You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
D
Deleted User
Guest
Does anyone know if there is any loss of quality while converting BFSTM to BRSTM?
I have no idea if there is any B(x)STM editing tool. I've run into another dead end here. I need something that can silence certain channels, read any B(x)STM format (ANY, not every), and help me save the result.
Recommendations welcome.
You mean silencing any channel of a BxSTM audio file?
If so, then you can use a hex editor, for example, HxD, to just fill that specified channel section with zeros, then you should be good.
Last edited by ,
too late mediafire trolled you
Oh, right. So in Mario Kart 8, the .szs isn't a Yaz0 compressed SARC, but in other games, it is. I get it now. That's why the GitHub page says that, because it acknowledges the majority... ahh, revelations.
Nintendo uses the .szs extension to mean "Yaz0-compressed data," in general. Usually the data is a SARC archive, but there are games other than MK8 that use SZS to compress files of other types. One game even uses SZS for Yaz0-compressed font files (BFFNT).
How did you do that, could you please say it?Finally I've got Loadiine works in 5.5.1
LOL, no I didn't ...
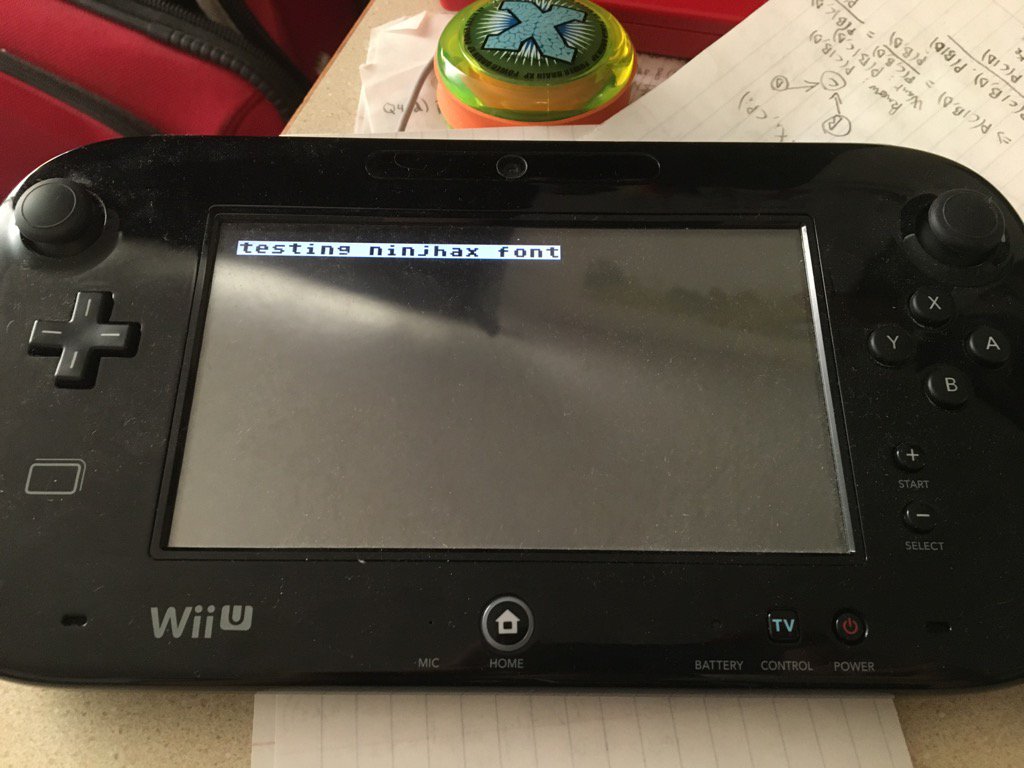
Please look at the white text...How did you do that, could you please say it?
Finally I've got Loadiine works in 5.5.1
LOL, no I didn't ...
Last edited by rw-r-r_0644,
How did you do that, could you please say it?
White text??, I see nothing there, what are u talking about, what can you see there?Please look at the white text...
highlight all the post.White text??, I see nothing there, what are u talking about, what can you see there?
I was talking about how Nikki's GitHub page said that .szs = Yaz0 + SARC archive, but MK8's .szs's weren't SARC archives. She told me that in her reply to me before.Nintendo uses the .szs extension to mean "Yaz0-compressed data," in general. Usually the data is a SARC archive, but there are games other than MK8 that use SZS to compress files of other types. One game even uses SZS for Yaz0-compressed font files (BFFNT).
Also, any idea in which folder the BFFNT would be? Would be undescribably cool to make a custom font.
Do you have experience with it? If so, mind sharing the offsets for individual channels of a BFSTM?You mean silencing any channel of a BxSTM audio file?
If so, then you can use a hex editor, for example, HxD, to just fill that specified channel section with zeros, then you should be good.
You have to search them, not every song has the same length.If so, mind sharing the offsets for individual channels of a BFSTM?
Boot1 IV has been added to my talk page (before you get all excited, don't. the iv is only useful to decrypt the first 0x10 bytes, given the correct key. we're still missing the boot1 key)
Anybody have issues with super Mario 3d world? It won't progress past the "you can also play with these controllers" screen. I'm using loadiine v3 on 5.4.
Boot1 IV has been added to my talk page (before you get all excited, don't. the iv is only useful to decrypt the first 0x10 bytes, given the correct key. we're still missing the boot1 key)
Wut, was it possible to bruteforce the IV? Isn't the first 0x10 bytes encrypted with the key too, and not just XORed with the IV? (Assuming they use AES(or some other encryption) in CBC mode)
Wut, was it possible to bruteforce the IV? Isn't the first 0x10 bytes encrypted with the key too, and not just XORed with the IV? (Assuming they use AES(or some other encryption) in CBC mode)
Presumably, it was reverse-engineered out of boot0, which has been possible to dump for almost 2 years.
yep, and the bootrom contains the expresso iv, whilst IOSU contains the starbuck iv (while we are talking about hardcoded crapPresumably, it was reverse-engineered out of boot0, which has been possible to dump for almost 2 years.
So sans, what could the great papyrus do with this?yep, and the bootrom contains the expresso iv, whilst IOSU contains the starbuck iv (while we are talking about hardcoded crap)
decrypt shit and use it to "time-travel"So sans, what could the great papyrus do with this?
Ohhhkay. Could papyrus test if need be? My Spaghetti will make you not Regretti.decrypt shit and use it to "time-travel"
Similar threads
- Replies
- 0
- Views
- 2K
- Replies
- 45
- Views
- 31K
- Replies
- 2
- Views
- 2K
- Replies
- 5
- Views
- 1K
Site & Scene News
New Hot Discussed
-
-
20K views
Majora’s Mask PC port 2Ship2Harkinian gets its first release
After several months of work, the Harbour Masters 64 team have released their first public build of 2Ship2Harkinian, a feature-rich Majora's Mask PC port. This comes... -
19K views
Mario Builder 64 is the N64's answer to Super Mario Maker
With the vast success of Super Mario Maker and its Switch sequel Super Mario Maker 2, Nintendo fans have long been calling for "Maker" titles for other iconic genres... -
19K views
Modders hint at potential kernel exploit hack for Xbox One consoles
It's been a while since Microsoft released the Xbox One, and despite its age, there haven't been any reliable softmod methods to hack the console. Until now. A post... -
17K views
The founder of Oculus is releasing a $199 FPGA Game Boy system
Palmer Luckey is known for his pursuits into the world of virtual reality, having founded Oculus and designed the Rift VR headset. Prior to the $2 billion dollar... -
14K views
Nintendo takes down the Breath of the Wild randomizer mod from Gamebanana
Another day, another Nintendo DMCA takedown against fan-made content. Just a few minutes ago, Nintendo issued a DMCA takedown notice against a widely known and...by ShadowOne333 104 -
14K views
The Kingdom Hearts games are coming to Steam
After a little more than three years of exclusivity with the Epic Games Store, Square Enix has decided to bring their beloved Kingdom Hearts franchise to Steam. The... -
12K views
Select PlayStation 2 games are coming to PlayStation 5
Sony is once more attempting to reintroduce players to their older library of games by re-releasing classic PlayStation 2 titles onto the PlayStation Store. During... -
11K views
Skyward Sword HD randomizer announced with release date and trailer
Skyward Sword is a divisive title in the Zelda series. Hailed with praise at launch with a 93 Metacritic average, the game since received criticism for the... -
10K views
PlayStation State of Play May 2024 showcase - God of War: Ragnarok coming to PC
The latest State of Play is here. This is PlayStation's Summer showcase, providing updates to new updates on upcoming games and brand new reveals. The 35-minute... -
9K views
Nintendo acquires company behind Mortal Kombat 1 and Hogwarts Legacy ports on Switch, "Shiver Entertainment Inc."
Nintendo is having quite the successful console generation with the Nintendo Switch, and with the follow-up to the Switch already on the horizon confirmed by...by ShadowOne333 48
-
-
-
169 replies
The founder of Oculus is releasing a $199 FPGA Game Boy system
Palmer Luckey is known for his pursuits into the world of virtual reality, having founded Oculus and designed the Rift VR headset. Prior to the $2 billion dollar...by Chary -
118 replies
Modders hint at potential kernel exploit hack for Xbox One consoles
It's been a while since Microsoft released the Xbox One, and despite its age, there haven't been any reliable softmod methods to hack the console. Until now. A post...by Chary -
108 replies
Majora’s Mask PC port 2Ship2Harkinian gets its first release
After several months of work, the Harbour Masters 64 team have released their first public build of 2Ship2Harkinian, a feature-rich Majora's Mask PC port. This comes...by Scarlet -
104 replies
Nintendo takes down the Breath of the Wild randomizer mod from Gamebanana
Another day, another Nintendo DMCA takedown against fan-made content. Just a few minutes ago, Nintendo issued a DMCA takedown notice against a widely known and...by ShadowOne333 -
91 replies
The Kingdom Hearts games are coming to Steam
After a little more than three years of exclusivity with the Epic Games Store, Square Enix has decided to bring their beloved Kingdom Hearts franchise to Steam. The...by Chary -
79 replies
Select PlayStation 2 games are coming to PlayStation 5
Sony is once more attempting to reintroduce players to their older library of games by re-releasing classic PlayStation 2 titles onto the PlayStation Store. During...by Chary -
66 replies
Mario Builder 64 is the N64's answer to Super Mario Maker
With the vast success of Super Mario Maker and its Switch sequel Super Mario Maker 2, Nintendo fans have long been calling for "Maker" titles for other iconic genres...by Scarlet -
64 replies
PlayStation State of Play May 2024 showcase - God of War: Ragnarok coming to PC
The latest State of Play is here. This is PlayStation's Summer showcase, providing updates to new updates on upcoming games and brand new reveals. The 35-minute...by Chary -
62 replies
Summer Game Fest 2024 coverage - Civilization VII announced
E3 may be gone, but it's not forgotten, as the trend of a massive Summer video game showcase still lives on in the form of the Summer Game Fest. Promising two hour of...by Chary -
55 replies
Doom for SNES full source code released by former Sculptured Software employees
The complete source code for the Super Nintendo Entertainment System (SNES) version of Doom has been released on archive.org. Although some of the code was partially...by shaunj66
-
Popular threads in this forum
General chit-chat
-
 Xdqwerty
Loading…what are you looking at?
Xdqwerty
Loading…what are you looking at? -
 K3Nv2
Loading…
K3Nv2
Loading… -
 NinStar
Loading…
NinStar
Loading… -
 BakerMan
Loading…I rather enjoy a life of taking it easy. I haven't reached that life yet though.
BakerMan
Loading…I rather enjoy a life of taking it easy. I haven't reached that life yet though.
-
-
-
-
-
-
-
-
-
-
-
 @
Xdqwerty:
@SylverReZ, the first one is a dnb song i put and the second one is a song that became popular due to gd that i really like
@
Xdqwerty:
@SylverReZ, the first one is a dnb song i put and the second one is a song that became popular due to gd that i really like -
 @
BakerMan:
i would say if it's not for a video game but it's in a video game, it counts if it's not a music game+1
@
BakerMan:
i would say if it's not for a video game but it's in a video game, it counts if it's not a music game+1
so it counts for hotline miami and geometry dash, but not just dance or beat saber -
-
-
-
-
-
-
-
-
-
-
-
-