Does this site even work?I need to find how to edit the UID - You can write to an amiibo or tag by using AmiiWrite.
http://amiibo.codlab.eu/amiibo.apk
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
That link doesn't work, just gives me a timeout.
That link doesn't work, just gives me a timeout.
@pokasmax posted it here: https://gbatemp.net/threads/save-and-restore-your-amiibos-on-android.403072/
You can clone the repo and compile it yourself: https://github.com/codlab/amiibo
And download the android SDK?@pokasmax posted it here: https://gbatemp.net/threads/save-and-restore-your-amiibos-on-android.403072/
You can clone the repo and compile it yourself: https://github.com/codlab/amiibo
Nah, better wait for the site to come back...
Why not just use Mifare++ Ultralight? That's what I use for all my reading, editing, and writing.And download the android SDK?
Nah, better wait for the site to come back...
One other small problem, I'm not sure how to generate the 32 byte xorpad. The pastebin post a while back with all the keys in it had the AES IV and KeyY needed to create the xorpad, and I feel like it should be fairly straight forward with Decrypt9, but I'm not really that familiar with xorpad generation. Has anybody else done this before?
D
Deleted User
Guest
You're trying to encrypt and decrypt, aren't you? Get an API key from the guy and use amiicli.sh 
oorrr just use his online thing.You're trying to encrypt and decrypt, aren't you? Get an API key from the guy and use amiicli.sh
D
Deleted User
Guest
Set1 keys:
1st 3 are DEVs data (and they are all correct).
2nd 3 are DEVs data and HMAC key is 830E75...
Set2 keys:
1st 3 are retail data and HMAC key is 1D164B...
2nd 3 are retail data and HMAC key is 7F752D...
As stated, algo for xorpad: AES-128 CTR mode: 1st key is AES KeyY, 2nd key is AES IV.
Resulting xorpads are:
495B197A5B802055AEE8AE8EA08E053233C770A8A99E6DAD6F1CA01FE3618022 (for DEVs)
044917DC76B49640D6F83939960FAED4EF392FAAB21428AA21FB54E545054766 (for retail)
xorpads ARE NOT copyrighted materials... they are just... xorpads, so no reason to censor them
Everything started from this great job.
1st 3 are DEVs data (and they are all correct).
2nd 3 are DEVs data and HMAC key is 830E75...
Set2 keys:
1st 3 are retail data and HMAC key is 1D164B...
2nd 3 are retail data and HMAC key is 7F752D...
As stated, algo for xorpad: AES-128 CTR mode: 1st key is AES KeyY, 2nd key is AES IV.
Resulting xorpads are:
495B197A5B802055AEE8AE8EA08E053233C770A8A99E6DAD6F1CA01FE3618022 (for DEVs)
044917DC76B49640D6F83939960FAED4EF392FAAB21428AA21FB54E545054766 (for retail)
xorpads ARE NOT copyrighted materials... they are just... xorpads, so no reason to censor them
Everything started from this great job.
Last edited by asper,
Thank you very much, you just released the last key needed (well, the xorpads). I couldn't find any documentation about how they work, so I couldn't calculate them with the keys. Now I only have to find the way to use the keys and the xorpad with amiibo-toolsSet1 keys:
1st 3 are DEVs data (and they are all correct).
2nd 3 are DEVs data and HMAC key is 830E75...
Set2 keys:
1st 3 are retail data and HMAC key is 1D164B...
2nd 3 are retail data and HMAC key is 7F752D...
As stated, algo for xorpad: AES-128 CTR mode: 1st key is AES KeyY, 2nd key is AES IV.
Resulting xorpads are:
495B197A5B802055AEE8AE8EA08E053233C770A8A99E6DAD6F1CA01FE3618022 (for DEVs)
044917DC76B49640D6F83939960FAED4EF392FAAB21428AA21FB54E545054766 (for retail)
xorpads ARE NOT copyrighted materials... they are just... xorpads, so no reason to censor them
Everything started from this great job.
EDIT: Which set is the developer one and which is the retail?
Last edited by fraret,
Set1 keys:
1st 3 are DEVs data (and they are all correct).
2nd 3 are DEVs data and HMAC key is 830E75...
Set2 keys:
1st 3 are retail data and HMAC key is 1D164B...
2nd 3 are retail data and HMAC key is 7F752D...
As stated, algo for xorpad: AES-128 CTR mode: 1st key is AES KeyY, 2nd key is AES IV.
Resulting xorpads are:
495B197A5B802055AEE8AE8EA08E053233C770A8A99E6DAD6F1CA01FE3618022 (for DEVs)
044917DC76B49640D6F83939960FAED4EF392FAAB21428AA21FB54E545054766 (for retail)
xorpads ARE NOT copyrighted materials... they are just... xorpads, so no reason to censor them
Everything started from this great job.
Awesome; thanks asper. Out of curiosity, how did you generate the xorpads?
Last edited by Supercool330,
lol, I figured. I was curious on how you interacted with the AES module. Did you use decrypt9 somehow, or something else?Maybe using a 3ds ?
well guys this is really awesome XD I want to do some :v there are no way they can be blocked, right? XD
Also... there is a way to do the same with skylanders/disney stuff? °w°
Also... there is a way to do the same with skylanders/disney stuff? °w°
Could someone help out please?
I have created a.bin file of Mario using amiiqo.
I have successfully run it through the online decrypt-er and I am able to read the contents of the file.
What I am trying to do is use the amiitool to do the same decrypting. I have a binary keys file 80 bytes in length using the info I have found here, however amiitool says simply says
"!!! WARNING !!!: Tag signature was NOT valid".
Any idea what I am doing wrong?
I have created a.bin file of Mario using amiiqo.
I have successfully run it through the online decrypt-er and I am able to read the contents of the file.
What I am trying to do is use the amiitool to do the same decrypting. I have a binary keys file 80 bytes in length using the info I have found here, however amiitool says simply says
"!!! WARNING !!!: Tag signature was NOT valid".
Any idea what I am doing wrong?
Your keyfile is correct?Could someone help out please?
I have created a.bin file of Mario using amiiqo.
I have successfully run it through the online decrypt-er and I am able to read the contents of the file.
What I am trying to do is use the amiitool to do the same decrypting. I have a binary keys file 80 bytes in length using the info I have found here, however amiitool says simply says
"!!! WARNING !!!: Tag signature was NOT valid".
Any idea what I am doing wrong?
Please post MD5 or SHA1 of your keyfile for check it
looking in a hex editor this is what the last 4 columns look like.
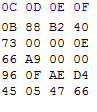
I have basically tried everything from a pastebin file and the xorpads, hopefully it is just a case of finding the right combination.
I have basically tried everything from a pastebin file and the xorpads, hopefully it is just a case of finding the right combination.
Similar threads
- Replies
- 43
- Views
- 22K
-
- Article
- Replies
- 16
- Views
- 12K
- Replies
- 1
- Views
- 5K
- Article
- Replies
- 2
- Views
- 18K
Site & Scene News
New Hot Discussed
-
-
20K views
Majora’s Mask PC port 2Ship2Harkinian gets its first release
After several months of work, the Harbour Masters 64 team have released their first public build of 2Ship2Harkinian, a feature-rich Majora's Mask PC port. This comes... -
18K views
Mario Builder 64 is the N64's answer to Super Mario Maker
With the vast success of Super Mario Maker and its Switch sequel Super Mario Maker 2, Nintendo fans have long been calling for "Maker" titles for other iconic genres... -
17K views
Modders hint at potential kernel exploit hack for Xbox One consoles
It's been a while since Microsoft released the Xbox One, and despite its age, there haven't been any reliable softmod methods to hack the console. Until now. A post... -
16K views
The founder of Oculus is releasing a $199 FPGA Game Boy system
Palmer Luckey is known for his pursuits into the world of virtual reality, having founded Oculus and designed the Rift VR headset. Prior to the $2 billion dollar... -
14K views
Ubisoft reveals 'Assassin's Creed Shadows' which is set to launch later this year
Ubisoft has today officially revealed the next installment in the Assassin's Creed franchise: Assassin's Creed Shadows. This entry is set in late Sengoku-era Japan... -
14K views
Nintendo takes down the Breath of the Wild randomizer mod from Gamebanana
Another day, another Nintendo DMCA takedown against fan-made content. Just a few minutes ago, Nintendo issued a DMCA takedown notice against a widely known and...by ShadowOne333 104 -
14K views
RetroArch is now available in the Apple Store for iOS devices
Another day, another great emulator that makes its way into the Apple Store for more users to enjoy. With Apple opening its store up to videogame emulators earlier...by ShadowOne333 58 -
14K views
The Kingdom Hearts games are coming to Steam
After a little more than three years of exclusivity with the Epic Games Store, Square Enix has decided to bring their beloved Kingdom Hearts franchise to Steam. The... -
11K views
Select PlayStation 2 games are coming to PlayStation 5
Sony is once more attempting to reintroduce players to their older library of games by re-releasing classic PlayStation 2 titles onto the PlayStation Store. During... -
11K views
Skyward Sword HD randomizer announced with release date and trailer
Skyward Sword is a divisive title in the Zelda series. Hailed with praise at launch with a 93 Metacritic average, the game since received criticism for the...
-
-
-
169 replies
The founder of Oculus is releasing a $199 FPGA Game Boy system
Palmer Luckey is known for his pursuits into the world of virtual reality, having founded Oculus and designed the Rift VR headset. Prior to the $2 billion dollar...by Chary -
108 replies
Modders hint at potential kernel exploit hack for Xbox One consoles
It's been a while since Microsoft released the Xbox One, and despite its age, there haven't been any reliable softmod methods to hack the console. Until now. A post...by Chary -
108 replies
Majora’s Mask PC port 2Ship2Harkinian gets its first release
After several months of work, the Harbour Masters 64 team have released their first public build of 2Ship2Harkinian, a feature-rich Majora's Mask PC port. This comes...by Scarlet -
104 replies
Nintendo takes down the Breath of the Wild randomizer mod from Gamebanana
Another day, another Nintendo DMCA takedown against fan-made content. Just a few minutes ago, Nintendo issued a DMCA takedown notice against a widely known and...by ShadowOne333 -
98 replies
Ubisoft reveals 'Assassin's Creed Shadows' which is set to launch later this year
Ubisoft has today officially revealed the next installment in the Assassin's Creed franchise: Assassin's Creed Shadows. This entry is set in late Sengoku-era Japan...by Prans -
91 replies
The Kingdom Hearts games are coming to Steam
After a little more than three years of exclusivity with the Epic Games Store, Square Enix has decided to bring their beloved Kingdom Hearts franchise to Steam. The...by Chary -
77 replies
Select PlayStation 2 games are coming to PlayStation 5
Sony is once more attempting to reintroduce players to their older library of games by re-releasing classic PlayStation 2 titles onto the PlayStation Store. During...by Chary -
66 replies
Mario Builder 64 is the N64's answer to Super Mario Maker
With the vast success of Super Mario Maker and its Switch sequel Super Mario Maker 2, Nintendo fans have long been calling for "Maker" titles for other iconic genres...by Scarlet -
64 replies
PlayStation State of Play May 2024 showcase - God of War: Ragnarok coming to PC
The latest State of Play is here. This is PlayStation's Summer showcase, providing updates to new updates on upcoming games and brand new reveals. The 35-minute...by Chary -
62 replies
Summer Game Fest 2024 coverage - Civilization VII announced
E3 may be gone, but it's not forgotten, as the trend of a massive Summer video game showcase still lives on in the form of the Summer Game Fest. Promising two hour of...by Chary
-
Popular threads in this forum
General chit-chat
- No one is chatting at the moment.
-
-
-
-
-
-
-
-
 @
K3Nv2:
Ffs papa brought back the cheeseburger pizza it's like the only decent pie they had since the 80s
@
K3Nv2:
Ffs papa brought back the cheeseburger pizza it's like the only decent pie they had since the 80s -
 @
BigOnYa:
I'm not a fan of papa johns, but that does sound good. We hardly order out pizza, I like making my own, but when we do its donatoes
@
BigOnYa:
I'm not a fan of papa johns, but that does sound good. We hardly order out pizza, I like making my own, but when we do its donatoes -
-
-
-
-
-
 @
BakerMan:
guys should i make a new thread and just count the amount of posts until kyle, luke or leo joins the thread for fun?
@
BakerMan:
guys should i make a new thread and just count the amount of posts until kyle, luke or leo joins the thread for fun? -
 @
BakerMan:
kyle's fine, just waiting for that wario joke
@
BakerMan:
kyle's fine, just waiting for that wario joke
luke and leo though, they yap until the thread's enjoyability is about halved -
-
-
-
-
-
-
-
-






