Hi, I have a nand backup of an old 3ds I had. This 3ds got lost. Thank god I got the backup and now I've recovered everything, from old data, to the sd card encrypted game save data (using movable.sed and other tools).
Now, next, I'm looking to recover my Mii Maker and Mii Plaza save files. Using ninfs, I decrypted my nand.bin, and in the ctrnand_full.img I got to the sysdata folder where this save data is stored. Now, my final goal is to be able to open these saves on citra. On citra I already installed all system cias (system settings, mii plaza, mii maker, etc.) and I got the folder where they store the saves. When I go in the sysdata folder from citra, and enter the game folder, instead of a 00000000 file with no extension, there is a folder with the same name and a "editSaveData.bin" file inside. I suppose this is the decrypted version of the 00000000 file on my Nand sysdata.
Mii Maker:
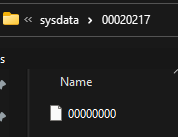
My Nand Backup:
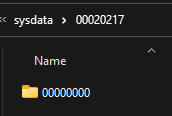
Citra:
I want to know if there is a way to decrypt this type of files without having to use the original 3ds (since I no longer have it). I tried using tools like three sd to transfer everything to citra, but I got stuck in the part where I need to execute the threeSDumper.gm9 on the 3ds (because I don't have it).
If you need me to clear something up to help you understand please let me know.
Any help would be appreciated
Now, next, I'm looking to recover my Mii Maker and Mii Plaza save files. Using ninfs, I decrypted my nand.bin, and in the ctrnand_full.img I got to the sysdata folder where this save data is stored. Now, my final goal is to be able to open these saves on citra. On citra I already installed all system cias (system settings, mii plaza, mii maker, etc.) and I got the folder where they store the saves. When I go in the sysdata folder from citra, and enter the game folder, instead of a 00000000 file with no extension, there is a folder with the same name and a "editSaveData.bin" file inside. I suppose this is the decrypted version of the 00000000 file on my Nand sysdata.
Mii Maker:
My Nand Backup:
Citra:
I want to know if there is a way to decrypt this type of files without having to use the original 3ds (since I no longer have it). I tried using tools like three sd to transfer everything to citra, but I got stuck in the part where I need to execute the threeSDumper.gm9 on the 3ds (because I don't have it).
If you need me to clear something up to help you understand please let me know.
Any help would be appreciated


