamebanana
Another day, another Nintendo DMCA takedown against fan-made content. Just a few minutes ago, Nintendo issued a DMCA takedown notice against a widely known and...by ShadowOne333 -
91 replies
The Kingdom Hearts games are coming to Steam
After a little more than three years of exclusivity with the Epic Games Store, Square Enix has decided to bring their beloved Kingdom Hearts franchise to Steam. The...by Chary -
79 replies
Select PlayStation 2 games are coming to PlayStation 5
Sony is once more attempting to reintroduce players to their older library of games by re-releasing classic PlayStation 2 titles onto the PlayStation Store. During...by Chary -
66 replies
Mario Builder 64 is the N64's answer to Super Mario Maker
With the vast success of Super Mario Maker and its Switch sequel Super Mario Maker 2, Nintendo fans have long been calling for "Maker" titles for other iconic genres...by Scarlet -
64 replies
PlayStation State of Play May 2024 showcase - God of War: Ragnarok coming to PC
The latest State of Play is here. This is PlayStation's Summer showcase, providing updates to new updates on upcoming games and brand new reveals. The 35-minute...by Chary -
62 replies
Summer Game Fest 2024 coverage - Civilization VII announced
E3 may be gone, but it's not forgotten, as the trend of a massive Summer video game showcase still lives on in the form of the Summer Game Fest. Promising two hour of...by Chary -
55 replies
Doom for SNES full source code released by former Sculptured Software employees
The complete source code for the Super Nintendo Entertainment System (SNES) version of Doom has been released on archive.org. Although some of the code was partially...by shaunj66
-
Popular threads in this forum
General chit-chat
-
 Xdqwerty
Loading…what are you looking at?
Xdqwerty
Loading…what are you looking at? -
 K3Nv2
Loading…
K3Nv2
Loading… -
 NinStar
Loading…
NinStar
Loading… -
 BakerMan
Loading…I rather enjoy a life of taking it easy. I haven't reached that life yet though.
BakerMan
Loading…I rather enjoy a life of taking it easy. I haven't reached that life yet though.
-
 @
Xdqwerty:
Also, do songs that werent made for a videogame but do appear in a videogame count as game songs @SylverReZ?+1
@
Xdqwerty:
Also, do songs that werent made for a videogame but do appear in a videogame count as game songs @SylverReZ?+1 -
-
-
-
-
-
-
-
-
-
-
 @
Xdqwerty:
@SylverReZ, the first one is a dnb song i put and the second one is a song that became popular due to gd that i really like
@
Xdqwerty:
@SylverReZ, the first one is a dnb song i put and the second one is a song that became popular due to gd that i really like -
 @
BakerMan:
i would say if it's not for a video game but it's in a video game, it counts if it's not a music game+1
@
BakerMan:
i would say if it's not for a video game but it's in a video game, it counts if it's not a music game+1
so it counts for hotline miami and geometry dash, but not just dance or beat saber -
-
-
-
-
-
-
-
-
-
-
-








