So I have a short thought some time ago about a possibility of a ROM hack or something that gives DS/DSi access to modern SSL/TLS websites. I'm curious about it and if it's possible.
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
- Thread starter Beta-Alexis128
- Start date
- Views 2,647
- Replies 14
Yeah, I'm pretty sure it's possible.
Though it depends on where to get the certificates, as well as which ones to use.
Though it depends on where to get the certificates, as well as which ones to use.
im working on it. i extracted the dsi browser rom and found that the certificates are located in a folder labeled "ca" and i found that 14 of the certificates are expired so im going to try to find newer ones to replace them. hopefully it works
What is in the certificates and how could we somehow replace it with better and updated certificates?im working on it. i extracted the dsi browser rom and found that the certificates are located in a folder labeled "ca" and i found that 14 of the certificates are expired so im going to try to find newer ones to replace them. hopefully it works
i just looked looked for the name of the expired certificates and downloaded the newest certificate from the company who issued them. but now i have a issue that the certificates from google are in .crt or .pem and the ones from the rom are in .caWhat is in the certificates and how could we somehow replace it with better and updated certificates?
I find some source about the format itself: https://stackoverflow.com/questions/20501865/ssl-certificate-files-no-ca-filei just looked looked for the name of the expired certificates and downloaded the newest certificate from the company who issued them. but now i have a issue that the certificates from google are in .crt or .pem and the ones from the rom are in .ca
Can you rename it as .ca instead? Does it work?i just looked looked for the name of the expired certificates and downloaded the newest certificate from the company who issued them. but now i have a issue that the certificates from google are in .crt or .pem and the ones from the rom are in .ca
Also, what tools do you use?
So... I checked the files (Nintendo DS Browser) via Tinke 0.9.2 and I found out that the cert folder actually uses .pem files:i just looked looked for the name of the expired certificates and downloaded the newest certificate from the company who issued them. but now i have a issue that the certificates from google are in .crt or .pem and the ones from the rom are in .ca
So i tried changing the files with exact filenames. Either it's true that they hardcoded it to the code, which is not my expertise or something... The only thing bothering me is the DSi browser.It's always possible it might be hardcoded to only use those specific certificate file names and that it might not be able to just dynamically load new ones.
Some updates: I tried modifying the config file and recompile the DSi browser and that didn't do well. I used dslazy for this.
EDIT:
EDIT:
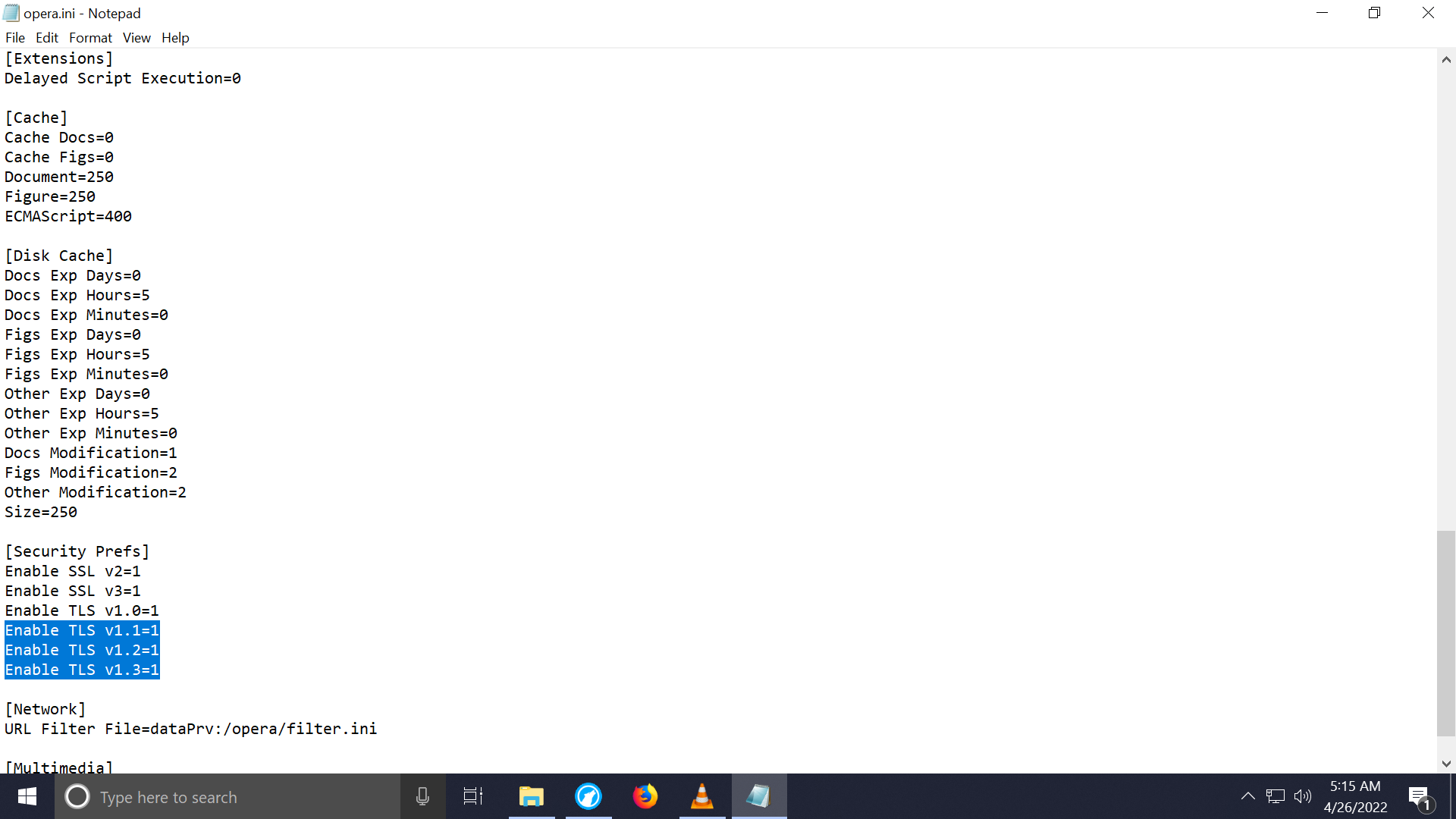
There may be a config setting for this but there is no guarantee that they are even implemented in the code in the first place. Higher TLS versions being enabled and implemented wouldn't really matter anyway, because the browser still needs valid (non-expired) certificates for those sites to load.
Pretty sure that was the case, I could recommend using some rendering proxy for this for now.There may be a config setting for this but there is no guarantee that they are even implemented in the code in the first place. Higher TLS versions being enabled and implemented wouldn't really matter anyway, because the browser still needs valid (non-expired) certificates for those sites to load.
You might want to use https://github.com/R-YaTian/TinkeDSi/releases, I don't think DSLazy would correctly repack the ROMSome updates: I tried modifying the config file and recompile the DSi browser and that didn't do well. I used dslazy for this.
EDIT:
View attachment 307537
That being said, I don't think you can just turn on TLS 1.3
Similar threads
- Replies
- 1
- Views
- 767
- Replies
- 2
- Views
- 942
Site & Scene News
New Hot Discussed
-
-
31K views
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other... -
27K views
New static recompiler tool N64Recomp aims to seamlessly modernize N64 games
As each year passes, retro games become harder and harder to play, as the physical media begins to fall apart and becomes more difficult and expensive to obtain. The... -
25K views
Nintendo officially confirms Switch successor console, announces Nintendo Direct for next month
While rumors had been floating about rampantly as to the future plans of Nintendo, the President of the company, Shuntaro Furukawa, made a brief statement confirming... -
23K views
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems... -
21K views
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 129 -
20K views
Name the Switch successor: what should Nintendo call its new console?
Nintendo has officially announced that a successor to the beloved Switch console is on the horizon. As we eagerly anticipate what innovations this new device will... -
17K views
A prototype of the original "The Legend of Zelda" for NES has been found and preserved
Another video game prototype has been found and preserved, and this time, it's none other than the game that spawned an entire franchise beloved by many, the very...by ShadowOne333 32 -
13K views
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal... -
13K views
Nintendo Switch Online adds two more Nintendo 64 titles to its classic library
Two classic titles join the Nintendo Switch Online Expansion Pack game lineup. Available starting April 24th will be the motorcycle racing game Extreme G and another... -
11K views
AYANEO officially launches the Pocket S, its next-generation Android gaming handheld
Earlier this year, AYANEO revealed details of its next Android-based gaming handheld, the AYANEO Pocket S. However, the actual launch of the device was unknown; that...
-
-
-
289 replies
Name the Switch successor: what should Nintendo call its new console?
Nintendo has officially announced that a successor to the beloved Switch console is on the horizon. As we eagerly anticipate what innovations this new device will...by Costello -
232 replies
Nintendo officially confirms Switch successor console, announces Nintendo Direct for next month
While rumors had been floating about rampantly as to the future plans of Nintendo, the President of the company, Shuntaro Furukawa, made a brief statement confirming...by Chary -
133 replies
New static recompiler tool N64Recomp aims to seamlessly modernize N64 games
As each year passes, retro games become harder and harder to play, as the physical media begins to fall apart and becomes more difficult and expensive to obtain. The...by Chary -
129 replies
Nintendo takes down Gmod content from Steam's Workshop
Nintendo might just as well be a law firm more than a videogame company at this point in time, since they have yet again issued their now almost trademarked usual...by ShadowOne333 -
92 replies
Ubisoft reveals 'Assassin's Creed Shadows' which is set to launch later this year
Ubisoft has today officially revealed the next installment in the Assassin's Creed franchise: Assassin's Creed Shadows. This entry is set in late Sengoku-era Japan...by Prans -
82 replies
Nintendo Switch firmware update 18.0.1 has been released
A new Nintendo Switch firmware update is here. System software version 18.0.1 has been released. This update offers the typical stability features as all other...by Chary -
80 replies
TheFloW releases new PPPwn kernel exploit for PS4, works on firmware 11.00
TheFlow has done it again--a new kernel exploit has been released for PlayStation 4 consoles. This latest exploit is called PPPwn, and works on PlayStation 4 systems...by Chary -
78 replies
"Nintendo World Championships: NES Edition", a new NES Remix-like game, launching July 18th
After rumour got out about an upcoming NES Edition release for the famed Nintendo World Championships, Nintendo has officially unveiled the new game, titled "Nintendo...by ShadowOne333 -
71 replies
DOOM has been ported to the retro game console in Persona 5 Royal
DOOM is well-known for being ported to basically every device with some kind of input, and that list now includes the old retro game console in Persona 5 Royal...by relauby -
65 replies
Microsoft is closing down several gaming studios, including Tango Gameworks and Arkane Austin
The number of layoffs and cuts in the videogame industry sadly continue to grow, with the latest huge layoffs coming from Microsoft, due to what MIcrosoft calls a...by ShadowOne333
-
Popular threads in this forum
General chit-chat
-
 Psionic Roshambo
Loading…
Psionic Roshambo
Loading…
-
-
-
-
 @
The Real Jdbye:
don't mind me, just liking all of SDIO's posts, they deserve it for https://gbatemp.net/threads/usb-partition-use-partitioned-usb-hdds-with-the-wii-u.656209/
@
The Real Jdbye:
don't mind me, just liking all of SDIO's posts, they deserve it for https://gbatemp.net/threads/usb-partition-use-partitioned-usb-hdds-with-the-wii-u.656209/ -
-
-
-
-
-
-
-
-
-
-
-
-
-
-
 @
BigOnYa:
Kinda silly. But cool I guess. Its like painting your 2by4 wood studs in a wall, before covering with drywall.+1
@
BigOnYa:
Kinda silly. But cool I guess. Its like painting your 2by4 wood studs in a wall, before covering with drywall.+1 -
 @
BigOnYa:
I heard a good one at the bar last night, made me think for sec. - "If you are cold, go stand in the corner, because corners are always 90 degrees."+2
@
BigOnYa:
I heard a good one at the bar last night, made me think for sec. - "If you are cold, go stand in the corner, because corners are always 90 degrees."+2 -
-
-
-
-



