Would it be possible to make it so that firm0/firm1 write permissions are separate from the normal sysnand/emunand write permission? That would make it somewhat safer for a9lh users since firm0/firm1 would remain read only (unless separately overridden) even when the rest of the system is writable.
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Occasional failed boots on HBL are normal, as the Brahma entrypoint is not perfectly stable.
Sure there is! With A9LH installed, you have access to Select9 and CTR Boot Manager9. Without A9LH, you still have CTR Boot Manager (which you'd have to use as a HBL replacement). In general, Homebrew Launcher is a better entrypoint than MSET and A9LH > HBL > MSET.
Thanks for the explaining. Is Ctr bootmanager9 this or there is another one? https://github.com/Cpasjuste/CtrBootManager
and an other one question: does boot.3dsx files have slow boot rate?
If it were a Linux system perhaps, don't know about 3ds thoughWould it be possible to make it so that firm0/firm1 write permissions are separate from the normal sysnand/emunand write permission? That would make it somewhat safer for a9lh users since firm0/firm1 would remain read only (unless separately overridden) even when the rest of the system is writable.
Would it be possible to make it so that firm0/firm1 write permissions are separate from the normal sysnand/emunand write permission? That would make it somewhat safer for a9lh users since firm0/firm1 would remain read only (unless separately overridden) even when the rest of the system is writable.
It would, but it would only serve to make things more complicated. All you have to do to keep FIRM unchanged is not write to the FIRM0.bin / FIRM1.bin and NAND.bin virtual files. If you want a A9LH preserving restore option, use D9WIP.If it were a Linux system perhaps, don't know about 3ds though
Yes. And no, boot.3dsx has a perfect boot rate.Thanks for the explaining. Is Ctr bootmanager9 this or there is another one? https://github.com/Cpasjuste/CtrBootManager
and an other one question: does boot.3dsx files have slow boot rate?
Occasional failed boots on HBL are normal, as the Brahma entrypoint is not perfectly stable.
Sure there is! With A9LH installed, you have access to Select9 and CTR Boot Manager9. Without A9LH, you still have CTR Boot Manager (which you'd have to use as a HBL replacement). In general, Homebrew Launcher is a better entrypoint than MSET and A9LH > HBL > MSET.
Don't forget BootCTR and BootCTR9. Another hotkey option, but with a configuration file. With the former, you can have hotkeys in MenuHax. I used to run CTR Boot Manager myself before switching to A9LH. I should probably explain at this time that I used the "Cakes" option because it's actually a "BootCTR9" option that sets Cakes up as one of the choices. However, I've actually got AuReiNAND as the default for several reasons. I just don't use it's chain loader because it seems to have a slight delay booting tools like D9, whereas BootCTR9 doesn't seem to slow AuReiNAND down noticeably at all. Since that was part of the tutorial, I wasn't aware there was a CBM9 at first, but I think I've decided I like the hotkeys more. Though I have downloaded CBM9 to try it out.
Interestingly, the regular BootCTR .3dsx has the name of the .ini file in plain text. You can easily change it with a hex editor so that you can run both on the same system. Very useful if you have a Gateway while we wait for the GW A9LH payload to hit. I've setup MenuHax to L on my 9.2 EmuNAND (because AuReiNAND uses L to boot EmuNAND using NATIVE_FIRM 9.0), and I've set the BootCTR default to Gateway (and I put the HBL menu to B just for a faster way to launch it). With that setup, I can just hold L to boot GW (I want it to stop at the menu anyway, so I can pick SysNAND mode).
Oh yeah, I noticed something weird on my EUR N3DS XL. For some odd reason, GodMode9 gives me "Warning: slot0x05 crypto fail! Could not set up slot0x05keyY. Continue?" when it starts up. It's only doing it on the EUR (Australian) device. Creating "aeskeydb.bin" in Decrypt9 caused the message to go away, so, it's not even a problem now. Still, I thought you (and anyone else with an AUS unit) might want to know.
Last edited by Kazuma77,
Oh yeah, I noticed something weird on my EUR N3DS XL. For some odd reason, GodMode9 gives me "Warning: slot0x05 crypto fail! Could not set up slot0x05keyY. Continue?" when it starts up. It's only doing it on the EUR (Australian) device. Creating "aeskeydb.bin" in Decrypt9 caused the message to go away, so, it's not even a problem now. Still, I thought you (and anyone else with an AUS unit) might want to know.
@d0k3
I'm getting the same with the latest github commit.
Oh yeah, I noticed something weird on my EUR N3DS XL. For some odd reason, GodMode9 gives me "Warning: slot0x05 crypto fail! Could not set up slot0x05keyY. Continue?" when it starts up. It's only doing it on the EUR (Australian) device. Creating "aeskeydb.bin" in Decrypt9 caused the message to go away, so, it's not even a problem now. Still, I thought you (and anyone else with an AUS unit) might want to know.
Are both of your N3DSes (these are N3DSes, right?) AUS units? Running from A9LH? Do the CTRNAND partitions show up in GodMode9? And, did you have the slot0x05keyY.bin file before you got that message?@d0k3I'm getting the same with the latest github commit.
Background to this: That message only comes up if GodMode9 can't verify slot 0x05 crypto. In theory, that happens in two cases.. (1) on A9LH, if you don't have the slot0x05keyY.bin or aeskeydb.bin file, (2) if you have a corrupt slot0x05keyY.bin or aeskeydb.bin file. In that case, on N3DS (not on O3DS) we would not have access to the CTRNAND partition.
I also already have a suspicion what may cause this, and if one of you (or both!) could dump the first 16 byte of their decrypted CTRNAND_fat.bin, I could verify.
Are both of your N3DSes (these are N3DSes, right?) AUS units? Running from A9LH? Do the CTRNAND partitions show up in GodMode9? And, did you have the slot0x05keyY.bin file before you got that message?
Background to this: That message only comes up if GodMode9 can't verify slot 0x05 crypto. In theory, that happens in two cases.. (1) on A9LH, if you don't have the slot0x05keyY.bin or aeskeydb.bin file, (2) if you have a corrupt slot0x05keyY.bin or aeskeydb.bin file. In that case, on N3DS (not on O3DS) we would not have access to the CTRNAND partition.
I also already have a suspicion what may cause this, and if one of you (or both!) could dump the first 16 byte of their decrypted CTRNAND_fat.bin, I could verify.
JP n3ds w/ a9lh. After generating aeskeydb.bin with Decrypt9, GodMode9 stops displaying the error message. I've been using the same slot0x05KeyY.bin since the beginning.
Okay, that helps! That aeskeydb.bin file... is it in the Decrypt9/ folder or in the SD root now? What happens if you move it?JP n3ds w/ a9lh. After generating aeskeydb.bin with Decrypt9, GodMode9 stops displaying the error message. I've been using the same slot0x05KeyY.bin since the beginning.
Okay, that helps! That aeskeydb.bin file... is it in the Decrypt9/ folder or in the SD root now? What happens if you move it?
I never made a Decrypt9/ folder
i'm pretty sure any cfw other than aureinand will let you access recovery to cancel an update. I was also under the impression doing this will not brick, only if you choose to proceed with recovery action while on a9lh may it brick or uninstall a9lh.
Anyone else know the answer to this? Anyways, if I were still using emunand at this point I'd also have an updated sysnand too, perhaps you must have gateway I guess?
Even accessing recovery on a A9LH New 3DS will brick it. However, it does not brick Old 3DS.
Are both of your N3DSes (these are N3DSes, right?) AUS units? Running from A9LH? Do the CTRNAND partitions show up in GodMode9? And, did you have the slot0x05keyY.bin file before you got that message?
Background to this: That message only comes up if GodMode9 can't verify slot 0x05 crypto. In theory, that happens in two cases.. (1) on A9LH, if you don't have the slot0x05keyY.bin or aeskeydb.bin file, (2) if you have a corrupt slot0x05keyY.bin or aeskeydb.bin file. In that case, on N3DS (not on O3DS) we would not have access to the CTRNAND partition.
I also already have a suspicion what may cause this, and if one of you (or both!) could dump the first 16 byte of their decrypted CTRNAND_fat.bin, I could verify.
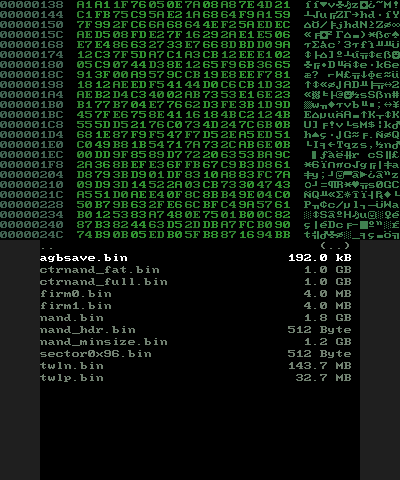
Well, I've had the slot0x05KeyY.bin file on the device the entire time. So it can't be case 1. And Decrypt9 used the file to build a working aeskeydb.bin, so it can't be case 2 either. Actually, I've just confirmed my USA N3DS XL does the same. It's just that I had already created aeskeydb.bin before updating from v0.20 so I hadn't noticed. I delete it and it had the same issue. Rebuilt aeskeydb.bin and it and it went away again. The functionality of aeskeydb.bin does not seem to matter whether I leave it in the Decrypt9 folder or move it to the root (well, technically, copy it to the root and delete it from Decrypt9, since there is no "move" function yet). CTRNAND is indeed not an option when it gives this error, as you would expect. With the aeskeydb.bin in place, the first 16 bytes on that .bin file are E9 00 00 43 54 52 20 20 20 20 20 00 02 40 01 00 on the EUR and USA devices (I'm using "SYSNAND VIRTUAL" and the hex viewer to get that, if that matters -- makes little sense copying 1 GB of data to get 16 bytes after all).
Now, I used the files from the data_input.zip provided by the A9LH tutorial. Is it possible that part of the problem is that I should have dumped my own firm0, firm1, and secret sector files? I was under the impression that they must be all the same if a distributed copy can work in the first place, but I can extract them from EmuNAND (being it's a copy of my pre-A9LH SysNAND) and reinstall A9LH if it matters.
Last edited by Kazuma77,
Well, I've had the slot0x05KeyY.bin file on the device the entire time. So it can't be case 1. And Decrypt9 used the file to build a working aeskeydb.bin, so it can't be case 2 either. Actually, I've just confirmed my USA N3DS XL does the same. It's just that I had already created aeskeydb.bin before updating from v0.20 so I hadn't noticed. I delete it and it had the same issue. Rebuilt aeskeydb.bin and it and it went away again. The functionality of aeskeydb.bin does not seem to matter whether I leave it in the Decrypt9 folder or move it to the root (well, technically, copy it to the root and delete it from Decrypt9, since there is no "move" function yet). CTRNAND is indeed not an option when it gives this error, as you would expect. With the aeskeydb.bin in place, the first 16 bytes on that .bin file are E9 00 00 43 54 52 20 20 20 20 20 00 02 40 01 00 on the EUR and USA devices (I'm using "SYSNAND VIRTUAL" and the hex viewer to get that, if that matters -- makes little sense copying 1 GB of data to get 16 bytes after all).
Now, I used the files from the data_input.zip provided by the A9LH tutorial. Is it possible that part of the problem is that I should have dumped my own firm0, firm1, and secret sector files? I was under the impression that they must be all the same if a distributed copy can work in the first place, but I can extract them from EmuNAND (being it's a copy of my pre-A9LH SysNAND) and reinstall A9LH if it matters.
Well, actually I messed up loading from slot0x05keyY.bin and I think that is the cause. With the latest commit, could you compile fresh and try without the aeskeydb.bin (but with slot0x05keyY.bin, obviously)? It should work now.
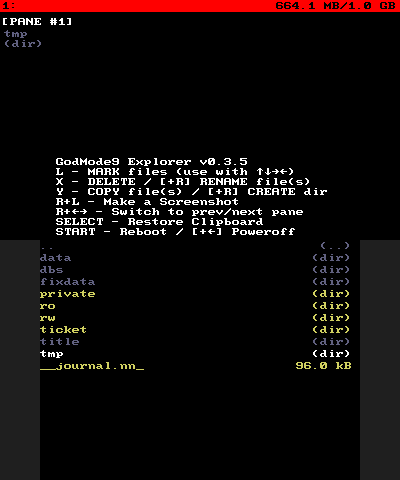
Here's a new major, stable release. This is new:
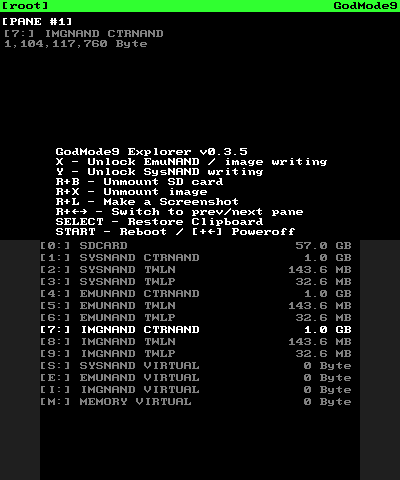
Also, to those of you who are not using this tool because you are too scared of it's possibilities... See that colored bar on top? As long as that is green, you have write permissions only for the SD card, meaning nothing bad can happen. Giving extended write permissions requries entering a button sequence. Even if the bar is yellow or red (for EmuNAND / SysNAND writing permissions), it is still in your hands, this tool won't do anything funny on it's own. If you can't handle this responsibility, keep away from this tool, otherwise there is nothing to be scared of.
- You can now mount NAND and FAT images and use them as additional drive(s)
- Hexviewer for files from any locations
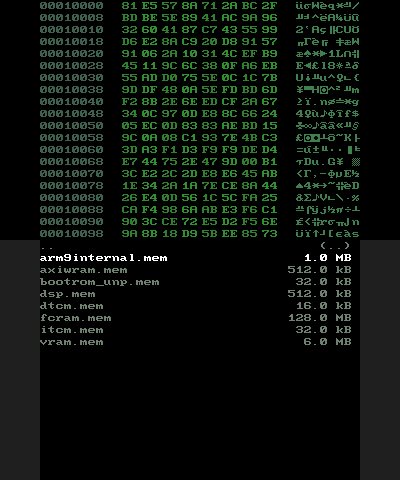
- Virtual Memory drive added (allows you to view and dump certain memory regions)
- Dual pane handling added, switch with R + (Right / Left)
- Vastly improved button react times on O3DS (thanks @AuroraWright)
- More useful info displayed in directory view
- Fixed filename input dialogue (this would fail on rare occasions)
- Fixed case sensitive renaming
- Some minor bugfixes
Also, to those of you who are not using this tool because you are too scared of it's possibilities... See that colored bar on top? As long as that is green, you have write permissions only for the SD card, meaning nothing bad can happen. Giving extended write permissions requries entering a button sequence. Even if the bar is yellow or red (for EmuNAND / SysNAND writing permissions), it is still in your hands, this tool won't do anything funny on it's own. If you can't handle this responsibility, keep away from this tool, otherwise there is nothing to be scared of.
Last edited by d0k3,
Well, actually I messed up loading from slot0x05keyY.bin and I think that is the cause. With the latest commit, could you compile fresh and try without the aeskeydb.bin (but with slot0x05keyY.bin, obviously)? It should work now.
I don't think I have the 3DS dev kit installed, just the PS3 one (even that's not updated -- the last time I used it was to help someone that was creating a Cinavia patch tool). Call me lazy I guess. It's probably not a good time to install it now either. I'm about to switch from an ATI card to an Nvidia. So I'm probably looking at a fresh Windows install (oh well, haven't been doing those as often as I should anyway). Besides, I've got someone wanting their PC looked at (typical malware infestation), so, not going to have much time today. If it's not too much trouble, can you upload another pre-compiled file?
Here's a new major, stable release. This is new:
View attachment 45547 View attachment 45548 View attachment 45549 View attachment 45555
- You can now mount NAND and FAT images and use them as additional drive(s)
- Hexviewer for files from any locations
- Virtual Memory drive added (allows you to view and dump certain memory regions)
- Dual pane handling added, switch with R + (Right / Left)
- Vastly improved button react times on O3DS (thanks @AuroraWright)
- More useful info displayed in directory view
- Fixed filename input dialogue (this would fail on rare occasions)
- Fixed case sensitive renaming
- Some minor bugfixes
Also, to those of you who are not using this tool because you are too scared of it's possibilities... See that colored bar on top? As long as that is green, you have write permissions only for the SD card, meaning nothing bad can happen. Giving extended write permissions requries entering a button sequence. Even if the bar is yellow or red (for EmuNAND / SysNAND writing permissions), it is still in your hands, this tool won't do anything funny on it's own. If you can't handle this responsibility, keep away from this tool, otherwise there is nothing to be scared of.
Damn, that was fast
See aboveI don't think I have the 3DS dev kit installed, just the PS3 one (even that's not updated -- the last time I used it was to help someone that was creating a Cinavia patch tool). Call me lazy I guess. It's probably not a good time to install it now either. I'm about to switch from an ATI card to an Nvidia. So I'm probably looking at a fresh Windows install (oh well, haven't been doing those as often as I should anyway). Besides, I've got someone wanting their PC looked at (typical malware infestation), so, not going to have much time today. If it's not too much trouble, can you upload another pre-compiled file?
@d0k3
Offtopic: Any chance of bringing https://github.com/d0k3/uncart up to date with a9lh compatibility?
@Shadowtrance uploaded a binary with nice purple font way back, but never provided the sources.
Offtopic: Any chance of bringing https://github.com/d0k3/uncart up to date with a9lh compatibility?

@Shadowtrance uploaded a binary with nice purple font way back, but never provided the sources.
No one asked for the source.@d0k3
Offtopic: Any chance of bringing https://github.com/d0k3/uncart up to date with a9lh compatibility?
@Shadowtrance uploaded a binary with nice purple font way back, but never provided the sources.
No one asked for the source.(hint, it's on my github and not much needs changing to work on a9lh).
Yea, I was looking at the change log and the last commit was in August, 2015. I'll compile it to see if it's the same. Thanks.
--------------------- MERGED ---------------------------
Yea, I was looking at the change log and the last commit was in August, 2015. I'll compile it to see if it's the same. Thanks.
Code:
arm-none-eabi-gcc -MMD -MP -MF /home/hle/src/uncart/brahma_loader/build/main.d -g -Wall -O3 -mword-relocations -fomit-frame-pointer -ffast-math -march=armv6k -mtune=mpcore -mfloat-abi=hard -I/home/hle/src/uncart/brahma_loader/include -I/home/hle/.bin/devkitPro/libctru/include -I/home/hle/src/uncart/brahma_loader/build -DPAYLOAD=\"Uncart.bin\" -DARM11 -D_3DS -DARM_ARCH -w -c /home/hle/src/uncart/brahma_loader/source/main.c -o main.o
/home/hle/src/uncart/brahma_loader/source/main.c: In function 'main':
/home/hle/src/uncart/brahma_loader/source/main.c:9:5: error: too many arguments to function 'hidInit'
hidInit(NULL);I'm not sure if this has anything to do with libctru, but is it updated for the latest libctru?
Speaking of CTRBM9, trying to load GodMod9 with it doesn't work. AuReiNand's payload chainloader works, though.Occasional failed boots on HBL are normal, as the Brahma entrypoint is not perfectly stable.
Sure there is! With A9LH installed, you have access to Select9 and CTR Boot Manager9. Without A9LH, you still have CTR Boot Manager (which you'd have to use as a HBL replacement). In general, Homebrew Launcher is a better entrypoint than MSET and A9LH > HBL > MSET.
Similar threads
- Replies
- 6
- Views
- 2K
- Replies
- 20
- Views
- 3K
Site & Scene News
New Hot Discussed
-
-
25K views
Wii U and 3DS online services shutting down today, but Pretendo is here to save the day
Today, April 8th, 2024, at 4PM PT, marks the day in which Nintendo permanently ends support for both the 3DS and the Wii U online services, which include co-op play...by ShadowOne333 179 -
21K views
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other... -
18K views
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we... -
17K views
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 96 -
14K views
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems... -
13K views
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 113 -
12K views
A prototype of the original "The Legend of Zelda" for NES has been found and preserved
Another video game prototype has been found and preserved, and this time, it's none other than the game that spawned an entire franchise beloved by many, the very...by ShadowOne333 31 -
10K views
Anbernic reveals specs details of pocket-sized RG28XX retro handheld
Anbernic is back with yet another retro handheld device. The upcoming RG28XX is another console sporting the quad-core H700 chip of the company's recent RG35XX 2024... -
10K views
Nintendo "Indie World" stream announced for April 17th, 2024
Nintendo has recently announced through their social media accounts that a new Indie World stream will be airing tomorrow, scheduled for April 17th, 2024 at 7 a.m. PT...by ShadowOne333 53 -
10K views
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another...
-
-
-
179 replies
Wii U and 3DS online services shutting down today, but Pretendo is here to save the day
Today, April 8th, 2024, at 4PM PT, marks the day in which Nintendo permanently ends support for both the 3DS and the Wii U online services, which include co-op play...by ShadowOne333 -
113 replies
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 -
97 replies
The first retro emulator hits Apple's App Store, but you should probably avoid it
With Apple having recently updated their guidelines for the App Store, iOS users have been left to speculate on specific wording and whether retro emulators as we...by Scarlet -
96 replies
Delta emulator now available on the App Store for iOS
The time has finally come, and after many, many years (if not decades) of Apple users having to side load emulator apps into their iOS devices through unofficial...by ShadowOne333 -
80 replies
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other...by Chary -
77 replies
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems...by Chary -
55 replies
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal...by relauby -
55 replies
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another...by Chary -
53 replies
Nintendo "Indie World" stream announced for April 17th, 2024
Nintendo has recently announced through their social media accounts that a new Indie World stream will be airing tomorrow, scheduled for April 17th, 2024 at 7 a.m. PT...by ShadowOne333 -
52 replies
The FCC has voted to restore net neutrality, reversing ruling from 2017
In 2017, the United States Federal Communications Commission (FCC) repealed net neutrality. At the time, it was a major controversy between internet service providers...by Chary
-
Popular threads in this forum
General chit-chat
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
-
 @
BigOnYa:
Anybody here have a Xbox series S and a series X, is the performance difference noticeable? Not worried about 4k. I have a series X but not a series S and was curious. (Reason- I was thinking of buying a series S for a second tv, for when grandkids come over, to keep them off my X)
@
BigOnYa:
Anybody here have a Xbox series S and a series X, is the performance difference noticeable? Not worried about 4k. I have a series X but not a series S and was curious. (Reason- I was thinking of buying a series S for a second tv, for when grandkids come over, to keep them off my X) -
-
-
-
-
-
-
-
-





